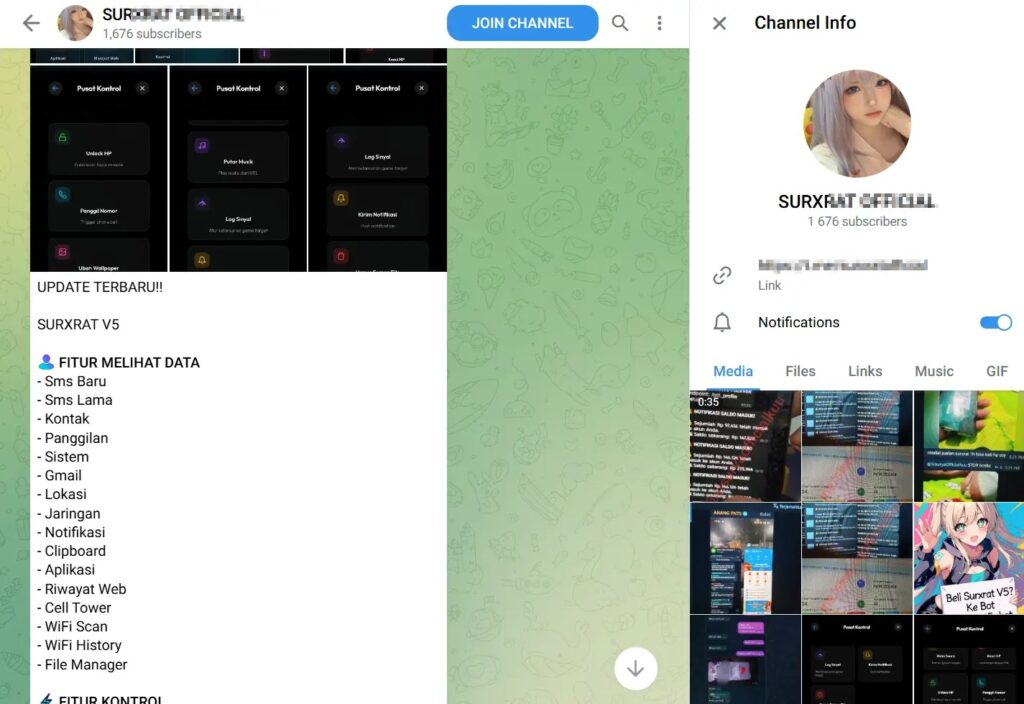
SURXRAT Android RAT Enables Full Device Takeover and Data Exfiltration for Attackers

SURXRAT, a advanced Android Remote Access Trojan, grants attackers complete control over infected devices. It steals data like SMS, contacts, and files while adding ransomware locking. Sold as Malware-as-a-Service on Telegram with reseller tiers, it evolves from ArsinkRAT. Cyble reports: “SURXRAT uses Firebase for stealthy C2 and Accessibility abuse for persistence.”
Attackers lure users with fake apps via social engineering on SMS or social media. Once installed, SURXRAT seeks permissions for SMS, calls, location, storage, and camera. The key is Accessibility Services. Users enable it thinking it’s for app features. This lets malware read screens, log keystrokes, and fake taps.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
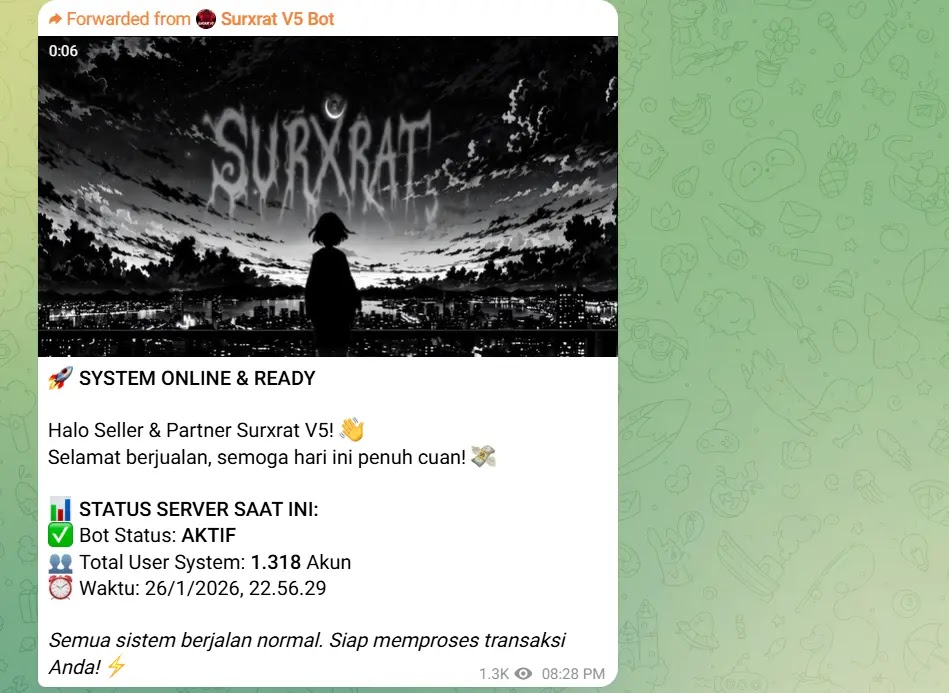
Cyble tracked Telegram channels advertising V5. Pricing suits small operators. Firebase Realtime Database hides C2 traffic among legit app calls. Traditional AV struggles. As of February 26, 2026, samples appear on VirusTotal; scan devices
Exfiltration covers logs, history, and media. Active features snap photos, record audio, download files. Ransomware overlays full screens with custom PIN demands. Failed unlocks ping attackers live for pressure.
This hybrid threat shifts from spy to extortion fast. Targets span personal banking fraud to enterprise spying. Rapid spread via MaaS boosts global risk.
Core Features Table
| Category | Capabilities |
|---|---|
| Data Theft | SMS/contacts exfil, call logs, browser history, files |
| Surveillance | Remote camera/mic, screen capture, keylogging |
| Control | Fake inputs, overlays, command execution |
| Ransomware | Persistent PIN locker with live monitoring |
| Stealth | Firebase C2, Accessibility persistence |
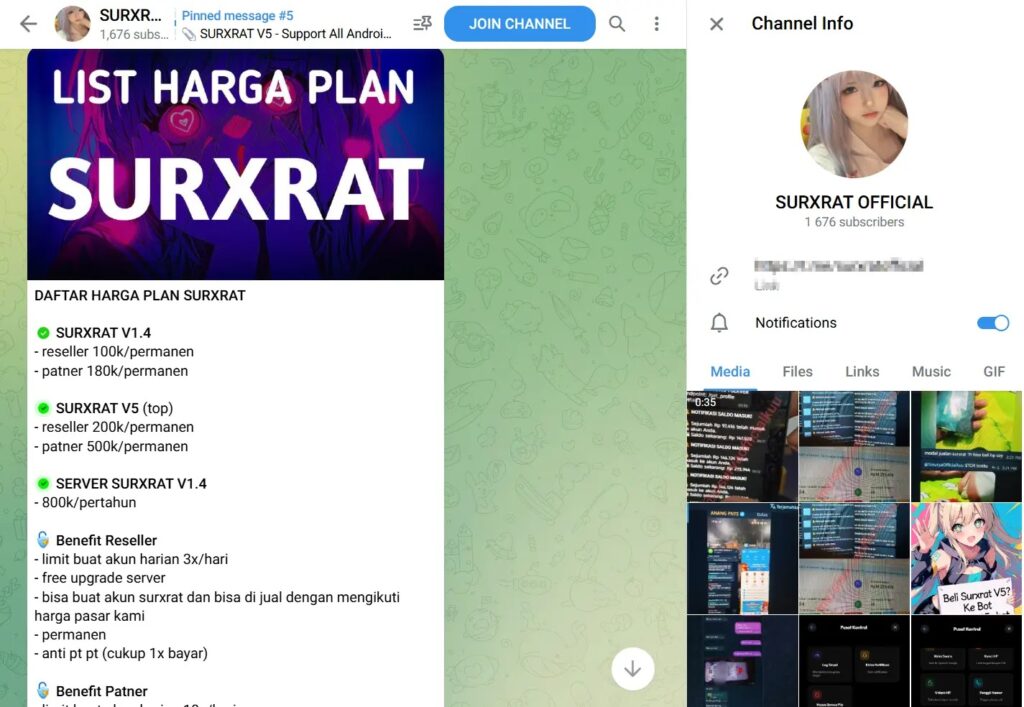
Telegram Pricing Tiers
| Tier | Price Range | Perks |
|---|---|---|
| Basic Reseller | Low entry | Custom APK builder |
| Partner | Mid-tier | Distribution tools, support |
| Enterprise | High | Full customization, priority C2 |
Ads show registered accounts for builders.
Attack Chain
Step-by-step infection.
- Lure via phishing SMS/social.
- Sideloading fake APK.
- Permission prompts granted.
- Accessibility enabled.
- Beacon to Firebase C2.
- Data flows; locker optional.
Defense Strategies
Layer protections.
- Stick to Google Play; enable Play Protect.
- Review Accessibility apps monthly.
- Use MFA everywhere.
- Update Android/OS promptly.
- Deploy enterprise MDM with app vetting.
- Scan with tools like Malwarebytes.
FAQ
Full control via Accessibility, plus ransomware; MaaS spreads it wide.
Blends malicious traffic with normal app data.
Battery drain, odd permissions, Firebase network spikes.
No; uninstall app, factory reset if locked. Vendor: Soliton? Wait, Android/Google Play advisories.
Android users globally via Telegram affiliates.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages