To reduce MTTR and business risk, start with better SOC collaboration
Modern SOC performance comes down to time and impact. You need fast containment. You also need decisions you can defend. Many teams buy more tools, yet workflow friction still slows response.
The biggest drag often sits between alert triage and incident response. Tier 1 may flag something quickly, but Tier 2 or IR still has to redo parts of the investigation. That duplication increases cost, increases fatigue, and increases business exposure.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Better collaboration reduces MTTR because it removes waste. It also improves risk outcomes because the team spends more time on the right incidents.
Where collaboration breaks down and why it raises risk
SOC tiers often work side-by-side without enough shared context. Triage analysts might escalate an alert with partial evidence. IR then re-runs the same checks, pulls the same logs, and rebuilds the timeline again.
That gap shows up in predictable ways:
- Duplicate investigations: IR repeats triage work because the handoff lacks proof and clarity.
- Interpretation drift: analysts describe the same event differently because they use different evidence sets.
- Slower response: unclear ownership and incomplete context stretch the investigation cycle.
These problems do not stay inside the SOC. They translate into longer dwell time, wider blast radius, and higher probability of operational downtime.
What “good collaboration” looks like in a SOC
Effective SOC collaboration means every escalation arrives with enough context for the next team to act. It also means each tier knows its responsibilities and can trust the work that came before.
A workable model usually includes:
- A shared evidence standard for escalations
- A consistent set of required artifacts for Tier 1 to Tier 2 handoffs
- Clear decision points for containment, isolation, and remediation
- A feedback loop so IR can improve triage rules and playbooks
You can often get these gains without replacing your entire stack. You can add a workflow layer that increases investigation depth early and standardizes what moves downstream.
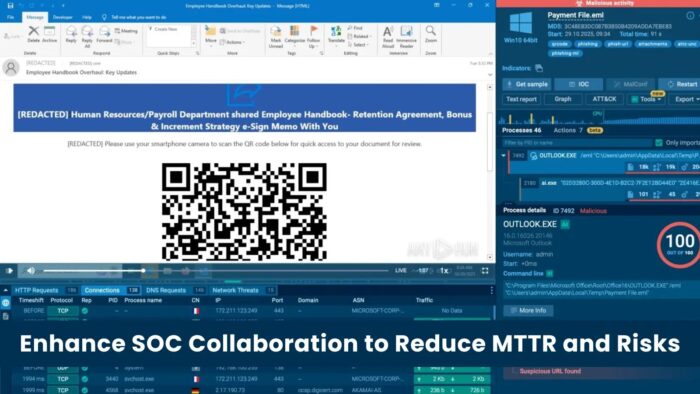
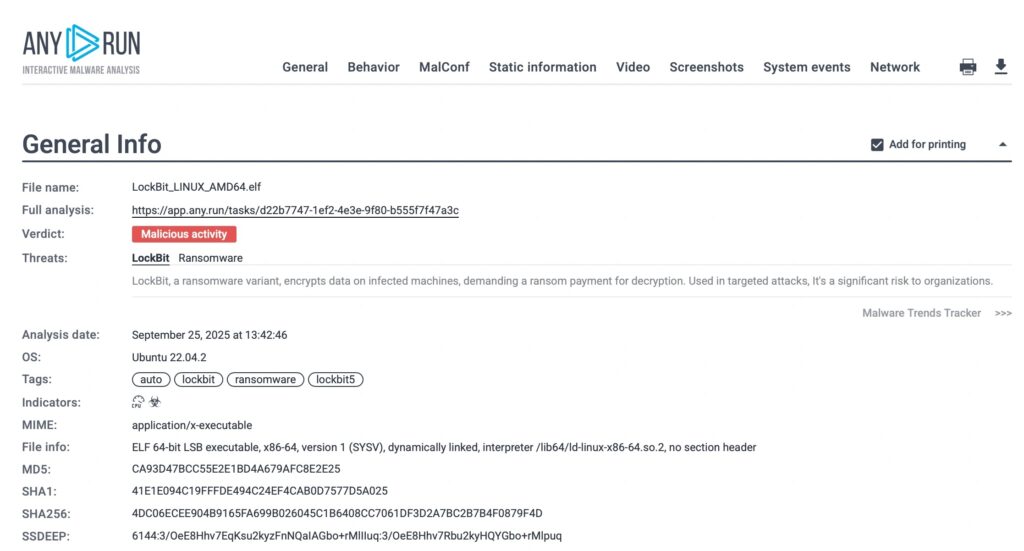
Operationalizing collaboration with an interactive sandbox
Interactive sandboxing can improve collaboration when it shortens the time to understand what an alert actually does. It can also standardize reporting so Tier 2 and IR can trust the evidence.
ANY.RUN positions its Interactive Sandbox as a workflow accelerator rather than an extra console. It focuses on fast validation, consistent enrichment, and reports that work as handoff packages.
1) Automation that scales inside existing workflows
Automation helps only when it fits the existing flow. If analysts have to switch tools and reformat evidence, speed gains disappear.
ANY.RUN says it supports triage-to-response workflows through automated analysis, AI-assisted insights, and integrations that push results into tools SOC teams already use.
- Automated interactivity that simulates user behavior to expose evasive threats
- AI-assisted summaries that surface key behavioral indicators
- Integrations that support SIEM and SOAR workflows
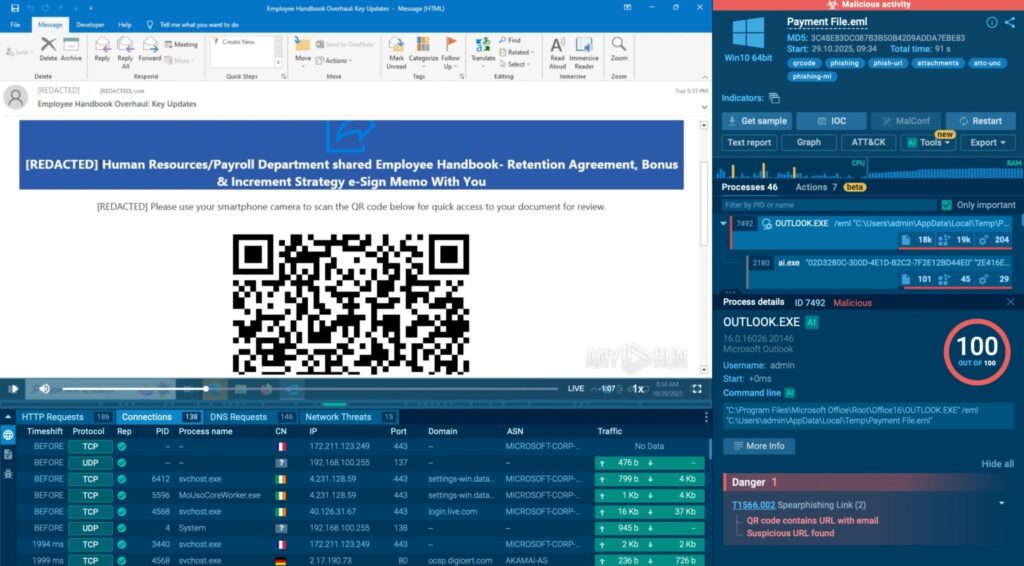
2) Response-ready reports that reduce rework
A strong handoff report does two jobs. It explains what happened. It also provides artifacts IR can act on quickly.
ANY.RUN says it generates structured reports that capture behavioral evidence, indicators, and a timeline that supports faster escalation decisions.
3) Shared visibility that improves consistency
Collaboration improves when teams see the same evidence and can review each other’s work. That reduces interpretation drift and improves coaching across tiers.
ANY.RUN’s Teamwork features aim to support shared visibility, role-based access, and analysis review across teammates.
Collaboration impact metrics
| Operational metric | Typical challenge without structured collaboration | Claimed impact with workflow support like ANY.RUN |
|---|---|---|
| Tier 1 workload | Repetitive enrichment and manual validation | Reduced overhead through automation and integrated enrichment |
| Tier 1 to Tier 2 escalations | Incomplete context causes re-analysis | Fewer misinterpretations due to standardized evidence packages |
| MTTR | Fragmented workflows prolong investigations | Faster resolution when teams share a single investigation context |
These outcomes depend on process maturity, rule quality, and integration depth. The main value comes from removing duplicate work and improving escalation quality.
Implementation checklist for SOC leaders
- Define a minimum evidence package for every escalation.
- Require a short narrative plus machine-readable indicators.
- Set a single owner for each investigation stage.
- Add a feedback loop where IR updates triage playbooks weekly.
- Measure escalation quality, not just alert volume.
- Treat collaboration as a control, not a soft skill.
FAQ
Broken handoffs between triage and incident response often force repeated investigations and slow containment.
Standardize escalation evidence, tighten ownership, and embed early-stage analysis that produces response-ready reports.
Sandboxing can validate behavior early and produce artifacts that reduce rework downstream, especially when it integrates into SIEM and SOAR workflows.
AI helps when it speeds triage decisions and highlights key behavior and indicators without adding noise.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages