Agent Tesla Phishing Campaign Uses Process Hollowing and Anti-Analysis to Steal Credentials

A phishing campaign delivers Agent Tesla malware via emails with business lures. It uses process hollowing and anti-analysis tricks to evade detection on Windows systems. Fortinet researchers uncovered this multi-stage attack in their threat report on February 25, 2026. The chain runs fully in memory. No files drop to disk.
Agent Tesla has targeted users since 2014. Cybercriminals sell it as Malware-as-a-Service. It grabs browser credentials, keystrokes, and email data. Attackers send it to their servers quietly. This version layers evasion to dodge endpoint tools.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
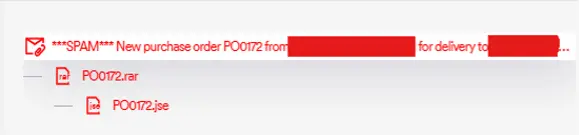
Emails mimic purchase orders. Subjects read like “New Purchase Order PO0172.” A RAR attachment holds PO0172.jse, an obfuscated JScript file. Email filters often allow .jse but block .exe. Victims open it. The chain starts automatically.
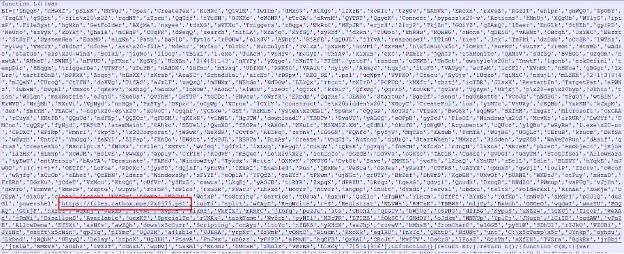
The JSE contacts catbox[.]moe for an encrypted PowerShell script. It decrypts with AES-CBC and PKCS7 padding right in memory. No disk writes happen. This unpacks the next loader.
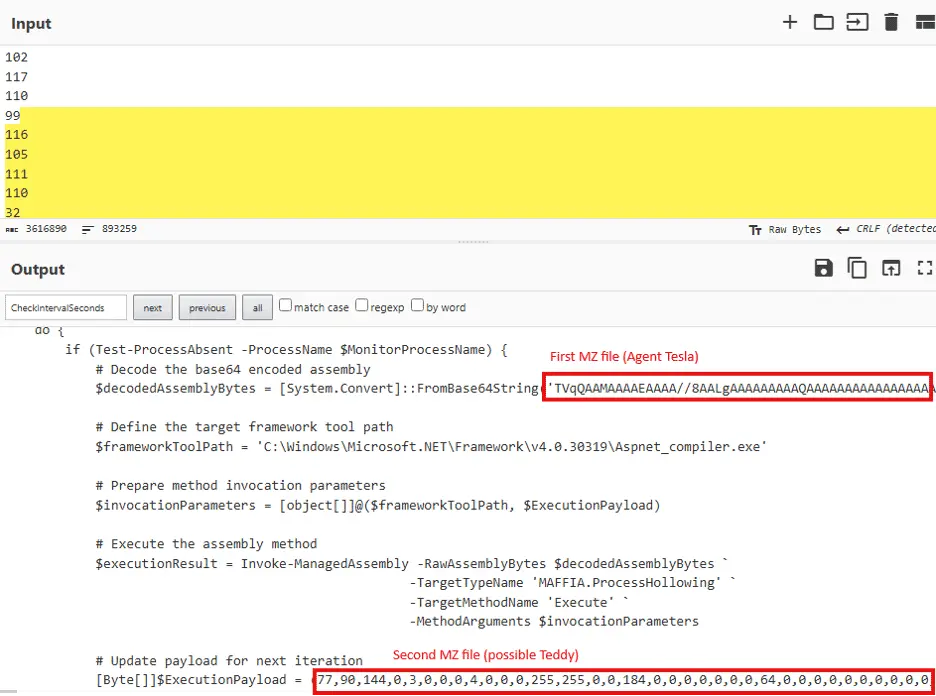
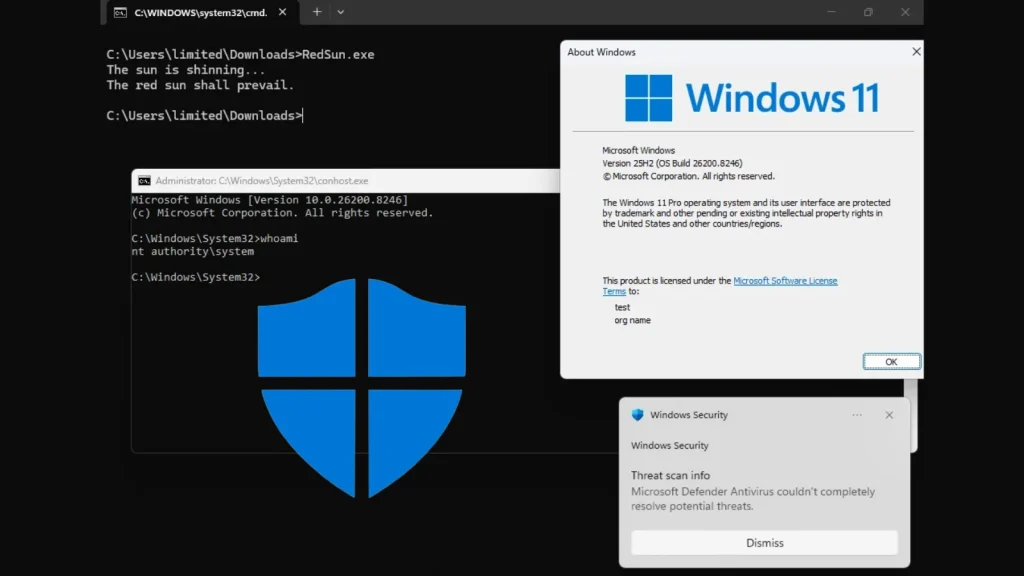
PowerShell then hollows aspnet_compiler.exe from C:\Windows\Microsoft.NET\Framework\v4.0.30319. It suspends the legit process. Clears its memory. Injects Agent Tesla instead. The malware hides as a trusted name.
Attack Chain Breakdown
- Stage 1: Phishing email with PO0172.rar → PO0172.jse.
- Stage 2: JSE downloads and decrypts PowerShell from catbox[.]moe.
- Stage 3: PowerShell performs in-memory AES decryption.
- Stage 4: Hollows aspnet_compiler.exe with .NET loader.
- Stage 5: Agent Tesla runs in memory, exfils via SMTP to mail[.]taikei-rmc-co[.]biz.
All stages avoid disk. Tools miss file-based signatures.
Evasion Techniques
Agent Tesla scans for sandboxes first. It queries WMI for VMware, VirtualBox, Hyper-V. Checks DLLs like snxhk.dll (Avast), SbieDll.dll (Sandboxie), cmdvrt32.dll (Comodo.
If detected, it quits. Otherwise, it steals:
- Browser cookies and credentials.
- Keystrokes.
- Email accounts.
- Packs as text files. Sends via SMTP.
Fortinet notes this shows pros handling commercial malware well.
Key Indicators of Compromise
| Type | Value |
|---|---|
| Phishing Domain | catbox[.]moe |
| C2 Server | mail[.]taikei-rmc-co[.]biz |
| Attachment | PO0172.rar / PO0172.jse |
| Hollowed Process | aspnet_compiler.exe |
| Decryption Func | Invoke-AESDecryption (AES-CBC) |
Block .jse attachments at email gateways. Microsoft recommends PowerShell logging in their security advisory.
Detection and Mitigation Steps
- Monitor PowerShell in-memory execution.
- Block RAR with scripts in email filters.
- Watch for aspnet_compiler.exe anomalies.
- Scan outbound SMTP for exfil.
- Use EDR with memory injection alerts.
Train staff on business email lures. Enforce least privilege on scripts.
Agent Tesla phishing, process hollowing attacks, and credential stealers like this demand layered defenses. Stay updated on Agent Tesla variants for 2026.
FAQ
Email → RAR/.jse → PowerShell download/decrypt → Process hollowing → In-memory payload.
Runs in memory only. Hollows trusted processes. Detects sandboxes via WMI/DLL checks.
Browser credentials, cookies, keystrokes, email details. Sends via SMTP.
Filter .jse/RAR emails. Log PowerShell. Block catbox[.]moe and taikei-rmc-co[.]biz.
Active since 2014. This uses advanced delivery per Fortinet’s report.
EDR like Microsoft Defender, CrowdStrike. Enable behavior analytics.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages