North Korean APT37 Ruby Jumper Campaign Targets Air-Gapped Systems

North Korean APT37 (ScarCruft, Ruby Sleet) deployed Ruby Jumper malware to infect air-gapped networks. The campaign uses five new tools: RESTLEAF, SNAKEDROPPER, THUMBSBD, VIRUSTASK, and FOOTWINE. Attackers bridge internet-connected and isolated systems through USB drives. Zscaler ThreatLabz uncovered the operation targeting Arabic-speaking users.
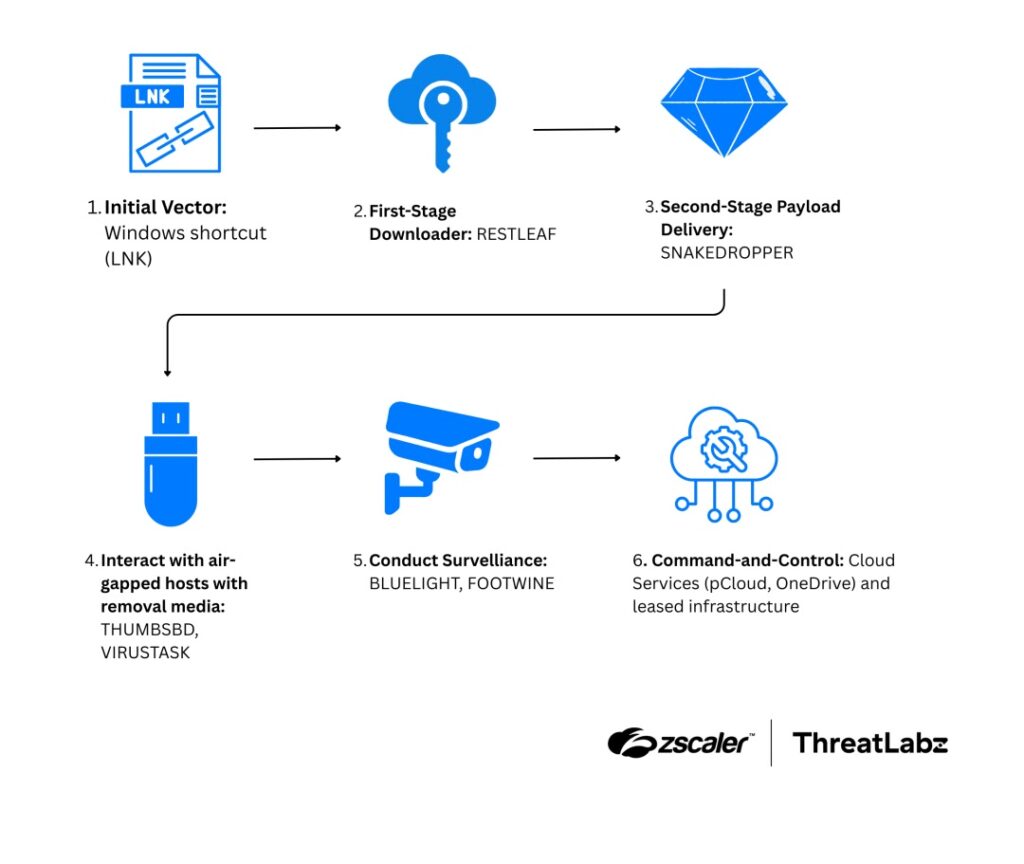
Malicious LNK files disguised as Palestine-Israel conflict documents start infections. RESTLEAF downloads payloads. SNAKEDROPPER deploys Ruby 3.3.0 runtime as usbspeed.exe. THUMBSBD and VIRUSTASK turn removable media into C2 bridges. FOOTWINE provides keylogging, audio/video capture, and shell access.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
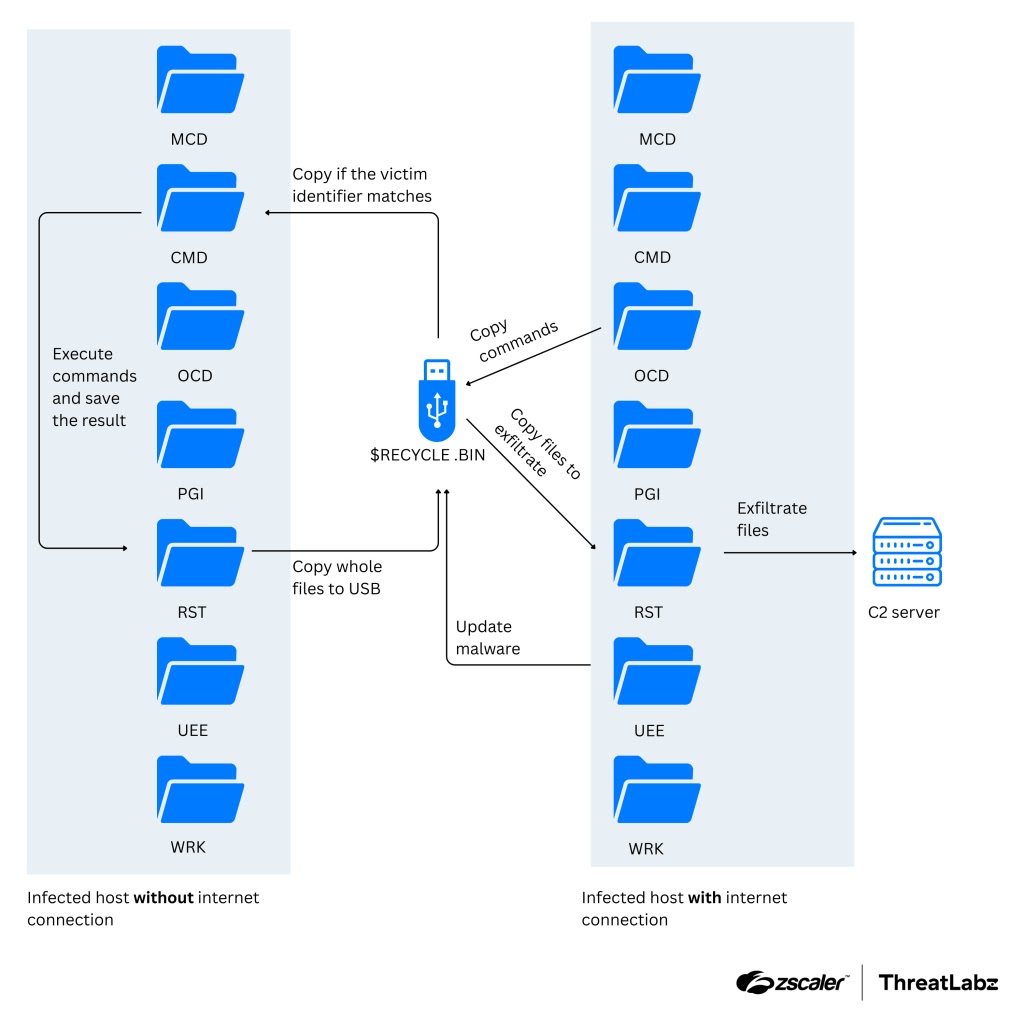
Air-gapped systems lose isolation. USB drives carry hidden commands in $RECYCLE.BIN. Attackers exfiltrate data and execute commands across security boundaries. Cloud services like Zoho WorkDrive serve as C2 channels.
Attack Chain Components
Each stage serves a specific purpose in the air-gap bridge.
| Malware Component | Role | Key Features |
|---|---|---|
| RESTLEAF | First-stage downloader | LNK → payload delivery |
| SNAKEDROPPER | Ruby runtime deployment | usbspeed.exe disguise, persistence |
| THUMBSBD | USB bridge backdoor | $RECYCLE.BIN command staging |
| VIRUSTASK | File replacement | LNK shortcuts replace legit files |
| FOOTWINE | Surveillance implant | Keylogger, AV, shell access |
C2 Infrastructure: Zoho WorkDrive, OneDrive, Google Drive, pCloud
Air-Gap Bridge Mechanics
THUMBSBD creates bidirectional USB communication:
- Internet-facing PC: THUMBSBD writes encrypted commands to USB $RECYCLE.BIN
- Air-gapped PC: THUMBSBD reads/decrypts (single-byte XOR) and executes
- Data exfil: Results written back to USB for next internet connection
- VIRUSTASK spreads: Replaces user files with malicious LNKs
Rubyupdatecheck scheduled task runs every 5 minutes for persistence.
Technical Indicators
Hunt these across environments:
| Indicator Type | Value/Path |
|---|---|
| Scheduled Task | rubyupdatecheck (5-min interval) |
| Registry Key | HKCU\SOFTWARE\Microsoft\TnGtp |
| File Paths | %PROGRAMDATA%\usbspeed.exe |
| USB Directories | $RECYCLE.BIN, $RECYCLE.BIN.USER (hidden) |
| Processes | Ruby 3.3.0 runtime processes |
Target Profile
Arabic-language decoys suggest Mideast focus. APT37 history includes:
- Government entities
- Defense organizations
- DPRK interest targets
- Korean Peninsula watchers
Defense Strategy
Immediate Actions:
- Block cloud storage C2 (Zoho WorkDrive, OneDrive, etc.)
- Disable autorun on removable media
- Deploy USB device control policies
- Hunt scheduled tasks and registry keys
Endpoint Hunting:
filename contains "usbspeed.exe" OR "rubyupdatecheck"
path contains "$RECYCLE.BIN" on removable drives
registry contains "TnGtp"
Physical Security:
- Escort USB usage on air-gapped systems
- Scan removable media before air-gap insertion
- Deploy air-gap data diodes where possible
FAQ
USB drives bridge commands via hidden $RECYCLE.BIN files.
APT37 (ScarCruft, Ruby Sleet, Velvet Chollima).
Zoho WorkDrive, OneDrive, Google Drive, pCloud.
THUMBSBD writes commands, VIRUSTASK spreads infection.
rubyupdatecheck scheduled task runs every 5 minutes.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages