Silver Fox APT Deploys Winos 4.0 Malware with DLL Sideloading and BYOVD Against Asian Targets

Silver Fox threat actors launched sophisticated Winos 4.0 (ValleyRat) malware campaigns targeting Asian organizations. Fortinet researchers uncovered phishing attacks using localized lures like tax notices and invoices. These deliver ransomware with advanced evasion via DLL sideloading and Bring Your Own Vulnerable Driver (BYOVD) techniques.
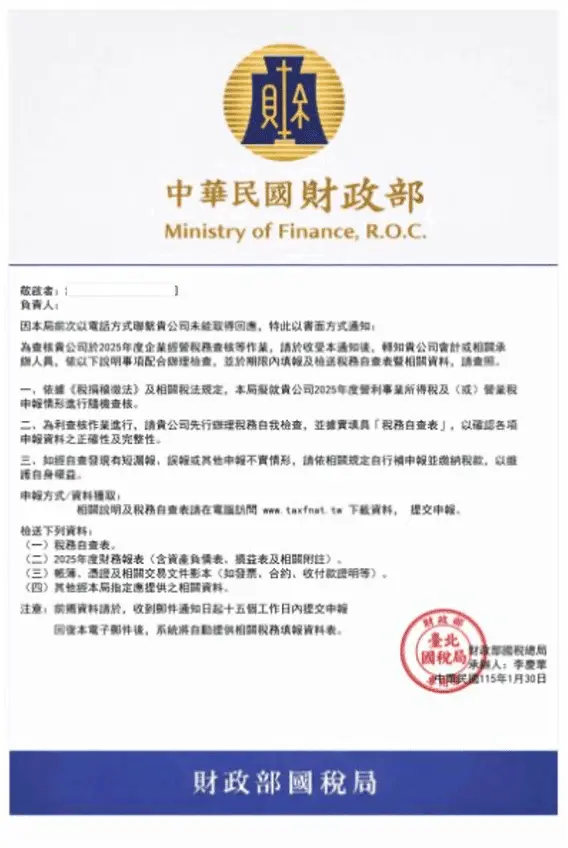
Phishing emails mimic government correspondence perfectly. Attachments contain archives with legitimate apps that sideload malicious DLLs. Victims see familiar tax forms or software installers. Interaction triggers silent infection chains.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
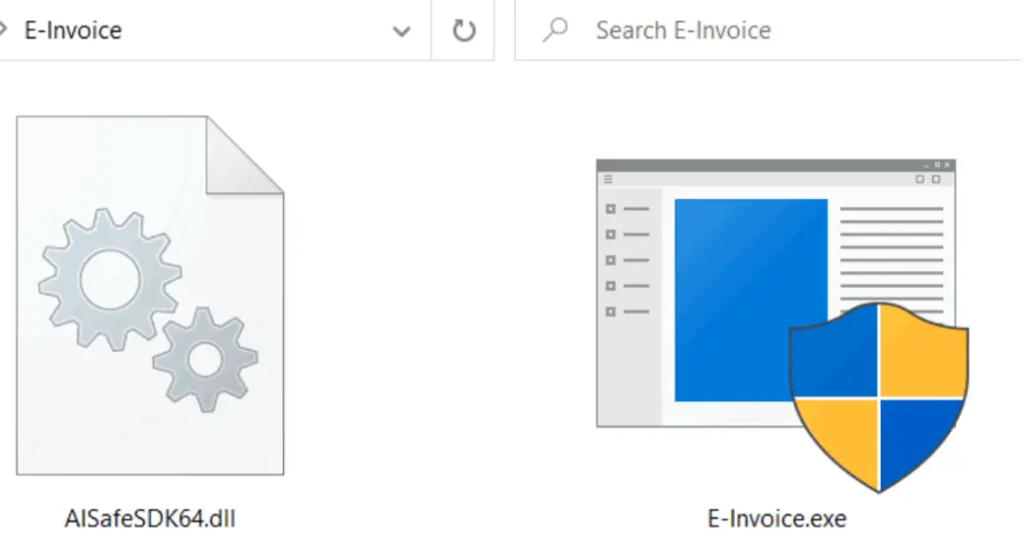
Archives include LNK files and decoy documents. These execute signed Windows drivers like wsftprm.sys for kernel access. Attackers rotate cloud domains rapidly to dodge blocks. This volatility frustrates traditional defenses.
Once elevated, Winos 4.0 kills antivirus processes systematically. It targets dozens of endpoint tools creating blind spots. File encryption follows alongside data theft for extortion.
Silver Fox focuses on Taiwan and regional firms. Localized Chinese lures boost click rates. Operations show state-sponsored sophistication with custom tooling.
These messages closely impersonate official government correspondence, such as tax audit notifications, software installers, and electronic invoice downloads.
Infection Chain Breakdown
Malware uses legitimate binaries for initial execution. DLL sideloading loads payloads in memory avoiding disk writes. BYOVD exploits signed drivers for privilege escalation.
Driver monitoring loop scans for security software continuously. Terminated processes include major AV vendors. C2 communication persists through domain hopping.
Ransomware encrypts files rapidly. Exfiltrated data fuels follow-on attacks. Infrastructure changes hourly complicating tracking.
Attack Techniques Table
| Technique | Purpose | Evasion Method |
|---|---|---|
| DLL Sideloading | Initial execution | Legit app + malicious DLL |
| BYOVD (wsftprm.sys) | Kernel privileges | Signed vulnerable driver |
| AV Evasion | Kill security tools | Process termination loop |
| Domain Rotation | C2 persistence | Cloud hosted + rapid flux |
| Phishing Lures | Initial access | Localized tax/invoice themes |

Organizations face stealthy persistence. Traditional signatures miss memory loads and signed drivers. Behavioral detection proves essential.
Defense Recommendations
- Deploy behavioral analysis on endpoints.
- Block archives from unknown senders.
- Monitor for wsftprm.sys driver loads.
- Enable application whitelisting strictly.
- Hunt for anomalous kernel activity regularly.
Fortinet stresses rapid domain pivots as key indicators. Security teams must watch cloud C2 patterns closely. Update all drivers to patch BYOVD vectors.
Asian firms report rising ransomware. Silver Fox campaigns align with regional tensions. Enterprises need proactive threat hunting now.
FAQ
Asia-focused group using Winos 4.0 ransomware with advanced evasion. Targets Taiwan heavily.
Legitimate app loads malicious DLL from phishing archive silently.
wsftprm.sys gains kernel privileges via signed vuln.
Asian orgs via tax notices, invoices in Chinese. Fortinet report linked above.
AV process kills, wsftprm.sys loads, cloud domain flux patterns.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages