Hackers Use CyberStrikeAI Tool to Hit Fortinet FortiGate Devices

Threat actors are using an AI‑driven offensive security tool called CyberStrikeAI to breach Fortinet FortiGate firewalls and other edge network devices. This open‑source platform, written in Go and hosted on GitHub under the alias “Ed1s0nZ,” automates reconnaissance, exploitation, and campaign management at scale.
The tool has been spotted in real‑world attacks targeting FortiGate appliances across multiple regions, with scanning and command‑and‑control traffic tied to servers linked to Chinese‑speaking areas such as China, Singapore, and Hong Kong. Researchers describe CyberStrikeAI as a significant escalation in how AI is being weaponized to run automated, large‑scale network attacks.
What CyberStrikeAI Does
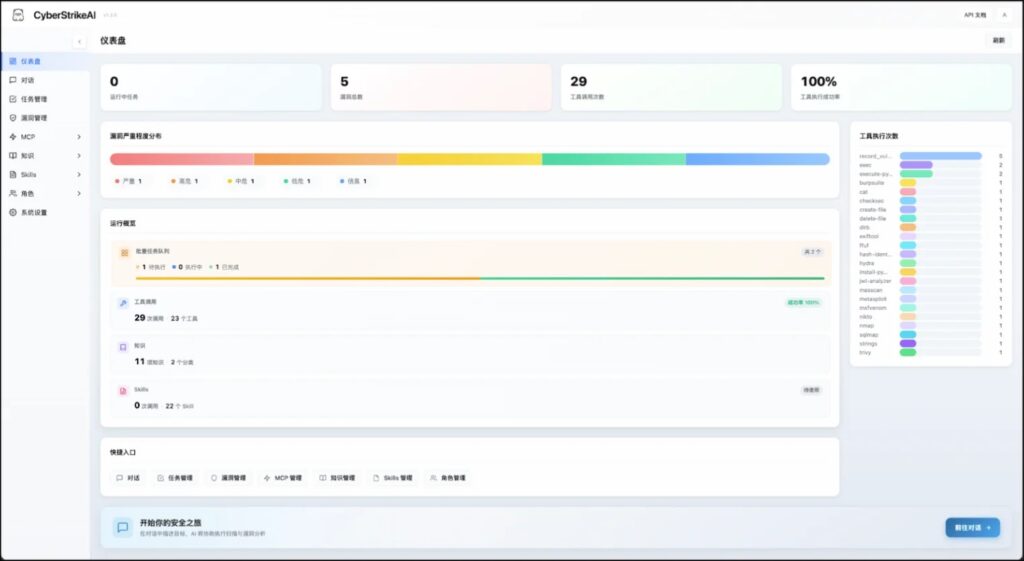
CyberStrikeAI is advertised as an “AI‑native security testing platform” built on Go. It bundles more than 100 existing security tools and layers on an intelligent orchestration engine, role‑based testing, and lifecycle management via a centralized web dashboard.
Operators can use the dashboard to:
- Launch automated scans against IP ranges and subnets.
- Coordinate multiple attack components (scanning, exploitation, post‑exploitation).
- Track active campaigns and monitor targets in near real time.
Because much of the logic is driven by AI‑assisted workflows, the tool lowers the technical bar for attackers who want to run complex FortiGate‑focused campaigns without deep manual expertise.
How It Targets FortiGate Devices
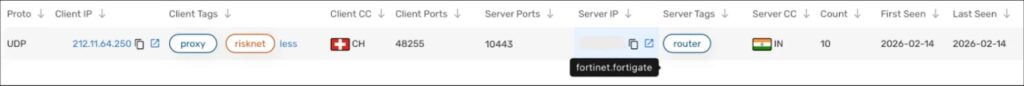
Analysis of infrastructure linked to CyberStrikeAI shows traffic patterns and service banners that match the platform’s name, such as the “CyberStrikeAI” banner on an open port at 212.11.64.250, which researchers have associated with the campaign. NetFlow monitoring reveals this IP and others repeatedly communicating with Fortinet FortiGate firewalls, carrying out reconnaissance and likely exploitation steps.
The typical attack flow looks like this:
- Scan large IP blocks to find reachable FortiGate devices.
- Probe for known or zero‑day vulnerabilities (for example, misconfigurations, weak authentication, or unpatched CVEs).
- Use AI‑guided workflows to select and chain exploits, then set up persistent access.
Because the tool can orchestrate follow‑up actions automatically, compromised devices may be used for lateral movement, data exfiltration, or onward pivoting into internal networks.
Who Is Behind CyberStrikeAI
The developer behind CyberStrikeAI, “Ed1s0nZ,” has a history of building AI‑assisted offensive tools. Their GitHub profile includes projects such as:
- PrivHunterAI: AI‑driven privilege escalation detection.
- InfiltrateX: automated privilege escalation vulnerability scanner.
- watermark‑tool: steganographic document watermarking utility.
Documents and forum posts indicate that this same developer has interacted with Chinese state‑linked entities. In December 2025, CyberStrikeAI was submitted to the Starlink Project managed by Knownsec 404, a private firm with documented ties to the Chinese Ministry of State Security (MSS) and the People’s Liberation Army. In January 2026, the developer also claimed a “Level 2 Contribution Award” from the National Vulnerability Database of China (CNNVD), another MSS‑overseen program often used to catalog and stockpile vulnerabilities.
Shortly after CyberStrikeAI drew public attention, the CNNVD reference was removed from the GitHub profile, suggesting an attempt to downplay its state‑linked background as the tool gained notoriety.
Growth and Geographic Spread
CyberStrikeAI was first created on GitHub in November 2025, but deployments remained sparse until early 2026. Between January 20 and February 26, 2026, researchers tracked 21 distinct IP addresses hosting the platform, with many of these servers located in or often routed through Chinese‑speaking regions.
This sharp increase in deployment suggests that:
- The tool is moving from a proof‑of‑concept phase into active, sustained operations.
- It is being adopted by both independent hacking groups and possibly state‑linked actors with access to similar infrastructure.
The concentration in China, Singapore, and Hong Kong also aligns with the developer’s known background and with the broader ecosystem of tools and programs that support Chinese‑aligned cyber operations.
Key Similar Tools and Features
| Tool name | Primary purpose | AI‑assisted features |
|---|---|---|
| CyberStrikeAI | Automated network exploitation platform | AI‑driven orchestration, 100+ tools |
| PrivHunterAI | Privilege escalation detection | AI‑based traffic analysis, pattern matching |
| InfiltrateX | Privilege escalation vulnerability scanner | AI‑guided scanning and prioritization |
| watermark‑tool | Steganographic document watermarking | AI‑assisted watermark embedding/analysis |
This family of tools shows a clear trend toward using AI to speed up exploitation chains, reduce manual errors, and make campaigns more repeatable across many targets.
Risks for Organizations Using FortiGate Devices
Organizations that rely on Fortinet FortiGate firewalls face several risks if they sit within the observed attack scope:
- Increased likelihood of automated scanning and exploitation attempts.
- Use of discovered devices as staging points for lateral movement inside the internal network.
- Potential theft of credentials, VPN configurations, and internal traffic logs.
Because CyberStrikeAI is AI‑native and can adjust its behavior based on target responses, defenders may see fewer repetitive, easily filtered signatures. This raises the importance of behavior‑based detection and proactive hardening.
Recommended Defensive Actions
Defenders should treat CyberStrikeAI‑linked activity as evidence of a highly automated, AI‑assisted attack surface. Some practical steps include:
- Applying the latest Fortinet patches and firmware updates for FortiGate devices.
- Disabling or restricting unused services and ports that attackers commonly scan.
- Enforcing strong multi‑factor authentication for all admin and VPN access tied to FortiGate firewalls.
Network teams can also:
- Monitor for traffic to known IOCs, such as the IP address 212.11.64.250 and similar ranges tied to CyberStrikeAI.
- Use EDR and SIEM rules to flag unusual outbound traffic patterns from firewall‑facing segments.
- Regularly audit firewall configurations and review logs for signs of unauthorized access or policy changes.
Organizations should also treat any AI‑assisted security or offensive tooling in the wild as a strong signal that attackers are raising their automation level and may adjust tactics quickly.
FAQ
It automates scanning, exploitation, and campaign management against edge devices, including FortiGate firewalls, using AI‑driven workflows and existing offensive tools.
Public reports focus more on the platform’s use of known and zero‑day vulnerabilities in general rather than a single CVE, but FortiGate‑specific vulnerabilities are among its likely targets.
Any organization running exposed FortiGate devices reachable from the internet, especially those with outdated firmware or weak authentication practices.
Traditional tools can help, but CyberStrikeAI’s AI‑driven, adaptive behavior means organizations should combine signature‑based detection with behavioral monitoring and continuous patching.
Review FortiGate logs for repeated scans and connection attempts from IP ranges associated with the 21 tracked CyberStrikeAI‑hosting servers, and search for unusual outbound traffic from the firewall segment.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages