7,500 Magento sites hit in mass defacement campaign tied to suspected file upload flaw

More than 7,500 Magento-powered websites have been caught in a large defacement campaign that has spread across roughly 15,000 hostnames since February 27, according to Netcraft. The company says attackers uploaded malicious text files into publicly accessible directories, hitting e-commerce brands, government services, universities, and nonprofits in what appears to be a broad opportunistic sweep rather than a tightly targeted operation.
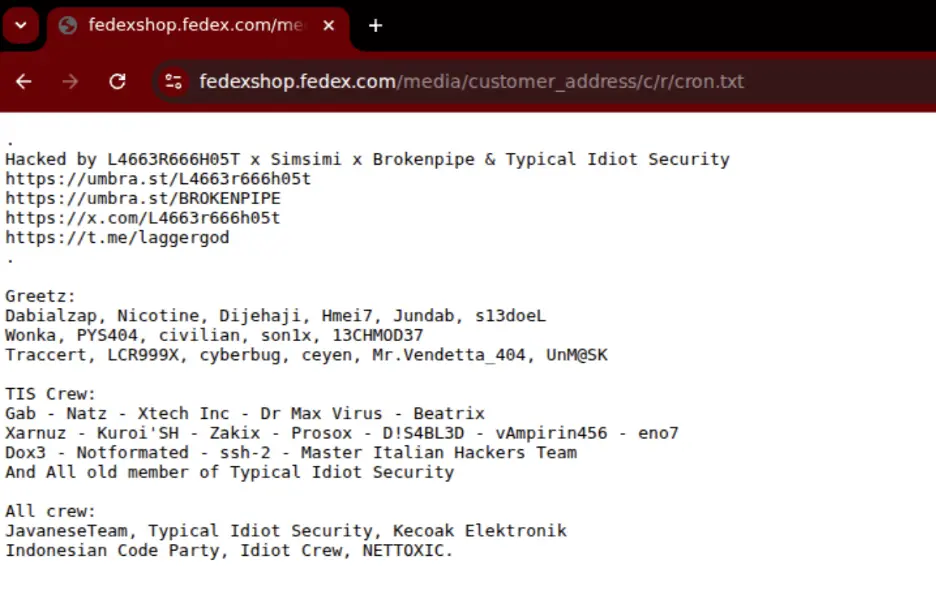
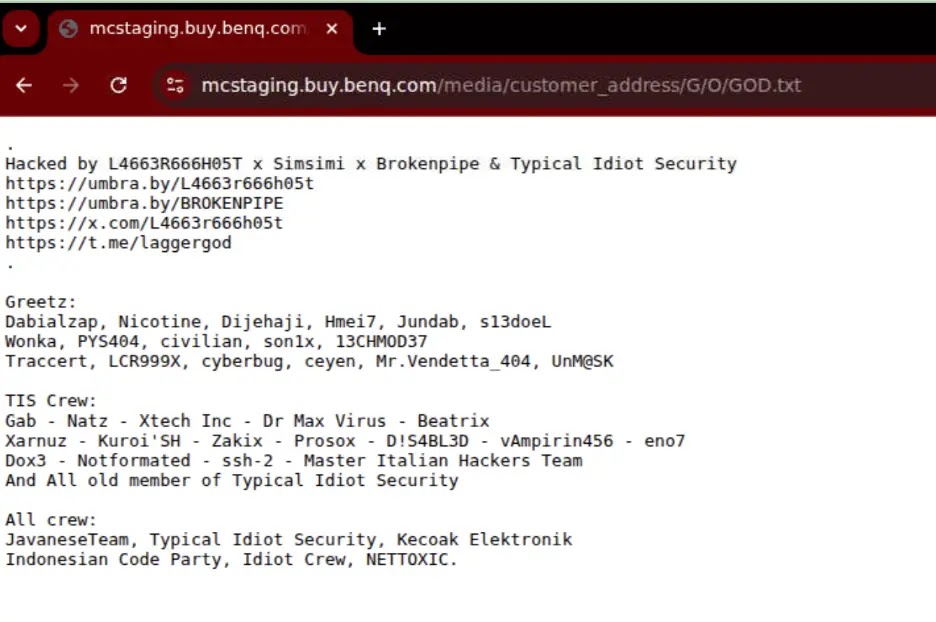
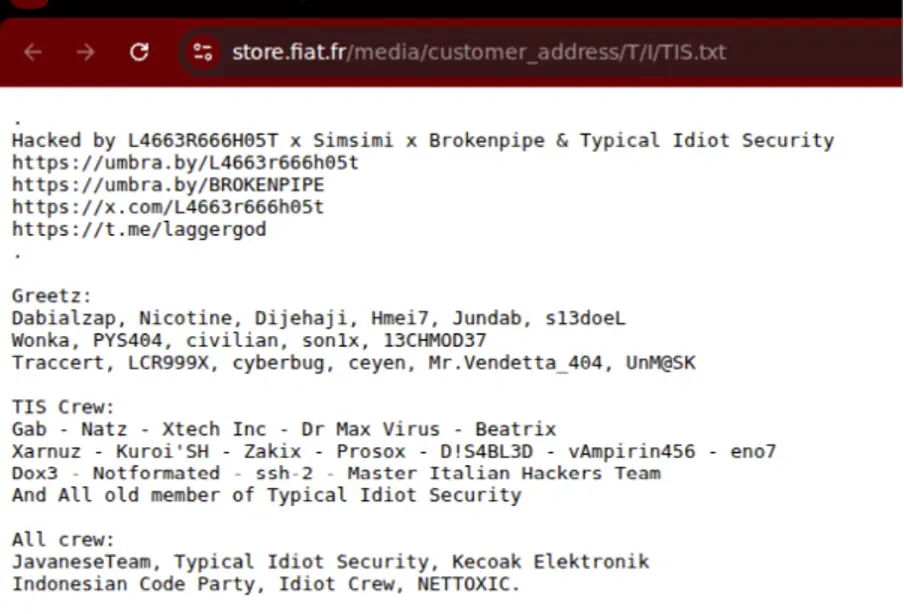
Netcraft says the campaign affected infrastructure linked to major brands including Toyota, Asus, Yamaha, BenQ, FedEx, Lindt, Fiat, Citroën, Diesel, Fila, and Bandai. The report also says some affected domains were tied to government and university infrastructure, as well as several Trump Organization domains. In many cases, the impacted sites were subdomains, regional storefronts, or staging systems, though some live customer-facing pages were also briefly affected.
The core issue appears to be an unauthenticated file upload weakness affecting some Magento and Adobe Commerce environments. Netcraft says it reproduced the behavior by uploading a .txt file to a test Magento Community 2.4.9-beta1 instance, which suggests some deployments may remain exposed even on newer versions depending on configuration.
That point matters because Adobe’s March 11 security bulletin does not describe known in-the-wild exploitation for the vulnerabilities it patched. Adobe said APSB26-05 fixes multiple critical, important, and moderate issues in Adobe Commerce and Magento Open Source, including bugs that could lead to arbitrary file system read and remote code execution, but said it was “not aware of any exploits in the wild” for those issues at the time of publication.
So far, the public picture suggests two related but not identical realities. Adobe has issued security updates for known Magento and Adobe Commerce flaws, while Netcraft says the behavior seen in this campaign does not directly match Adobe’s published fixes and may depend on server-side conditions that leave file upload paths exposed. That is an evidence-based interpretation from the two public sources, not a confirmed vendor attribution to one specific CVE.
How the attackers appear to be operating
Netcraft says the attackers mostly planted simple text-based defacement files rather than complex webshells or destructive payloads. Many of those pages included aliases such as “L4663R666H05T,” “Simsimi,” “Brokenpipe,” and “Typical Idiot Security,” along with “greetz” messages that are common in defacement culture. The report also says many incidents were self-reported to Zone-H using the notifier handle “Typical Idiot Security,” which suggests the actor or actors may be documenting the attacks for reputation-building.
A small subset of pages posted on March 7 included political messaging, but Netcraft says that did not match the main pattern of the broader operation. The company’s assessment points more toward indiscriminate exploitation of exposed infrastructure than a focused ideological campaign.
Why this campaign stands out
Magento remains one of the most widely used e-commerce platforms, which makes it a natural target for attackers who want scale. Once a working upload path or misconfiguration is identified, threat actors can automate the process and push it across thousands of domains very quickly. Netcraft’s figures suggest that is exactly what happened here, with the campaign expanding from late February into mid-March across a huge set of unrelated organizations.
The incident also highlights a familiar security gap in commerce platforms: patching the software alone may not fully remove risk if web server settings, upload handling, or exposed endpoints remain unsafe. Sansec, in separate March 2026 research, also described an unrestricted file upload issue in Magento and Adobe Commerce REST API paths that could enable file uploads under certain server configurations. That does not prove the same flaw drove Netcraft’s campaign, but it reinforces the idea that upload exposure remains an active risk area in Magento ecosystems.
Magento defacement campaign at a glance
| Item | Details |
|---|---|
| First activity seen | February 27, 2026 |
| Websites affected | 7,500+ |
| Hostnames affected | 15,000+ |
| Reported by | Netcraft |
| Main observed behavior | Upload of defacement text files into public directories |
| Suspected weakness | Unauthenticated file upload in some Magento environments |
| Affected platforms | Magento Open Source, Magento Enterprise / Adobe Commerce, Adobe Commerce with B2B |
| Notable pattern | Broad, opportunistic targeting across brands, public sector, and education |
What defenders should do now
Organizations running Magento or Adobe Commerce should urgently review exposed upload endpoints, inspect publicly accessible directories for unauthorized files, and apply current Adobe security updates. Netcraft says new compromised sites were still appearing at the time of its reporting, which means defenders should treat this as an active campaign rather than a closed event.

Priority actions include:
- Apply Adobe Commerce and Magento Open Source security updates from APSB26-05.
- Audit file upload endpoints and server-side handling rules.
- Search public web directories for newly added
.txt, script, or stray upload files. - Review staging, regional, and non-production storefronts, not just primary production domains.
- Monitor for follow-on abuse, because a defacement campaign can also serve as proof of access for deeper intrusion later. This is a grounded inference based on the exposed file-write behavior Netcraft described.
FAQ
Netcraft says the campaign impacted more than 7,500 websites and over 15,000 hostnames.
They uploaded malicious text files into publicly accessible directories, which led to widespread defacements across many affected domains.
No. In APSB26-05, Adobe said it was not aware of in-the-wild exploitation for the issues covered by that bulletin.
Netcraft points to an unauthenticated file upload issue affecting some Magento environments, but public reporting has not yet tied the campaign to a single confirmed CVE from Adobe.
No. Netcraft says the campaign also affected government agencies, universities, nonprofits, and other organizations.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages