New SysUpdate Variant Targets Linux Systems with Encrypted C2 Traffic

A new variant of SysUpdate malware has been found attacking Linux systems. Security researchers at LevelBlue discovered it during a real-world incident response. They also built a decryption tool to reveal its hidden command-and-control communications.
This threat uses strong encryption to hide its activities from defenders. The malware runs as a disguised system service on Linux servers. Traditional tools struggle to unpack and analyze it fully.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Malware Discovery Details
LevelBlue teams spotted the suspicious ELF64 binary in a client’s environment. The file lacks section headers and uses an unknown packer. This design blocks standard reverse engineering techniques.
When launched without arguments, it runs the Linux “id” command for reconnaissance. It collects user and group details quickly. Then it sets up encrypted network links over multiple protocols.
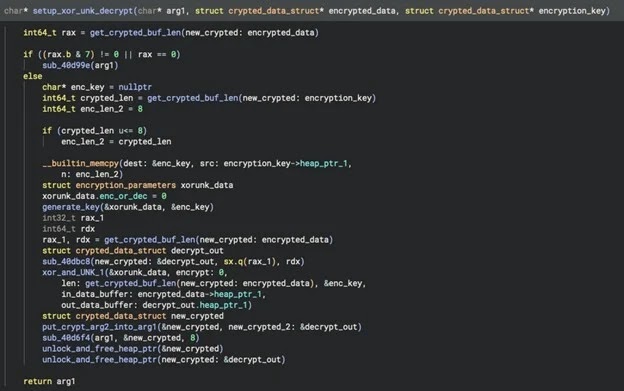
Researchers linked it to SysUpdate through dynamic analysis and endpoint data. They gained high confidence via detailed code examination. The C++ code handles complex crypto routines for C2 traffic.
Decryption Tool Breakthrough
LevelBlue created a tool with the Unicorn Engine to crack the encryption. They did this without decoding the full algorithm. The work happened live during the incident for fast results.
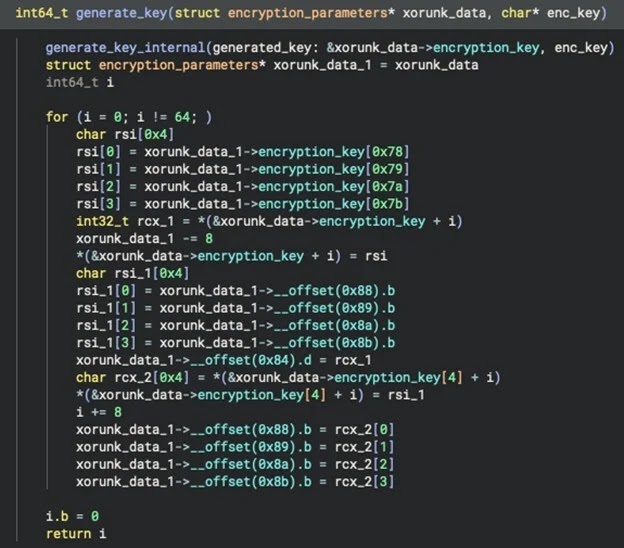
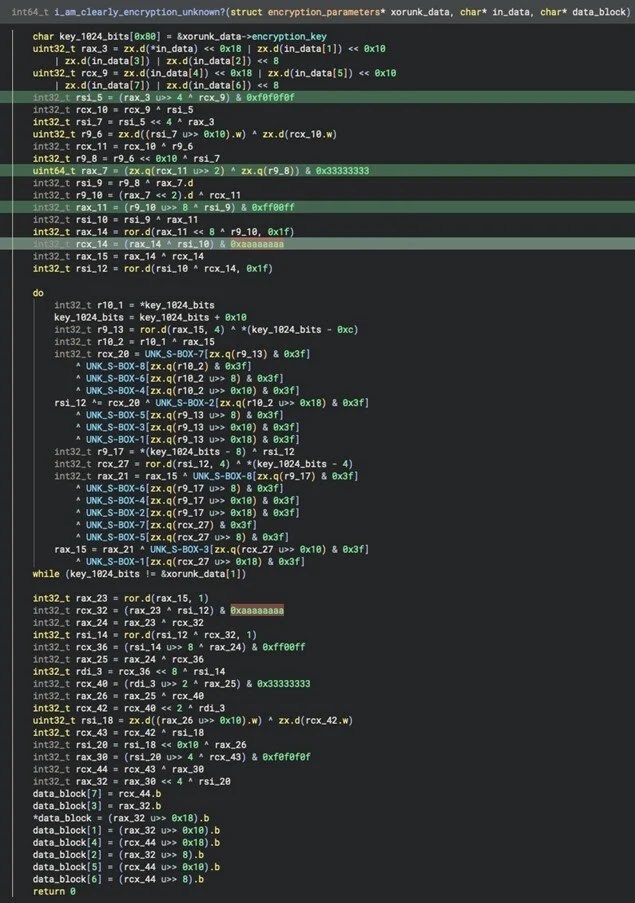
Experts pulled machine code, heap data, and CPU states from the running malware. They emulated key generation from hardcoded plaintext in memory. A second emulator handled decryption with XOR and custom logic on 8-byte blocks.
Tools like Binary Ninja aided static analysis. GDB helped with debugging. Rust bindings for Unicorn ran x86-64 code safely.
Technical Breakdown
| Component | Function | Tools Used |
|---|---|---|
| Packer Analysis | Unpack ELF64 binary | Binary Ninja |
| Reconnaissance | Gather system info | GNU/Linux “id” command |
| Key Extraction | Pull plaintext key | Heap memory dump |
| Emulation | Run crypto routines | Unicorn Engine (Rust) |
| Decryption | Process C2 blocks | Dual emulators with XOR |
The setup mirrors the malware’s memory layout exactly. Stack, heap, data, and code segments all match. This lets teams decrypt traffic from related variants by swapping keys.
Defense Recommendations
- Scan for packed ELF binaries posing as services.
- Monitor network flows for odd encrypted patterns.
- Build emulation skills for incident response.
- Use EDR tools to catch early reconnaissance.
Organizations face rising Linux threats from groups like this. Quick tool development shows how emulation beats unknown crypto. Stay updated on SysUpdate indicators.
FAQ
SysUpdate is a Linux-targeting threat family. This variant adds advanced C2 encryption and evasion tactics.
It emulates the malware’s own functions. One part generates keys. The other decrypts blocks. No full algorithm reverse needed.
Linux servers with weak endpoint monitoring. Focus on ELF64 executables.
Look for no-section-header binaries. “id” command spikes. Encrypted multi-protocol traffic. Full list in LevelBlue report.
Deploy EDR. Analyze traffic. Practice malware emulation. Update incident playbooks.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages