700+ Next.js hosts hit in React2Shell campaign as attackers steal cloud and database secrets

A large-scale credential theft campaign has compromised more than 700 internet-facing hosts by exploiting React2Shell, the remote code execution flaw tracked as CVE-2025-55182. Cisco Talos says the operation, which it tracks as UAT-10608, uses the bug to break into vulnerable web applications and then run an automated script that steals secrets from the server.
The campaign mainly targets applications built with React Server Components, especially exposed Next.js deployments that did not patch after the December 2025 disclosures. Talos says the attackers use automated scanning to find targets, exploit the flaw without authentication, and then pull credentials from local files, cloud metadata, shell history, and live application environments.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
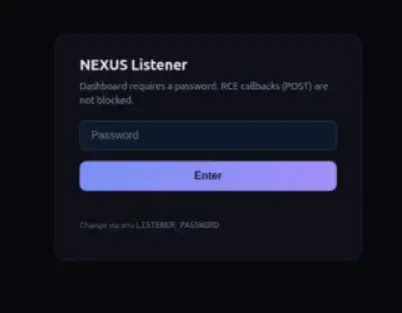
The scale looks serious. Talos says its visibility into the attackers’ own “NEXUS Listener” dashboard showed 766 compromised hosts in a 24-hour period, spread across regions and cloud providers. That figure supports the broad claim that more than 700 hosts were hit, but it reflects what Talos observed in that panel rather than a full global count of every affected server.
Why React2Shell remains dangerous
React2Shell is a pre-authentication remote code execution flaw in React Server Components. React disclosed CVE-2025-55182 on December 3, 2025, and said affected packages unsafely deserialize payloads sent to Server Function endpoints. React rated the issue CVSS 10.0 and warned that some apps could still be vulnerable even if they did not explicitly expose React Server Function endpoints.
Next.js also published a downstream advisory because the framework uses the affected React components. Vercel said the upstream React issue affected Next.js applications using the App Router, and later clarified that two additional React Server Components issues found afterward did not enable remote code execution, while the original React2Shell fix remained effective.
That timing matters because the current campaign appears to exploit laggards rather than a new zero-day. The flaw has been public and patchable since December 2025, which means the attackers likely succeeded against exposed apps that either missed the upgrade window or remained reachable with vulnerable code paths in production.
What the attackers steal after exploitation
Talos says the post-exploitation script focuses on credentials and secrets that can unlock more systems. According to the report, the attackers harvested database credentials from more than 90 percent of observed victims, private SSH keys from nearly 80 percent, plus AWS credentials, Stripe API keys, GitHub tokens, Kubernetes secrets, Docker configurations, and shell history.
The researchers say the attackers then organize stolen data through a custom web panel called NEXUS Listener. That matters because it shows this was not a smash-and-grab intrusion. The operation appears structured for repeatable credential harvesting at scale, with tooling built to collect, sort, and reuse secrets from many victims quickly.

The practical risk goes well beyond one compromised web app. A stolen database password can expose customer records. A stolen SSH key can open lateral movement paths. A live cloud credential can let attackers pivot into infrastructure, storage, and compute resources. A GitHub token can help tamper with source code or CI pipelines. Those follow-on risks flow directly from the kinds of secrets Talos says the attackers collected.
React2Shell campaign at a glance
| Item | Verified detail |
|---|---|
| Threat cluster | UAT-10608 |
| Initial access | CVE-2025-55182, also called React2Shell |
| Main target type | Vulnerable apps using React Server Components, especially Next.js App Router deployments |
| Observed victim count | 766 hosts in Talos’s view of the attacker dashboard |
| Main theft focus | Database credentials, SSH keys, cloud secrets, GitHub tokens, Stripe keys |
| Attack style | Automated scanning, exploitation, then scripted credential harvesting |
| Key management panel | NEXUS Listener |
What organizations should do now
- Patch React and Next.js immediately to the fixed versions listed in the official advisories.
- Rotate database passwords, SSH keys, cloud credentials, API keys, and GitHub tokens if a server may have been exposed before patching. This step follows directly from the types of data Talos says the attackers stole.
- Restrict access to cloud metadata services and review whether workloads can still pull credentials too easily from the instance environment. Google Cloud specifically published mitigation guidance after the React2Shell disclosures.
- Hunt for suspicious background scripts, unexplained outbound connections, and credential access patterns on patched hosts, because patching stops new exploitation but does not remove a foothold from previously compromised machines. This is a defensive inference supported by Talos’s post-exploitation findings.
- Treat any internet-facing Next.js app that stayed unpatched since December 2025 as high priority for review, especially if it handled payments, source code, or cloud administration.
FAQ
React2Shell is the name commonly used for CVE-2025-55182, a pre-authentication remote code execution bug in React Server Components. React said the issue comes from unsafe deserialization of payloads sent to Server Function endpoints.
The root issue came from React Server Components, but Next.js apps using the affected components were exposed downstream. Vercel tracked the Next.js impact separately under CVE-2025-66478 before marking it as downstream to the upstream React flaw.
Cisco Talos said it observed 766 compromised hosts through the attackers’ NEXUS Listener dashboard in a 24-hour window. That supports the “700+” figure, but it should be read as an observed slice of the operation, not a guaranteed full total of every victim worldwide.
Talos says the attackers stole database credentials, SSH private keys, AWS credentials, Stripe keys, GitHub tokens, Kubernetes secrets, Docker configurations, and other valuable secrets from compromised hosts.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages