Fake Avast Refund Scam Harvests Credit Cards: Targets French Users with €499.99 Lure

Cybercriminals impersonate Avast on a fake site to steal credit card details. They claim a €499.99 charge hit your account today and push urgent refunds. Enter card info to “cancel.” Malwarebytes warns: “The site uses Avast’s real logo from their CDN, dynamic dates, and Luhn validation for legit-looking theft.”
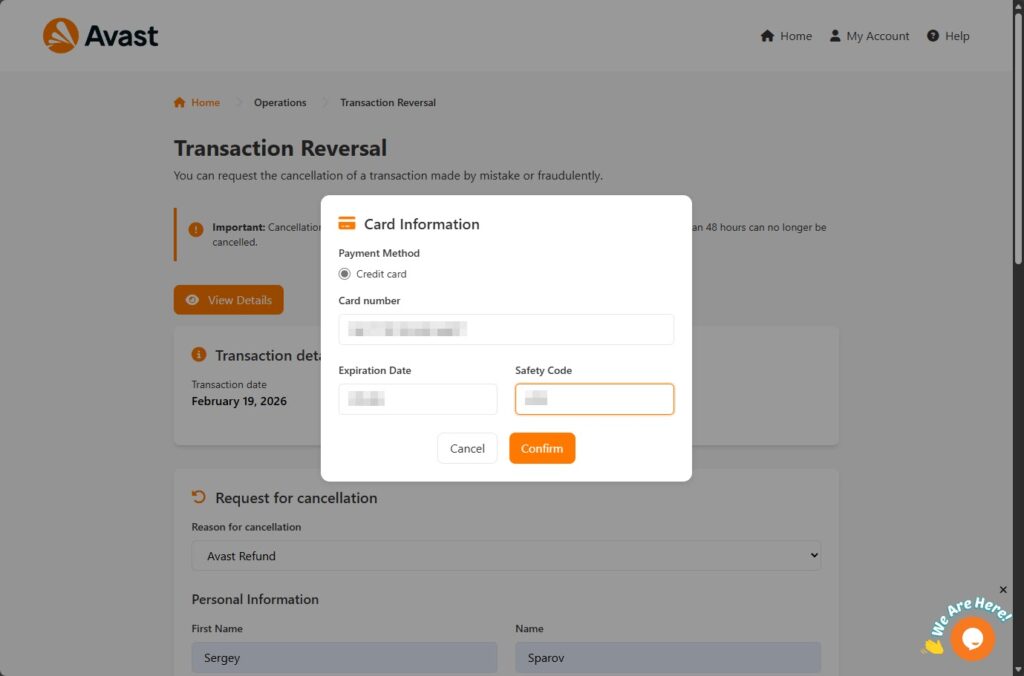
The page mimics Avast’s portal with orange theme, “Home,” “My Account,” and “Help” links. A warning mixes 72-hour and 48-hour deadlines for panic. It loads Avast logo from official CDN for credibility. Targets French speakers mainly.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
JavaScript pulls your local date to fake a fresh charge. No login needed. First form grabs name, email, address, phone. Then a modal demands card number, expiry, CVV.
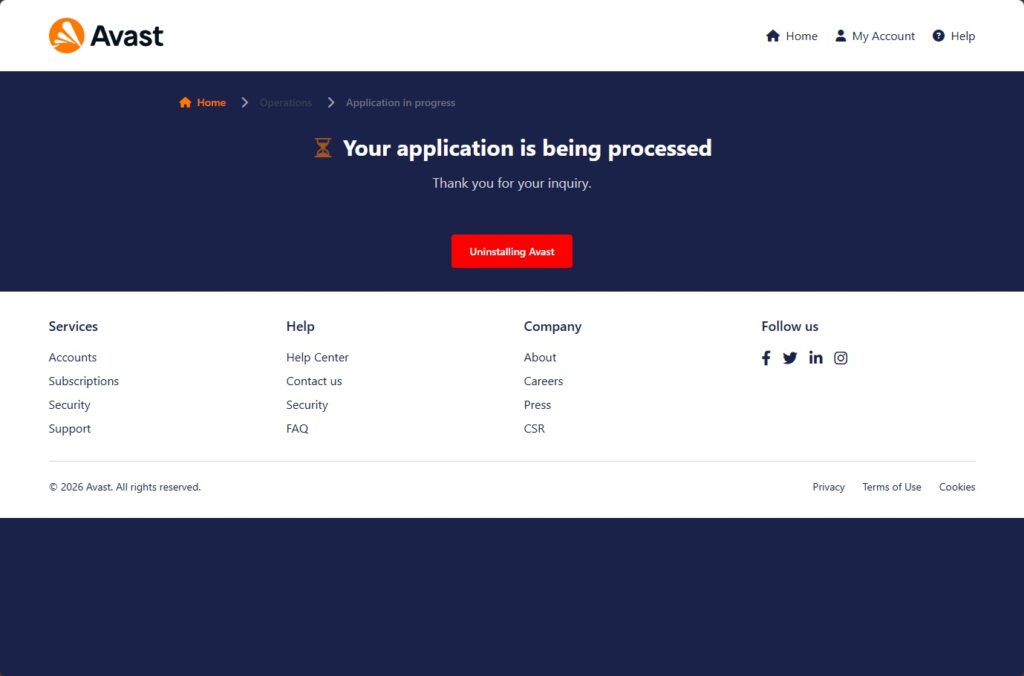
Luhn algorithm checks card validity client-side. Valid data POSTs as JSON to send.php. Tawk.to live chat (ID 689773de2f0f7c192611b3bf) nudges hesitants. Redirects to fake “uninstall Avast” page post-theft.
Victims include real customers, forgotten subs, scared non-users, even opportunists chasing free money. As of February 26, 2026, site active; Avast has no tie. RH-ISAC echoes: “Multi-stage modals and chat make it interactive fraud.”.
Urgency tricks skip suspicion. Banks hold payment data already; legit firms never re-ask full cards.
Scam Flow Table
| Step | Victim Action | Attacker Gain |
|---|---|---|
| Arrival | Sees €499.99 charge | Panic induced |
| Form 1 | Personal details | PII for sales |
| Modal | Card + CVV | Payment theft |
| Chat | Live reassurance | Nudges completion |
| Redirect | “Uninstall” prompt | Delays detection |
Key Indicators
Spot fakes fast.
- Unsolicited charge alerts.
- Full card re-request for refund.
- Timing contradictions (72h vs 48h).
- Tawk.to chat on Avast site.
- No official Avast login.
Victim Response Steps
Act now if hit.
- Call bank to cancel card.
- Dispute charges.
- Change linked passwords.
- Scan devices.
- Report to Avast support.
FAQ
Fake refund page steals cards via urgency and forms.
Credible subscription sum to provoke action.
No; they have your details already.
Fake via Tawk.to ID 689773de2f0f7c192611b3bf.
PII, full cards validated by Luhn algo.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages