Asia Crypto Scams Combine Malvertising and Pig Butchering: ¥10M Losses

Sophisticated crypto scams target Asia, especially Japan, blending malvertising with pig butchering tactics. Victims lose up to ¥10 million through fake social media ads leading to AI-powered chat scams. Infoblox identified over 23,000 suspicious domains driving the campaign.
Attackers place convincing ads on Facebook and Instagram impersonating financial experts. Ads promote “AI-driven” investment algorithms with guaranteed returns. Victims click through to fake investment portals with QR codes for LINE, WhatsApp, or KakaoTalk groups.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
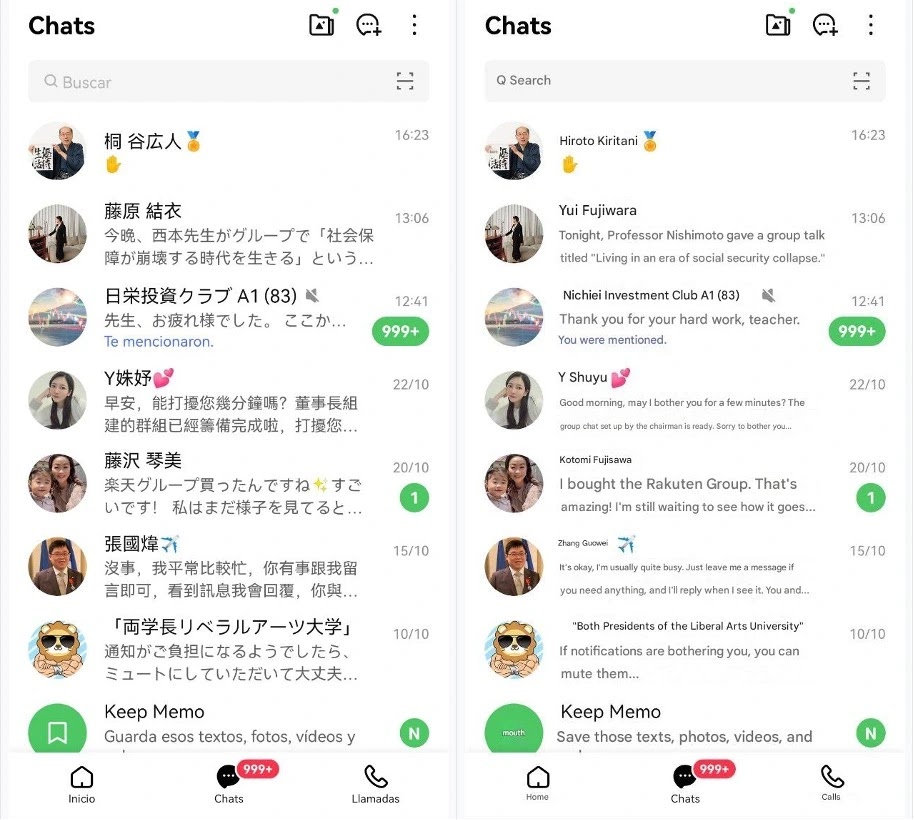
AI chatbots engage victims 24/7 across multiple languages. Bots share fake success stories and encourage small test deposits. Early “profits” build trust for larger transfers. Withdrawal attempts trigger “release fee” demands before scammers disappear.
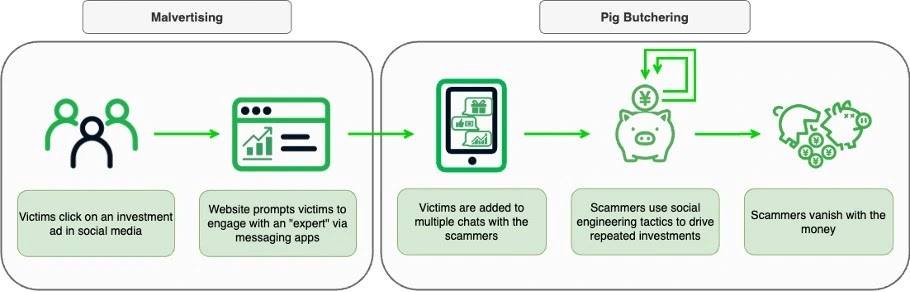
Attack Chain Breakdown
Five-stage operation scales through automation.
- Malvertising: Social media ads impersonate experts
- Lure sites: Fake portals with QR code entry points
- Chat onboarding: LINE/WhatsApp/KakaoTalk group access
- Trust building: AI bots deliver fabricated returns
- Cash out: Release fee scam extracts final payments
Infrastructure Scale
Massive domain generation evades blocking.
| Metric | Scope |
|---|---|
| Suspicious domains | 23,000+ identified |
| Domain generation | RDGA automation |
| Target countries | Japan primary, Asia-wide |
| Messaging platforms | LINE, WhatsApp, KakaoTalk |
| Active campaigns | 3+ parallel operations |
Registered Domain Generation Algorithms create lookalike domains rapidly. Infrastructure supports multiple actors simultaneously.
AI Bot Characteristics
Automated engagement shows distinct patterns.
- Instant 24/7 responses across timezones
- Seamless Japanese/English/Korean switching
- Consistent fabricated success narratives
- Escalating deposit pressure tactics
- Professional withdrawal excuse generation
Victim Impact Statistics
Individual losses reach catastrophic levels.
¥10M maximum single loss (~$67K USD)
Japan primary target geography
Social media primary vector
Crypto-only payment extraction
100% funds unrecoverable
Technical Indicators
Domain clusters reveal operational patterns.
Domain Patterns:
- Japanese financial brand lookalikes
- High-volume DNS queries from Japan
- Rapid registration/expiration cycles
- Shared IP clusters across campaigns
- QR code hosting concentration
Chat Indicators:
Perfect weekend availability
Zero response delays
Language fluency switching
Screenshot fabrication consistency
Platform migration fluency
Scam Infrastructure Model
Service-as-a-Platform enables parallel operations.
Domain generation → RDGA service
Ad placement → Social media arbitrage
Chat automation → AI bot platform
Payment routing → Crypto tumblers
Victim management → Dashboard access
Multiple actors rent infrastructure simultaneously.
Platform Exploitation
Social platforms serve as primary attack vectors.
| Platform | Ad Prevalence | Chat Hand-off |
|---|---|---|
| High | QR code primary | |
| High | Direct messages | |
| LINE | Chat primary | Group onboarding |
| Chat secondary | International | |
| KakaoTalk | Korea focus | Local preference |
Immediate Defense Actions
Users need concrete protection steps.
Social Media Hygiene:
- Verify expert accounts via official channels
- Block investment ads immediately
- Never scan unverified QR codes
- Report suspicious financial content
Crypto Wallet Protection:
- Hardware wallet mandatory
- Multi-signature for large transfers
- Test small amounts first
- Monitor for unauthorized approvals
Chat Platform Controls:
- Disable unknown group adds
- Limit financial discussions
- Screenshot suspicious interactions
- Report to platform immediately
Enterprise Monitoring
Organizations track campaign indicators.
DNS Intelligence:
- Block 23,000+ Infoblox IOC domains
- Monitor RDGA pattern emergence
- Alert Japanese employee DNS spikes
Endpoint Protection:
- QR code scanning alerts
- Malicious domain preemption
- Social media ad click monitoring
Scam Takedown Challenges
Infrastructure resilience defeats blocking.
- 23,000 domains rotate hourly
- RDGA generation outpaces lists
- AI automation scales infinitely
- Crypto payments untraceable
- Platform arbitrage shifts rapidly
Regional Risk Assessment
Asia faces highest exposure levels.
| Country | Threat Level | Platform Focus |
|---|---|---|
| Japan | Critical | LINE + Facebook |
| South Korea | High | KakaoTalk |
| India | Medium | |
| Southeast Asia | Medium | Regional mix |
FAQ
Fake financial expert ads on Facebook/Instagram lead to QR code chat groups.
Long-term relationship building for large crypto transfers.
24/7 chatbots deliver convincing investment conversations.
¥10 million per individual reported.
23,000+ generated by RDGA automation.
Japan shows highest DNS query volume.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages