duer-js NPM Package Delivers “Bada Stealer” Windows and Discord Users at Risk
A malicious npm package named duer-js contains a multi-stage infostealer the JFrog team calls Bada Stealer. The package was published by the account luizaearlyx and is engineered to run on Windows, persist through Discord, and exfiltrate browser credentials, crypto wallet data, payment methods, and more. Security researchers at JFrog published the full technical analysis and remediation steps on February 11, 2026.
Install counts for duer-js are modest, but the malware is sophisticated. That means even a small number of installs can produce high impact. JFrog’s analysis shows the package uses heavy obfuscation, staged payloads, and multiple exfil channels so that removal of the npm module alone will not fully clean an infected machine.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What it does
duer-js installs an infostealer that harvests browser and wallet data, hijacks the Discord desktop client to steal tokens and payment info, and uploads stolen files to attacker-controlled endpoints. The primary research and full cleanup steps are available from JFrog.
How the attack works
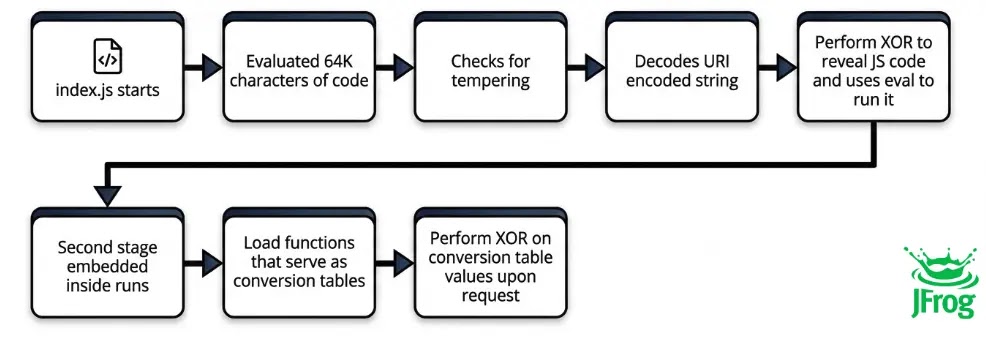
- A developer or system installs the
duer-jspackage from the npm registry. - The package executes obfuscated JavaScript that drops a staged Windows payload.
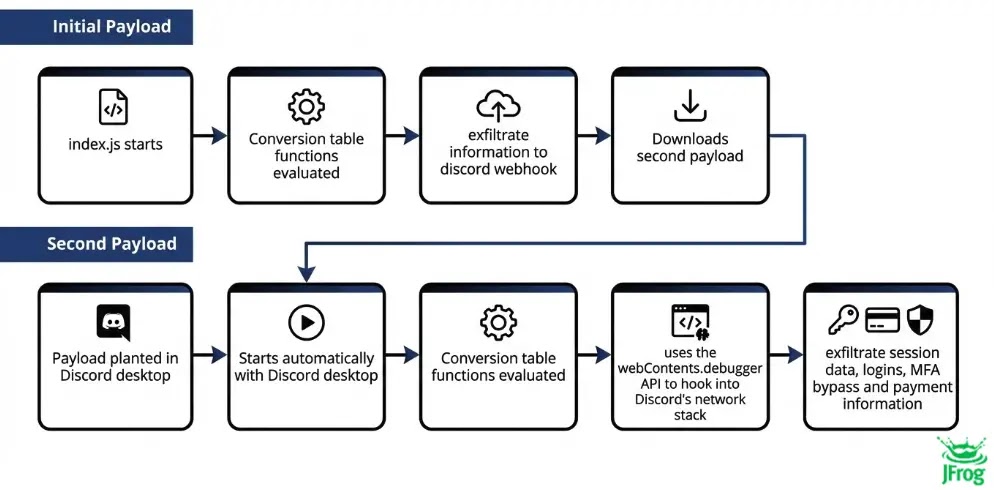
- The payload collects browser data (saved passwords, cookies, autofill), checks for crypto wallets (MetaMask, Exodus, BraveWallet), and searches for Steam and other app files.
- A secondary payload targets the desktop messaging client Discord, injecting code that runs on Discord startup to harvest tokens and billing information repeatedly.
- Stolen data is exfiltrated via a Discord webhook and a fallback cloud upload (for example Gofile).
JFrog’s researchers stress that duer-js implements persistence and automatic re-injection into the Discord process, meaning simple npm uninstall does not guarantee full removal.
“The JFrog Security Research team recently uncovered a sophisticated malicious package called duer-js published on NPM by the user luizaearlyx. After complex analysis, the package was identified as an advanced Windows targeted information stealer, self-named as ‘bada stealer’.” JFrog.
What JFrog found
- Multi-stage delivery: Obfuscated npm script drops native Windows artifacts.
- Discord injection: Secondary payload hooks Discord at startup to steal tokens and billing data each run.
- Browser and wallet theft: Targets Chrome/Edge/Brave/Yandex, and common browser wallet extensions.
- Dual exfil channels: Primary exfil via Discord webhook; backup via cloud storage upload.
- Persistence: Leaves artifacts that survive a simple package uninstall.
Quick indicators of compromise
- Presence of
duer-jsinnode_modulesof recent projects. - Unexpected Windows binaries dropped by npm installs (check timestamps and parent processes).
- Discord behaving oddly at startup or new unknown files under
%LOCALAPPDATA%\Discordor%APPDATA%\Discord. - Outbound POSTs to Discord webhook URLs from local host or uploads to obscure file hosting services.
- Files named like
result.txt, compressed archives with credential dumps, or evidence of DPAPI use in dumped browser files.
Immediate steps if you installed duer-js
- Isolate the host now from the network to stop further exfiltration.
- Do not simply run
npm uninstalland assume you are clean. The malware persists outside Node. - Clean Discord fully: close Discord; remove
%LOCALAPPDATA%\Discord,%APPDATA%\Discord, and reinstall only from the official site. Revoke all Discord tokens and reset 2FA. - Rotate passwords and any API keys that might have been stored in the browser or environment variables.
- Check crypto wallets used on the machine. Move funds to new wallets if possible and revoke connected dapps.
- Run a full forensic scan and compare artifacts against IOCs in the JFrog report. If in doubt, restore from a clean backup or reimage the host.
What to check now
| Area | Action |
|---|---|
| npm projects | Search for duer-js and other unknown modules in node_modules |
| Windows host | Look for recently created native executables, suspicious autorun entries |
| Discord | Remove local Discord folders, revoke tokens, re-install official client |
| Browsers | Export and rotate saved passwords; clear cookies and local storage |
| Crypto wallets | Move funds, re-create wallets on a clean device |
| Backups | Verify backups are clean before restoring |
Why developers and users are at special risk
Developers often run packages with elevated privileges during builds or local tests. A malicious package that drops a native payload can therefore execute with the same user rights used in local development. The addition of Discord persistence transforms a one-time theft into ongoing harvesting. That combination makes duer-js particularly dangerous for dev machines that also hold credentials and wallets.
Longer cleanup checklist for security teams
Report the malicious package and any confirmed compromises to the npm security team and to JFrog.
Quarantine affected machines and preserve images for forensic analysis.
Hunt across your estate for Jest, CI runners, or build agents that might have pulled duer-js.
Revoke secrets that might have been in dev environment variables or local config files.
Add WAF/endpoint rules to block known exfil endpoints and suspicious webhook traffic.
Educate dev teams: confirm package names, check maintainers, and prefer audited packages.
FAQ
duer-js still on the npm registry? A: At the time of JFrog’s publication the package remained available. Check the JFrog post for the latest status and for the exact malicious versions.
A: No. JFrog found the package drops native payloads and modifies Discord, so uninstalling Node packages alone is not sufficient. Full removal and forensic validation are required.
A: The payload locates browser profile data and uses Windows DPAPI techniques to extract or leverage saved credentials. Exact mechanics and examples are in the JFrog analysis.
A: Yes. In addition, revoke all active sessions and reset two-factor authentication. Assume tokens may be stolen if Discord ran on an infected machine.
A: The technical analysis and remediation guidance come from JFrog. See their full writeup for code, IOCs, and step-by-step cleanup.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages