MuddyWater Launches Operation Olalampo Targeting MENA with New Malware

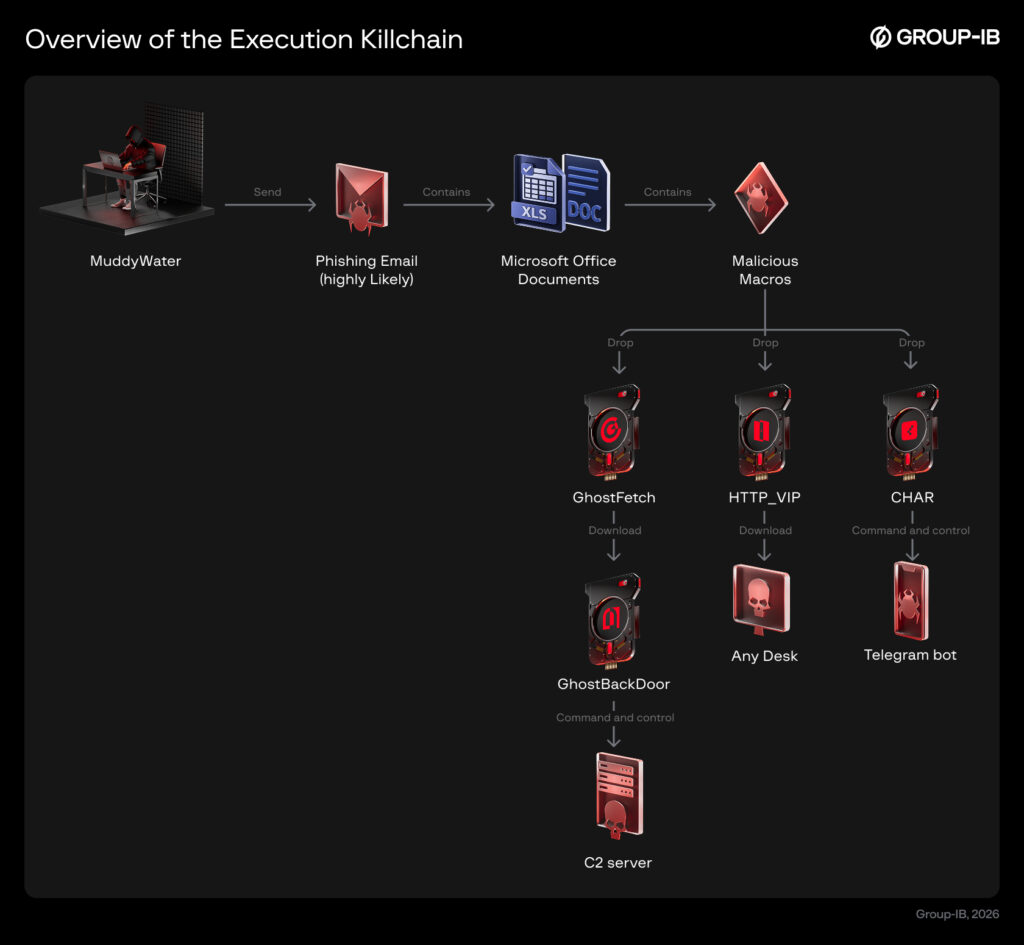
Iran-linked MuddyWater (aka Earth Vetala, Mango Sandstorm) started Operation Olalampo on January 26, 2026. It hits MENA organizations using phishing and new tools like GhostFetch, CHAR, HTTP_VIP, and GhostBackDoor.
Attacks begin with Excel docs prompting macro enablement. Macros decode payloads for remote access. Lures include flight tickets, reports, or fake energy firms.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
One chain drops Rust backdoor CHAR via Telegram bot “stager_51_bot” (named Olalampo). Another uses GhostFetch downloader for GhostBackDoor. HTTP_VIP fetches AnyDesk from codefusiontech[.]org.
CHAR executes cmd/PowerShell for SOCKS5 proxies, Kalim backdoor, browser theft, and binaries like sh.exe. Group-IB notes AI-assisted code from emojis in strings.
Malware Toolset Breakdown
GhostFetch profiles systems, evades sandboxes, loads payloads in memory. GhostBackDoor offers shell, file ops, re-runs GhostFetch.
HTTP_VIP reconnoiters, authenticates, deploys AnyDesk. New variants add shells, file transfer, clipboard grabs.
CHAR uses Telegram C2 for flexible commands. Shares Rust style with BlackBeard RAT.
Attack Chain Table
| Stage | Malware | Key Features |
|---|---|---|
| Initial Access | Malicious Excel | Macro drops loader |
| Downloader | GhostFetch | Anti-VM/debug, memory exec |
| Downloader | HTTP_VIP | AnyDesk deploy, C2 auth |
| Backdoor | GhostBackDoor | Shell, file R/W |
| Backdoor | CHAR | Telegram bot C2, PowerShell |
MuddyWater exploits public servers too. This keeps options open beyond phishing.
Campaign Insights
Targets focus on MENA governments, corporates. Tools show maturity with memory loads, Telegram C2, AI dev hints.
Diversified C2 blends malicious and legit traffic. Rust use boosts cross-platform evasion.
Group-IB warns of expansion. MuddyWater persists in META region with custom tools.
FAQ
MuddyWater’s MENA campaign since Jan 26, 2026. Uses GhostFetch, CHAR, etc., for espionage.
Phishing Excel with macros. Drops downloaders leading to backdoors.
Rust-based, Telegram C2 bot “stager_51_bot”. Runs proxies, stealers.
MENA organizations, mainly META area. Geopolitical focus.
Emojis in CHAR code suggest LLM help, per Group-IB analysis.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages