Alleged exploit sale for patched Windows RDS flaw raises fresh concern, but public proof remains limited

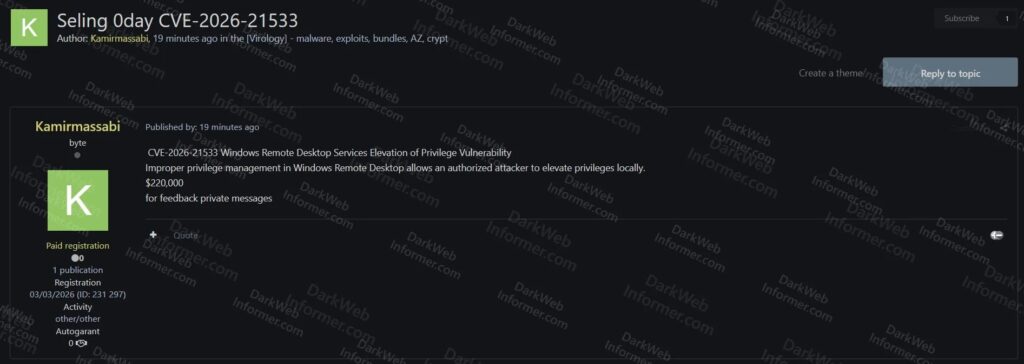
A dark web post is claiming to sell an exploit for CVE-2026-21533, a Windows Remote Desktop Services elevation-of-privilege flaw that Microsoft disclosed and patched on February 10, 2026. The seller, highlighted by Dark Web Informer, allegedly wants $220,000 for the exploit. But that sale claim remains unverified in public, so the safer framing is that a threat actor is advertising an exploit for a bug that Microsoft and CISA already treat as actively exploited in the wild.
That distinction matters because the vulnerability itself is real and already serious without the forum listing. Microsoft assigned CVE-2026-21533 to an improper privilege management flaw in Windows Remote Desktop Services, and the CVE record says an authorized attacker can elevate privileges locally. NVD also shows the bug is in CISA’s Known Exploited Vulnerabilities catalog, which means U.S. authorities already had evidence of active exploitation before this alleged sale surfaced.
What is confirmed
CVE-2026-21533 was published on February 10, 2026. The public CVE record describes it as an improper privilege management issue in Windows Remote Desktop that allows local privilege escalation. NVD shows the vulnerability carries a high-severity score and notes its inclusion in CISA’s KEV catalog.
CISA’s KEV listing is the strongest public signal here. NVD’s entry shows the flaw was added to KEV on February 10, 2026, with a remediation due date of March 3, 2026, for federal agencies. That means defenders should treat the issue as already weaponized, regardless of whether the dark web seller actually possesses a reliable exploit.
What is only alleged
The claim that someone is selling a working “0day” for $220,000 comes from a Dark Web Informer post on X. That post says a threat actor is advertising an exploit for CVE-2026-21533, but it does not publicly prove that the seller has a functional, exclusive, or reliable exploit. The vulnerability also is not a true zero-day anymore in the normal defensive sense, because Microsoft disclosed and patched it in February.
So the strongest version of the story is not “hackers are selling a new zero-day.” It is “a threat actor claims to be selling an exploit for a recently patched and already exploited Windows RDS privilege-escalation bug.” That wording stays closer to what the public evidence supports.
Why enterprises should still care
This bug affects Windows Remote Desktop Services and enables local privilege escalation, which can be highly valuable after initial access. Even though it is not a remote code execution flaw on its own, local elevation bugs often help attackers turn limited footholds into SYSTEM-level control on compromised machines. Several security summaries published after February Patch Tuesday described the flaw as allowing attackers to gain SYSTEM privileges.
The KEV status raises the urgency further. Once CISA adds a Microsoft bug to the KEV catalog, defenders should assume attackers are already using it somewhere in real operations, even if public reporting does not yet describe every campaign or exploit chain.
Key details
| Item | Verified detail |
|---|---|
| CVE | CVE-2026-21533 |
| Component | Windows Remote Desktop Services / Windows Remote Desktop |
| Issue type | Improper privilege management leading to local privilege escalation |
| Public status | Patched by Microsoft in February 2026 |
| CISA KEV status | Yes, listed as actively exploited |
| Dark web claim | Alleged exploit sale for $220,000 reported by Dark Web Informer |
What organizations should do now
The first priority is patching. Since Microsoft already fixed the flaw and CISA already flagged it as exploited, any exposed or unpatched Windows systems in scope should be treated as high priority for remediation.
Security teams should also review recent privilege-escalation activity on Windows endpoints, especially on systems where Remote Desktop Services is present and where attackers may already have user-level access. This is an inference from the flaw’s local privilege-escalation nature and KEV status, not a separate public statement about a specific detection rule.
If RDS is not needed, disabling or restricting it reduces attack surface. If it is needed, limit access to trusted admins and monitored management paths, and make sure EDR coverage can detect suspicious privilege-escalation behavior after initial compromise. That guidance follows from the vulnerability class and CISA’s remediation posture.
FAQ
Not anymore. The flaw was publicly disclosed and patched by Microsoft on February 10, 2026, so calling it a “0day” in March 2026 reflects the seller’s forum language, not the normal defensive meaning.
Publicly, the strongest confirmation comes through CISA’s Known Exploited Vulnerabilities process. NVD shows CVE-2026-21533 is in the KEV catalog, which means U.S. authorities had evidence of exploitation in the wild.
No. Public reporting only supports that a threat actor claimed to be selling an exploit. There is no public proof that the seller has a working or exclusive exploit.
It allows an authorized attacker to elevate privileges locally on a Windows system. That can help turn a limited compromise into full SYSTEM-level control.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages