The CTEM Divide: Why Most Security Programs Are Falling Behind in 2026
A recent wave of cybersecurity research highlights a growing gap between organizations that have adopted Continuous Threat Exposure Management (CTEM) and those that still rely on traditional security approaches. CTEM is a structured, continuous cyber risk management framework designed to help organizations identify, prioritize, validate, and remediate exposures in real time. According to industry analysts, companies that embrace CTEM are positioned to reduce their likelihood of a breach dramatically compared to those that have not.
CTEM was introduced by market leader Gartner and has gained traction as a next-generation framework for aligning cybersecurity with business risk priorities. Gartner’s data suggests a strong security advantage for organizations that integrate CTEM into their strategic risk-management programs, particularly by 2026.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What Is CTEM and Why It Matters
Continuous Threat Exposure Management (CTEM) is more than a set of tools. It is a proactive cybersecurity strategy. It focuses on reducing real operational exposure by continuously scanning, validating, and addressing threats before they can be exploited.
CTEM differs from traditional vulnerability programs by shifting from reactive, periodic checks to ongoing, risk-based decision making. This approach places emphasis on exposures that matter most to the organization’s business goals and critical assets, rather than on every technical finding.
Official Industry Insight
“By 2026, organizations that prioritize their security investments based on a Continuous Threat Exposure Management program will be three times less likely to suffer a breach.” Gartner, industry research cited widely in CTEM analysis
This statement from Gartner is frequently referenced in CTEM literature to underscore the potential impact of adopting continuous exposure management strategies.
Understanding the CTEM Framework
CTEM is commonly described as a five-stage cycle that organizations repeat continuously. These stages help teams keep their defenses aligned with evolving threats and business priorities.
| CTEM Phase | Core Activity |
|---|---|
| Scoping | Define business-critical assets and risk boundaries. |
| Discovery | Find exposures and inventory attack targets. |
| Prioritization | Rank exposures by risk, exploitability, and business impact. |
| Validation | Test real-world exploitability of top risks. |
| Mobilization | Remediate exposures and refine strategy. |
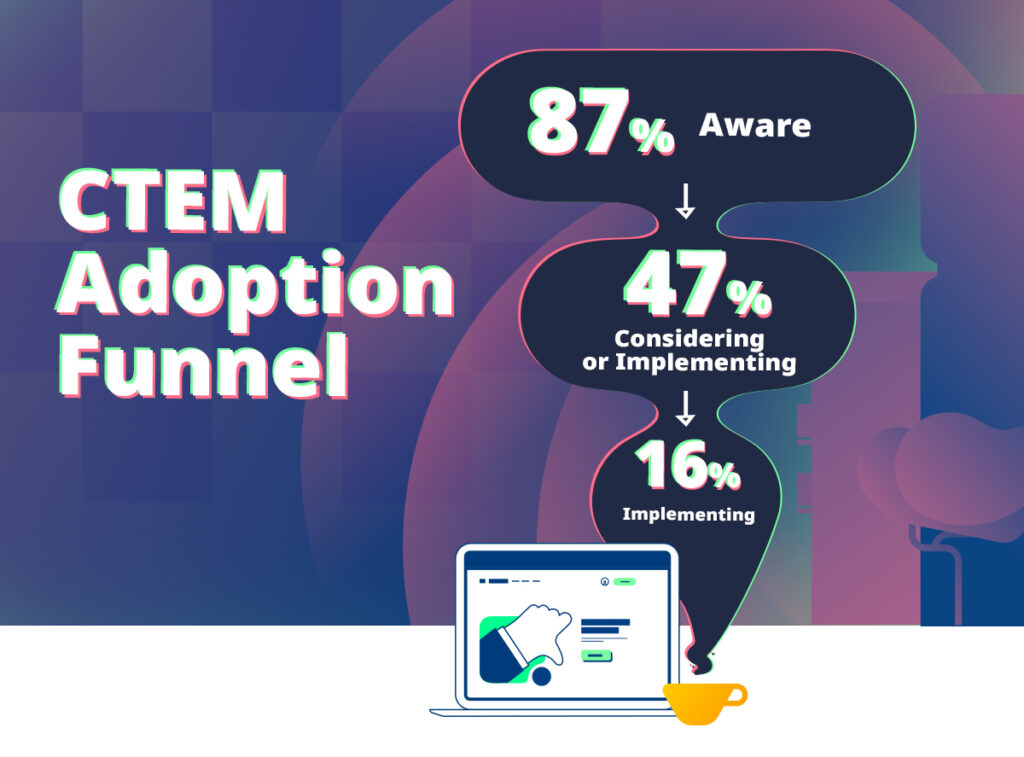
The CTEM Adoption Gap: Reality Check
Although awareness of CTEM’s benefits is increasing, many organizations struggle to implement it effectively. Traditional security models still focus on point-in-time assessments, periodic vulnerability scans, and patch cycles that do not keep pace with modern attack surfaces.
Legacy approaches treat vulnerabilities as static and isolated. In contrast, CTEM treats them as part of a dynamic system that needs ongoing validation and remediation based on current threat intelligence and real-world exploitability.
Industry analysis shows that those using CTEM frameworks tend to manage risk more proactively, while organizations relying on outdated models risk falling into blind spots that adversaries can exploit.
Why Security Leaders Are Embracing CTEM
Security teams and executives are turning to CTEM for several reasons:
- Proactive Risk Reduction: CTEM enables security teams to act before an exposure becomes an incident.
- Business Alignment: It aligns security efforts with business goals and risk tolerance.
- Measurement-Driven Results: Teams can track progress and prioritize work that reduces real business risk.
- Continuous Validation: Testing defenses and exposures continuously helps verify controls are effective.
- Improved Board Communication: CTEM metrics help translate technical insights into business terms.
CTEM turns cybersecurity from a series of isolated tasks into a measurable discipline that empowers security teams and business leadership to make better decisions.
CTEM vs. Traditional Security Approaches
| Aspect | Traditional | CTEM |
|---|---|---|
| Testing Frequency | Periodic (monthly/quarterly) | Continuous |
| Focus | Vulnerability counts | Exploitable exposures |
| Risk Prioritization | Severity scores | Business impact + exploitability |
| Action Planning | Siloed | Cross-team mobilization |
| Validation | Manual or periodic | Ongoing verification |
This comparison highlights how CTEM helps security teams focus on what really matters, rather than accumulating unchecked findings that don’t lead to measurable improvement.
Why the Divide Matters in 2026
As cyber threats evolve faster than ever, the divide between reactive and proactive security models widens. Modern attack surfaces span hybrid cloud environments, remote workforces, and external supply chains, making simple scanning and patching inadequate.
Security leaders who adopt CTEM can continuously refine priorities based on current exposure, reducing risk and improving resilience. Those who continue with legacy approaches risk falling behind as adversaries exploit gaps that static models cannot address.
Frequently Asked Questions (FAQ)
A: It stands for Continuous Threat Exposure Management, a continuous cyber risk management framework focused on proactive exposure reduction.
A: Modern digital environments change rapidly, and traditional vulnerability management can’t keep up. CTEM provides ongoing, real-time visibility and action.
A: According to Gartner, organizations that adopt CTEM are projected to be three times less likely to suffer a breach by 2026.
A: It is a program-level framework that integrates processes, teams, and technologies to continuously reduce security exposures.
A: Official research and frameworks are available from Gartner and cybersecurity leadership blogs that discuss CTEM fundamentals.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages