GrayCharlie Hijacks WordPress Sites to Deliver NetSupport RAT and Stealc Malware

Threat actor GrayCharlie (aka SmartApeSG/ZPHP/HANEMONEY) injects malicious JavaScript into WordPress sites since mid-2023. Compromised legitimate domains serve fake browser updates or ClickFix CAPTCHAs delivering NetSupport RAT, Stealc infostealer, and SectopRAT. U.S. law firms hit hardest through suspected SMB Team supply-chain compromise.
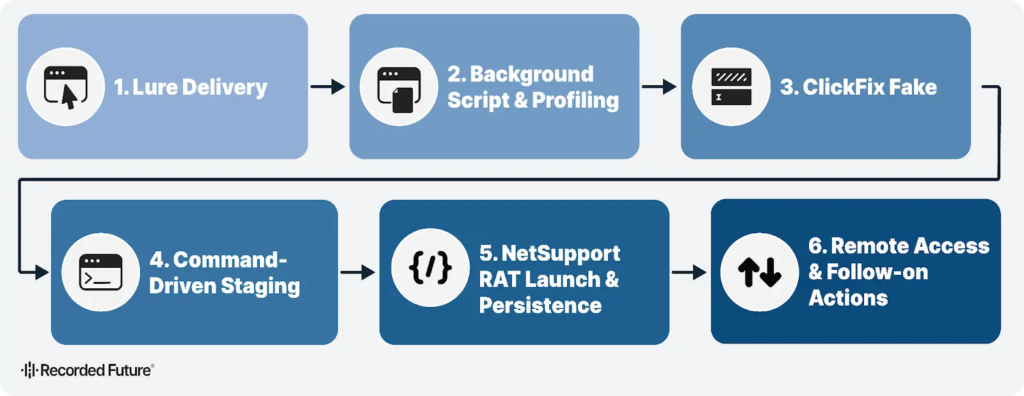
Attackers embed script tags in site DOM pointing to external JS on MivoCloud/HZ Hosting servers. Visitor browsers profiled for OS compatibility before payload selection. Fake Cloudflare verification or update prompts trick users into self-installation.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
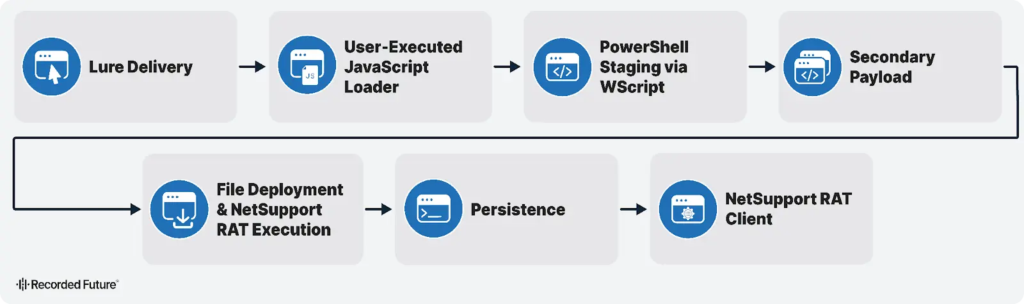
PowerShell execution follows user paste of obfuscated commands. NetSupport RAT extracts to AppData with Registry persistence. Operators gain full remote control immediately. Stealc harvests credentials; SectopRAT adds secondary payloads.
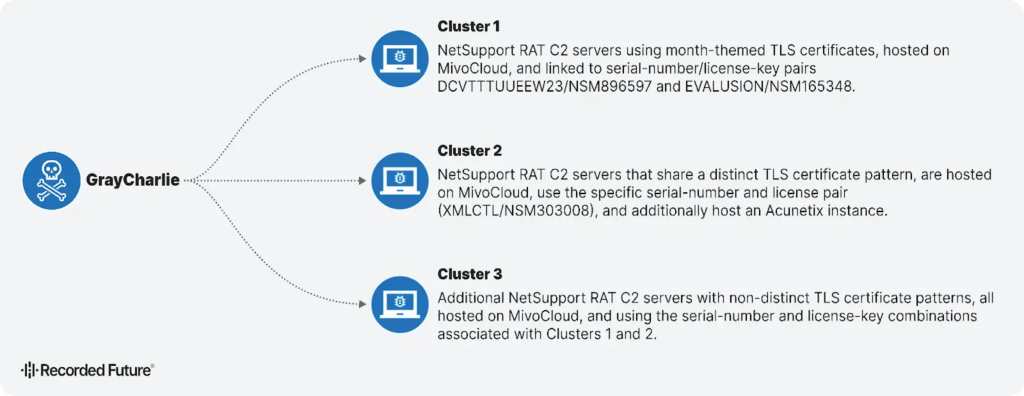
Two C2 clusters identified by TLS certs, license keys, serial numbers. TCP 443 traffic mimics HTTPS. SSH manages staging servers. Russian-language browsing patterns suggest actor origins.
15+ U.S. law firm sites injected with identical JS. SMB Team credentials leaked align with domain activation timing. Supply-chain attack suspected targeting North American legal sector.
Infection Chains Table
| Chain | Trigger | Payload Delivery | Persistence |
|---|---|---|---|
| Fake Update | JS profiling → WScript | PowerShell → AppData RAT | Registry Run key |
| ClickFix CAPTCHA | Malicious command paste | Batch file → RAT install | Reboot survival |
| Secondary Drop | RAT C2 recon | SectopRAT deployment | Memory execution |
Global reach spans industries. U.S. remains prime target. Law firms expose sensitive client data post-infection.
C2 Infrastructure Details
Cluster 1: MivoCloud-hosted, specific TLS naming
Cluster 2: HZ Hosting Ltd, unique license keys
Management: SSH access, 443 outbound
Operators: Russian-speaking per analytics
EDR evasion through legitimate hosting and HTTPS blending. Steady 2025 deployments show active maintenance.
Attack Indicators
- Injected
<script src="attacker-domain/jq.js">in WordPress DOM - Fake Cloudflare verification demanding PowerShell
- WScript → PowerShell → AppData\Netsupport.exe
- SMB Team email credentials in leaks
- MivoCloud/HZ Hosting C2 patterns
Defense Recommendations
- Scan WordPress for unauthorized DOM script tags daily
- Deploy YARA/Snort/Sigma rules for NetSupport/Stealc
- Block GrayCharlie IOCs: MivoCloud IPs, jq.js domains
- Monitor SMB shares for SMB Team indicators
- Enable EDR memory scanning for Lua loaders
- Train users against ClickFix browser prompts
Law firms scramble post-compromise. Client PII exposed through persistent RAT access. Supply-chain vetting gaps enable widespread infections.
FAQ
NetSupport RAT for remote control, plus Stealc infostealer and SectopRAT.
Malicious JS injected into legit WordPress sites profiling visitors for payloads.
U.S. law firms (15+ sites) via SMB Team supply-chain compromise.
HTTPS C2 on 443, SSH staging, fake Cloudflare ClickFix social engineering.
MivoCloud and HZ Hosting Ltd C2 servers.
Recorded Future full report linked above with IOCs and rules.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages