New KadNap botnet hijacks ASUS routers and turns them into criminal proxy nodes

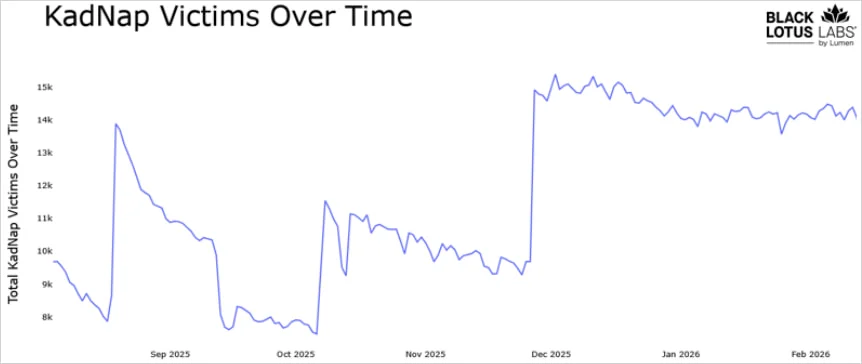
A newly tracked botnet named KadNap is hijacking ASUS routers and other edge networking devices, then using them to relay malicious traffic for a cybercrime proxy service. Researchers at Lumen’s Black Lotus Labs say they have monitored the network since August 2025 and now estimate it has grown to more than 14,000 infected devices.
The campaign matters because it does not just infect a router and stop there. It folds the device into a peer-to-peer system that helps hide the real command infrastructure, then sells access through a proxy service that researchers link to Doppelganger, which they believe may be a rebrand of the older Faceless operation tied to TheMoon malware.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Black Lotus Labs says KadNap mainly targets ASUS hardware, though the operators also hit other edge devices. More than 60% of observed victims sit in the United States, with additional concentrations in Taiwan, Hong Kong, and Russia. That geographic spread shows this is not a small regional campaign. It is a live botnet with enough scale to support criminal traffic routing at volume.
What makes KadNap stand out is the way it hides. Instead of depending on a simple, fixed command server list, the malware uses a custom version of the Kademlia distributed hash table protocol. In practice, that gives infected devices a way to discover peers and locate control infrastructure through a decentralized system, which makes traditional takedowns and blocklists less effective.
Researchers say the infection chain starts with a shell script named aic.sh pulled from an external server. That script sets persistence through a cron job that re-runs at the 55-minute mark of every hour, then downloads an ELF binary named kad. Black Lotus Labs also found ARM and MIPS samples, which suggests the operators built KadNap to run across a range of router-class hardware.
After installation, the malware checks the device’s external IP address and reaches out to multiple NTP servers to collect the current time and uptime. Researchers say those values help the malware generate data used in its peer discovery process. That extra step gives the botnet more resilience and makes the network harder to map quickly.
Lumen says it has already blocked traffic to and from the identified control infrastructure on its own network. The company also says it will publish indicators of compromise into public feeds so defenders can disrupt the botnet elsewhere. That action should help, but it does not mean the threat has disappeared across the wider internet.
For ASUS router owners, the immediate takeaway is simple. This report does not say every ASUS router is compromised, but it does show that exposed, poorly secured, or outdated edge devices remain prime targets for proxy botnets. ASUS’ own guidance tells users to keep firmware up to date, use separate strong passwords, keep the firewall enabled, and disable WAN access unless they truly need it.
KadNap at a glance
| Item | What researchers found |
|---|---|
| Malware name | KadNap |
| Primary targets | ASUS routers, plus other edge networking devices |
| Botnet size | More than 14,000 infected devices |
| Activity tracked since | August 2025 |
| Core technique | Custom Kademlia DHT-based peer discovery |
| Infection method | Shell script downloader, cron persistence, ELF payload |
| Criminal use | Proxy network access sold through Doppelganger |
| Defender action so far | Lumen blocked identified control traffic on its own network |
Source basis: Black Lotus Labs at Lumen.

Why this botnet is dangerous
- It turns home and small office routers into relay points for malicious traffic.
- It hides parts of its control system inside a peer-to-peer design.
- It appears linked to a criminal proxy business, not just one-off intrusion activity.
- It can make abuse look like it came from an innocent victim’s IP address.

What ASUS users should do now
- Update router firmware to the latest version available. ASUS says new firmware often includes security fixes.
- Use separate passwords for Wi-Fi and the router admin panel.
- Turn off WAN or remote management unless you absolutely need it. ASUS says that feature stays disabled by default and should remain off when possible.
- Keep the router firewall enabled.
- Replace unsupported hardware if it no longer receives updates. The FBI warned in 2025 that cybercriminal proxy services were exploiting old routers, especially when remote administration stayed enabled.
FAQ
KadNap is malware that infects routers and edge devices, connects them into a peer-to-peer botnet, and helps route traffic for a criminal proxy service.
No. ASUS devices appear to be the main target, but Black Lotus Labs says the operators also use the malware against other edge networking devices.
Compromised routers make useful proxies. Attackers can send traffic through them to hide their real location, evade blocklists, and support abuse such as credential attacks, fraud, or other malicious operations.
Check whether you run the latest firmware and whether remote access from WAN is enabled. If you do not need remote management, turn it off.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages