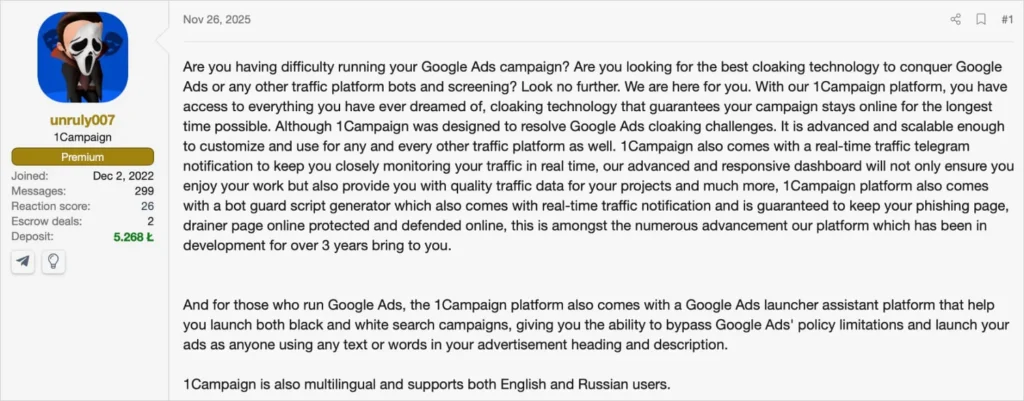
1Campaign Cloaking Service Powers Malicious Google Ads Evading Detection for Years

1Campaign cybercrime platform runs malicious Google Ads filtering real victims from researchers. DuppyMeister-operated service active 3+ years bypassing automated scanners. Real-time fraud scoring blocks 99.4% traffic showing white pages to cloud providers.
Service passes Google screening serving phishing, crypto drainers only to genuine users. User dashboard configures geo, ISP, device-based traffic routing. High-risk regions, VPNs, security vendors auto-blocked instantly.
Fraud scores 0-100 evaluate visitor legitimacy from infrastructure signals. Microsoft, Google Cloud, Tencent, OVH traffic flagged maximum risk immediately. 1,676 visitors yielded 10 targets (0.6% success rate).
Google Ads launcher impersonates brands bypassing policy limits. U.S., Canada, Netherlands, China, Germany, France, Japan, Hungary, Albania traffic observed. Realistic browser fingerprints needed for effective scanning.

Static URL analysis fails against dynamic cloaking. Human-mimic patterns evade behavioral detection. Manual reporting delays enable extended campaign lifespans.
Cloaking Filters Table
| Filter Type | Blocked Examples |
|---|---|
| Cloud Providers | Microsoft, Google, Tencent, OVH |
| High-Risk Geo | Security researcher heavy regions |
| VPN Detection | Commercial VPN IP ranges |
| Scanner Patterns | Automated browser fingerprints |
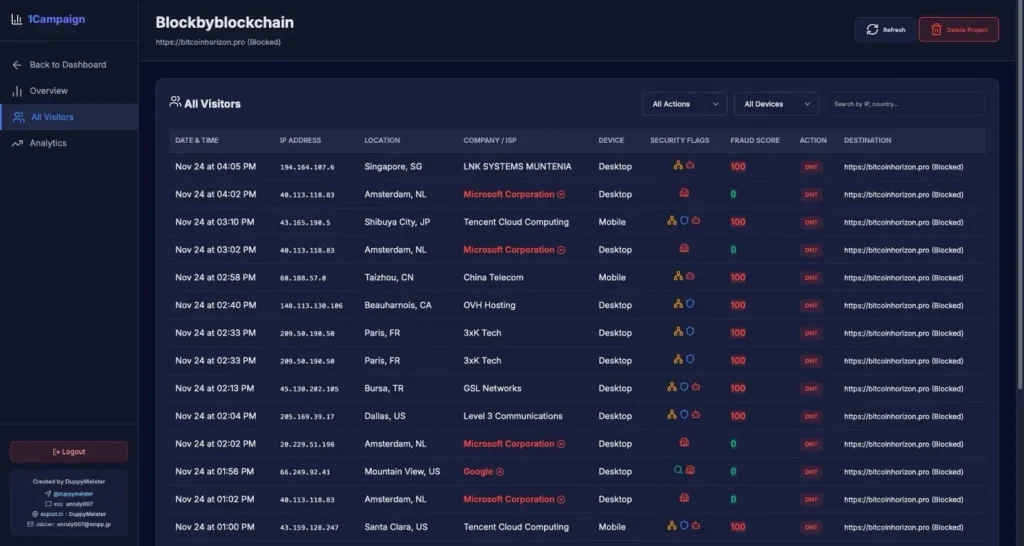
Observed Traffic Patterns
- Aggressive 99.4% visitor blocking
- 0.6% conversion to real victims
- Real-time fraud scoring 0-100
- Geo/ISP/device targeting
- Brand impersonation ads
Rotating IP pools, diverse user-agents needed for analysis. Static scanning ineffective against sophisticated cloaking.
Protection Measures
- Avoid promoted search results entirely
- Bookmark official software sites
- Verify URLs before credential entry
- Block known 1Campaign domains
- Deploy realistic fingerprint scanners
- Manual campaign reporting accelerates takedown
Google Ads remains persistent malware vector. Cloaking services extend malicious campaign durations dramatically. Victim reporting represents primary disruption mechanism.
FAQ
Cloaks malicious Google Ads from scanners showing content only to victims.
0.6% (10 real targets after 99.4% blocking).
0-100 scale based on infrastructure signals.
DuppyMeister running 3+ years undetected.
Real-time visitor profiling blocking cloud/security traffic.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more





User forum
0 messages