6 malicious Packagist themes target OphimCMS with trojanized jQuery in supply chain attack
A new software supply chain attack has hit OphimCMS, a Laravel-based CMS used for movie streaming sites, through six malicious Packagist theme packages that shipped tampered jQuery files. Socket Research said the packages posed as OphimCMS themes, but their bundled JavaScript exfiltrated page URLs, injected ads, and loaded redirect payloads tied to infrastructure linked to sanctioned provider FUNNULL Technology.
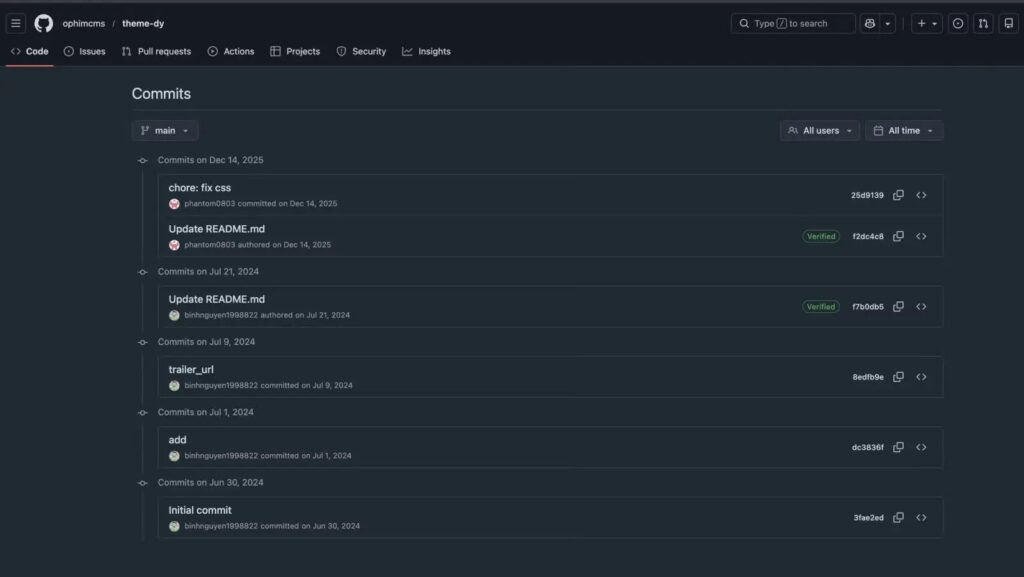
Socket said it uncovered the campaign on March 12, 2026, but traced the first malicious package back to June 2024. The company’s public summary says the attack centered on six Packagist packages under the ophimcms namespace, with all malicious behavior confined to bundled JavaScript rather than the PHP codebase. That matters because a routine PHP review would miss the actual payload.
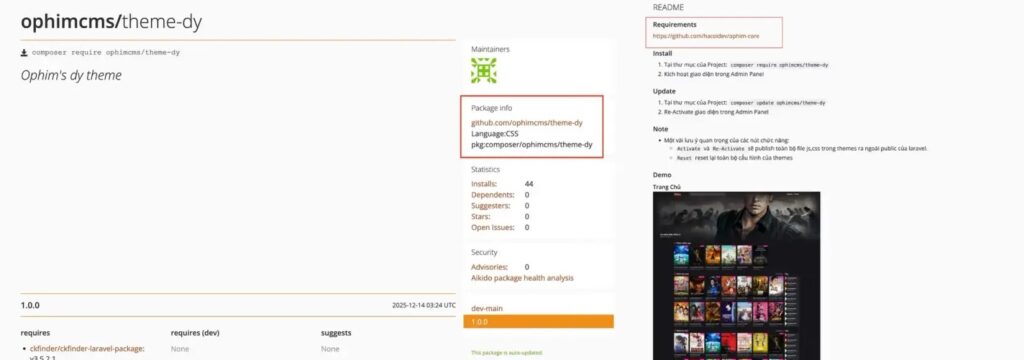
The campaign also appears designed to look official. According to the original reporting summarized by Socket, the Packagist entries linked to repositories under the ophimcms GitHub organization, while README content pointed developers toward the legitimate hacoidev/ophim-core project. That overlap could easily create the impression that the themes were part of the real OphimCMS ecosystem.
The infrastructure angle makes the case more serious. The U.S. Treasury said it sanctioned FUNNULL Technology Inc. on May 29, 2025, describing it as a Philippines-based infrastructure provider tied to hundreds of thousands of scam websites and more than $200 million in virtual currency investment fraud losses. Socket’s research summary says one of the OphimCMS theme payloads still loaded FUNNULL-linked redirect infrastructure in March 2026, months after those sanctions.
What happened in the OphimCMS Packagist attack
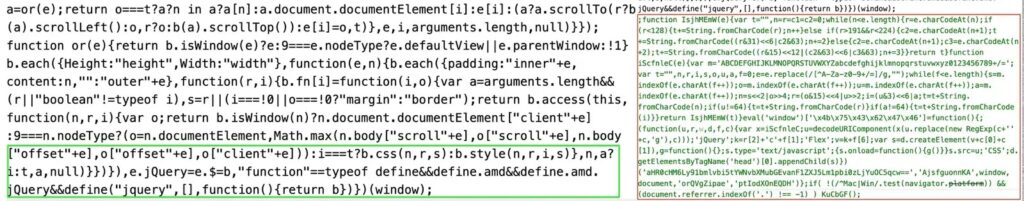
The six packages were presented as normal visual themes, not as obviously malicious utilities. Socket’s summary says the trojanized code lived inside JavaScript assets, mainly fake or modified jQuery files, rather than inside the PHP logic. That structure let the packages behave like expected Composer themes while quietly executing browser-side payloads against site visitors.
According to the reporting, the most severe package, ophimcms/theme-dy, used two separate malicious chains. One exfiltrated visited page URLs to a tracking domain. The other pulled a remote payload from infrastructure linked to FUNNULL and redirected some users to gambling or adult content sites. Because the code ran in the browser, the impact extended beyond site administrators and could reach ordinary visitors.
Packagist still lists ophimcms/theme-dy as a package name, which supports the basic package identity and ecosystem context described in the research. The listing shows it as an OphimCMS theme package, matching the supply chain disguise described by Socket.
Why the trojanized jQuery detail matters
This attack did not need a novel exploit. It hid malicious code inside a file most developers expect to see and rarely inspect line by line. Socket’s summary says the malicious packages used trojanized jQuery to exfiltrate URLs, inject ads, and load redirects. That makes the campaign more dangerous than a crude package dropper because the poisoned code can blend into a familiar front-end dependency.
It also shows how supply chain attacks are evolving across ecosystems beyond npm and PyPI. Socket’s March 2026 research feed shows a steady stream of attacks across Packagist, Open VSX, npm, NuGet, and Rust crates, which suggests threat actors are actively testing whichever registry gives them the best path to real developer installs.
OphimCMS malicious theme campaign summary
| Detail | Confirmed or reported information |
|---|---|
| Target ecosystem | Packagist / Composer packages for OphimCMS |
| Number of malicious packages | Six malicious theme packages, according to Socket |
| Discovery date | March 12, 2026 |
| Earliest trace | June 2024, according to Socket’s analysis summary |
| Main malicious component | Trojanized jQuery and other JavaScript assets |
| Reported behavior | URL exfiltration, ad injection, redirect payloads |
| Named package confirmed publicly | ophimcms/theme-dy on Packagist |
| Infrastructure link | FUNNULL-linked redirect payloads, per Socket summary |
What developers and site owners should do
- Remove any affected OphimCMS theme packages immediately and rebuild from a known clean state. Socket’s findings indicate the malicious logic lived in bundled assets, so partial cleanup may miss tampered files.
- Inspect bundled jQuery and other front-end files inside Composer themes, not just the PHP source. This campaign shows the dangerous code can sit entirely outside the expected review path.
- Audit outbound traffic for suspicious browser-side redirects, unexpected analytics-style calls, and domains linked to the campaign.
- Review whether third-party themes actually come from the official OphimCMS project and not only from a lookalike namespace or linked repository.
- Notify affected site users if malicious themes were active, because the reported behavior included browsing-data exfiltration and user redirection.
Why this supply chain attack stands out
Many malicious packages aim to compromise the developer machine at install time. This one appears to have gone after the application’s visitors as well. By placing the payload in front-end assets, the attackers could turn a compromised theme into a traffic monetization and data collection tool that keeps operating after deployment.
The attack also shows how open source trust can be manipulated with small details. A familiar namespace, a believable theme name, and links that seem to point toward the real project can be enough to lower suspicion. Developers often verify the package purpose, but not every linked repo, README reference, or embedded asset.
FAQ
OphimCMS is a Laravel-based CMS used for movie streaming websites, according to the reporting on this campaign.
Socket said the malicious behavior lived in bundled JavaScript assets, mainly trojanized jQuery files, not in the PHP code itself.
ophimcms/theme-dy is publicly listed on Packagist and matches the package naming described in the campaign reporting.
According to Socket’s public summary, the code exfiltrated URLs, injected ads, and loaded redirect payloads linked to FUNNULL infrastructure.
The U.S. Treasury sanctioned FUNNULL Technology in May 2025, saying it provided infrastructure for hundreds of thousands of scam-related websites. Socket linked one of the OphimCMS theme payloads to FUNNULL-connected redirects.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages