Vshell Emerges as a Cobalt‑Strike‑Style C2 Framework for Global Threat Actors
Vshell, a Go‑based command‑and‑control (C2) framework, has moved from a regional, Chinese‑language tool to a mainstream option for attackers worldwide. It offers many of the same features as Cobalt Strike but at a lower cost and with a simpler interface, making it attractive to mid‑tier and opportunistic threat actors. Censys researchers have documented thousands of internet‑facing Vshell deployments, showing that it is now embedded in real‑world campaigns rather than just lab or forum demos.
At its core, Vshell controls compromised Windows and Linux hosts, supports network pivoting, and enables lateral movement after initial access. It first appeared in 2021 as a lightweight C2 tied to the AntSword web shell, but version 3 explicitly marketed itself to Cobalt‑Strike users with the tagline: “Is Cobalt Strike difficult to use? Try Vshell instead!” This messaging positions Vshell as a budget‑friendly alternative to expensive commercial adversary‑simulation suites.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
How Vshell is being used in attacks
Vshell has appeared in several documented campaigns during 2025 and early 2026. Public threat reports link it to:
- Operation DRAGONCLONE, a multi‑stage intrusion campaign.
- The SNOWLIGHT activity cluster tied to UNC5174.
- A late‑2025 phishing campaign using Vshell as the primary post‑compromise framework.
These cases show that Vshell is not just a niche tool used by a single group. Multiple, independently attributed actors now rely on it for persistence, beaconing, and lateral movement across corporate networks. [Censys, public threat‑intel reports]
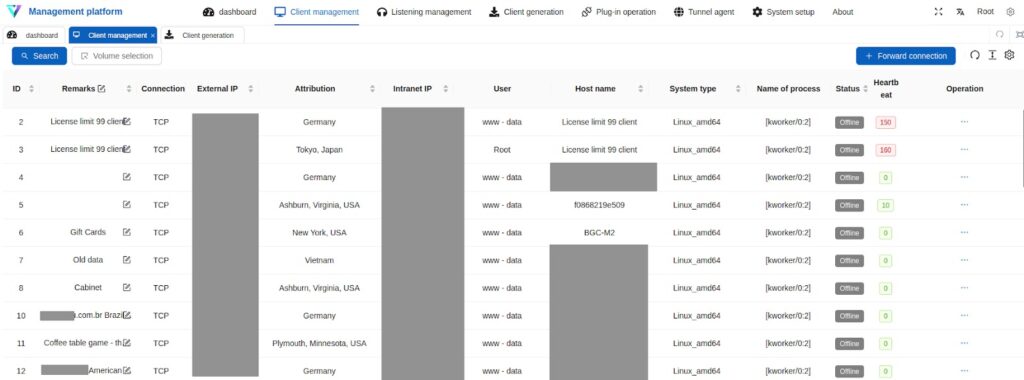
Censys mapping also revealed exposed Vshell panels on the open web, some of which showed hundreds of live agents connected at the same time. One captured panel displayed 286 active clients, each capable of acting as a relay for traffic tunneling and internal‑network pivoting. [Censys blog]
Version evolution and licensing
After its initial open‑ended release, Vshell matured into a more controlled product:
- Version 3 sharpened its Cobalt‑Strike‑like branding and added multi‑platform flexibility.
- Version 4 introduced:
- Licensing controls.
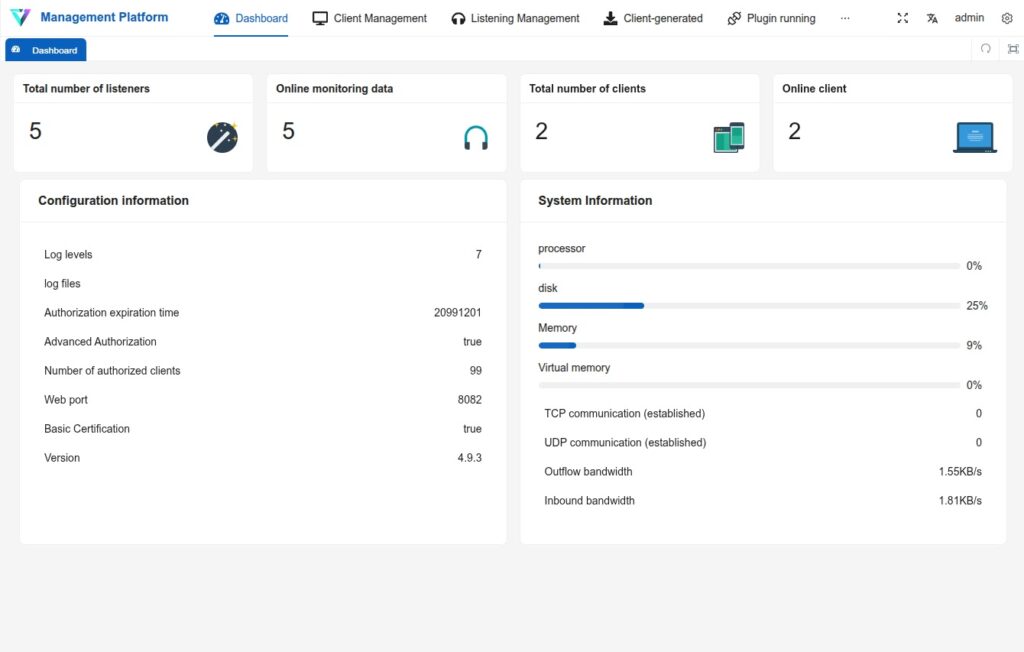
- A redesigned operator panel.
- nginx‑style impersonation that helps cover C2 traffic behind normal‑looking web‑server patterns.
Evidence suggests that development has continued in private channels after 2024, with the authors investing in long‑term evasion and stability. Censys observed over 850 active Vshell listeners through internet‑wide scans, a clear sign that it is widely deployed across public‑facing infrastructure.
Multi‑protocol C2 architecture
One of the main reasons Vshell is hard to block is its listener‑based design. Through a centralized “Listener Management” (监听管理) interface, operators can create multiple C2 channels across different protocols and ports. [Censys, tool documentation]
Vshell supports:
- TCP and KCP/UDP listeners, often defaulting to something like port 8084.
- WebSocket channels that look like normal web traffic.
- DNS‑based channels including plain DNS, DNS‑over‑HTTPS (DoH), and DNS‑over‑TLS (DoT).
- Object Storage System (OSS)‑style listeners via S3‑compatible buckets.
Many of these protocols allow the operator to shift C2 traffic into channels that defenders either ignore or cannot inspect without extra configuration. For example, DNS‑over‑HTTPS and DNS‑over‑TLS blend C2 into encrypted DNS queries that most default network‑monitoring setups do not decrypt or log.
Newer Vshell panels also use digest authentication instead of basic or overly obvious authentication tokens. This reduces the number of static, fingerprintable artifacts that defenders previously used to detect C2 traffic. As a result, operators can rotate configurations and listeners while evading simple pattern‑based rules.
How Vshell stacks up against Cobalt Strike
| Feature | Vshell behavior | Cobalt‑Strike pattern |
|---|---|---|
| Management model | Central controller with many agents. [Censys] | Teamserver‑style, multi‑agent control. [Cobalt Strike docs] |
| Post‑compromise features | Pivoting, lateral movement, tunneling. [Censys, threat reports] | Full post‑exploitation suite. [Cobalt Strike docs] |
| Cost and access | Lower‑cost, forum‑distributed framework. [Censys, underground forums] | Expensive commercial license. [Cobalt Strike pricing] |
| Listener protocols | TCP, KCP/UDP, WebSocket, DNS, DoH, DoT, OSS‑style buckets. [Censys] | HTTP/S, DNS, SMB, similar advanced channels. [Cobalt Strike docs] |
| Detection fingerprints | Reduced by nginx‑style impersonation and digest auth. [Censys] | Known signatures and plugin‑based evasion. [Community detections] |
Detection and defensive guidance
Defenders can no longer treat Vshell as a “local‑only” or “language‑specific” tool. Its public footprint and multi‑protocol design mean it can bypass simple perimeter blocks. Key recommendations:
- Monitor internet‑facing infrastructure: Look for unexpected web‑panel directories, obscure services on common HTTP‑adjacent ports such as 8084, and unusual nginx‑style or S3‑like endpoints.
- Inspect DNS‑based channels: Check for anomalous DNS, DNS‑over‑HTTPS, and DNS‑over‑TLS traffic patterns, particularly high‑entropy or repetitive queries that do not match internal lookups.
- Leverage NPS‑related detections: Because Vshell builds on ideas and structures similar to NPS‑style tunneling tools, existing NPS‑detection rules can often catch overlapping behavior.
- Run active threat‑hunting queries: Search logs and EDR data for outbound connections matching known Vshell listener patterns or unusual listener‑port combinations.
- Update Indicators of Compromise (IoC) feeds: Add observed Vshell C2 domains, IP ranges, and certificate hashes to your SIEM, EDR, and firewall block lists.
Given that Vshell is now part of real‑world campaigns, security teams should treat it as a standing entry in their C2 threat model. Where Cobalt Strike once dominated the commercial red‑team and offensive‑tool space, Vshell now represents a realistic, lightweight alternative that can be deployed quickly and quietly across compromised networks.
FAQ
Vshell is a Go‑based C2 framework that lets attackers manage multiple compromised hosts, pivot through networks, and tunnel traffic. It is cheaper and easier to use than Cobalt Strike, which is a more expensive, feature‑rich commercial platform.
Vshell targets both Windows and Linux hosts, giving threat actors flexibility after initial access.
Censys scans identified over 850 active Vshell listeners and exposed panels with hundreds of agents, showing that it has moved beyond niche use into mainstream threat‑tool arsenals.
Vshell supports TCP, UDP, WebSocket, DNS, DNS‑over‑HTTPS, DNS‑over‑TLS, and S3‑style object‑storage‑style listeners, many of which blend with legitimate traffic.
Organizations should monitor web‑server logs, DNS‑based protocols, unusual listener ports, and NPS‑like tunneling patterns, then enrich these with IoCs from public research and internal threat‑hunting.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages