Malicious Go Crypto Module Targets Developers

A malicious Go module mimicking the trusted golang.org/x/crypto library steals passwords and deploys the Rekoobe backdoor in developer environments. Security researchers at Socket.dev uncovered this supply chain attack. It poses a major threat to Go-based Linux systems.
Attack Details
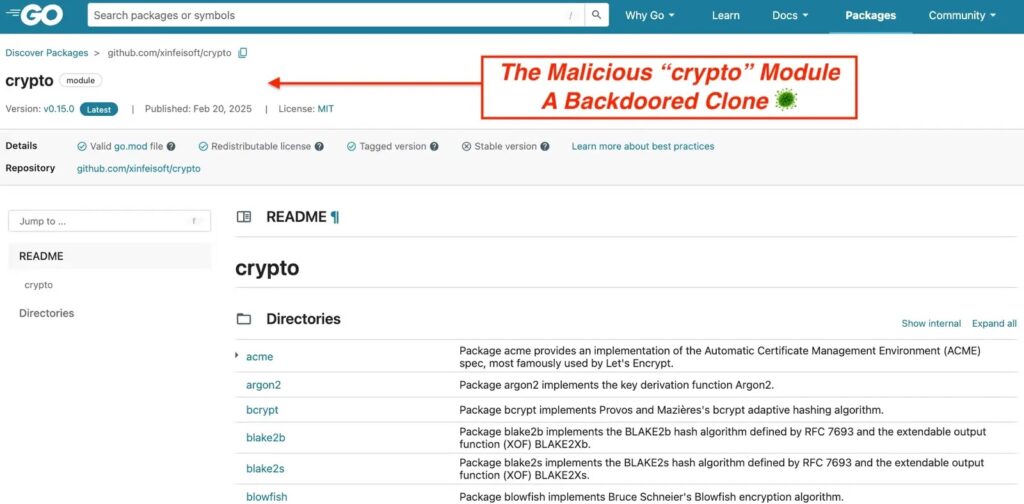
Threat actors published github at version v0.15.0 on February 20, 2025. This module copies the structure of the legitimate golang.org/x/crypto, including subpackages like bcrypt, argon2, acme, and ssh. Developers importing it face hidden risks during routine dependency updates.
The backdoor hides in the ssh/terminal/terminal.go file. It modifies the ReadPassword function, which tools use for SSH passphrases, database logins, and API keys. The code activates only during interactive sessions, staying dormant in automated tests.
How the Backdoor Works
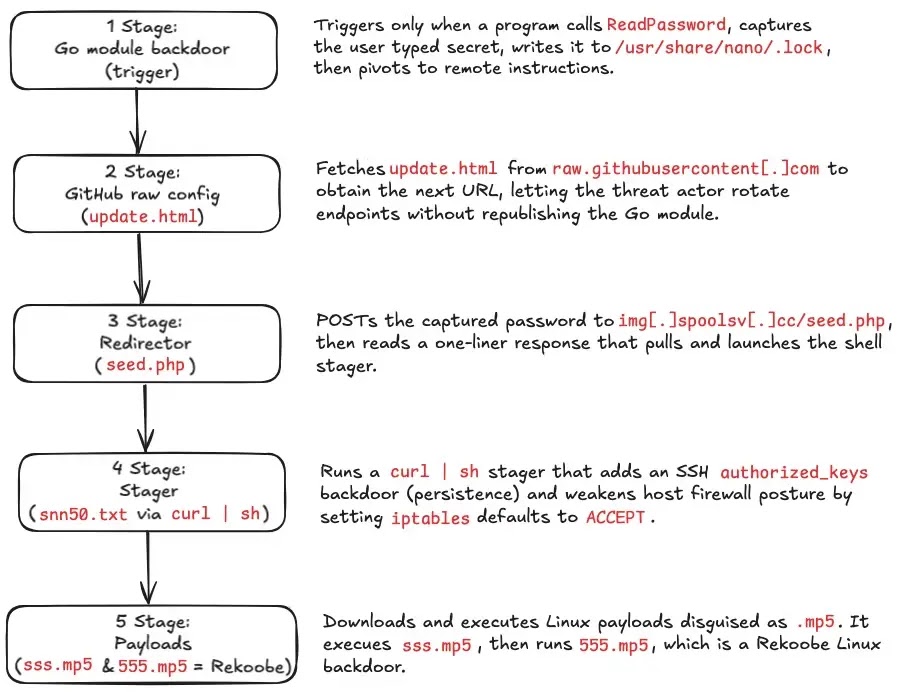
When ReadPassword runs, it captures credentials in plaintext. The data saves to /usr/share/nano/.lock, a sneaky location. Next, it pulls a staging URL from the attacker’s GitHub repo and sends the password to a dynamic endpoint.
A shell script downloads from there. This starts a multi-stage dropper chain. The Go security team blocked the module at the public proxy with a 403 SECURITY ERROR.
- Stage 1: Fetches update.html from GitHub, redirects to img.spoolsv.cc/seed.php.
- Stage 2: curl | sh grabs snn50.txt, the main stager.
- Stage 3: Adds attacker SSH key to /home/ubuntu/.ssh/authorized_keys.
- Stage 4: Sets iptables to ACCEPT, disables firewall protections.
- Stage 5: Downloads and runs sss.mp5 (recon loader) and 555.mp5 (Rekoobe backdoor), then deletes them.
Rekoobe Backdoor Features
Rekoobe links to APT31 (Zirconium) with roots in Tiny SHell. It connects to 154.84.63.184 on TCP port 443 using custom encryption to mimic HTTPS. This grants persistent remote access.
| Component | Function | Indicators |
|---|---|---|
| ReadPassword hook | Steals plaintext credentials | Writes to /usr/share/nano/.lock |
| snn50.txt stager | Prepares host | Modifies authorized_keys, iptables |
| 555.mp5 | Rekoobe backdoor | C2: 154.84.63.184:443 |
| sss.mp5 | Recon loader | Custom traffic, self-deletes |
Impact on Teams
Go developers on Linux cloud VMs, CI/CD pipelines, and bastion hosts face the highest risks. Compromised apps harvest credentials before hashing. This exposes SSH keys, DB passwords, and APIs.
Teams must review go.mod and go.sum for changes. Any new crypto dependency needs scrutiny.
Defense Steps
Monitor these signs of compromise:
- Unauthorized writes to /usr/share/nano/.lock.
- Changes to .ssh/authorized_keys.
- iptables resets to ACCEPT.
- Traffic to img.spoolsv.cc or img.spoolsv.net.
- GitHub Raw fetches followed by HTTP POSTs.
Block listed domains. Audit dependencies regularly. Socket.dev flagged this via AI scanning.
FAQ
Socket.dev’s AI Scanner spotted the backdoor in ssh/terminal/terminal.go.
No. The Go proxy blocks it with a 403 error.
Linux-based Go apps in cloud VMs, CI/CD, or dev hosts using ReadPassword.
Via added SSH key in authorized_keys, surviving password changes.
Scan systems for indicators, rotate credentials, and audit go files now.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages