IBM links likely AI-generated Slopoly malware to Interlock ransomware attack

IBM X-Force says a new malware strain called Slopoly was used during an Interlock ransomware intrusion, where it helped attackers keep access to a compromised server for more than a week and support data theft. The company describes Slopoly as a likely AI-generated PowerShell backdoor, but stops short of claiming proof about which model created it.
That distinction matters. The strongest confirmed claim here is not that AI wrote the malware with certainty, but that the script shows strong signs of large language model-assisted development. IBM points to traits such as extensive comments, structured logging, error handling, clearly named variables, and unused code that resembles iterative AI-assisted output.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
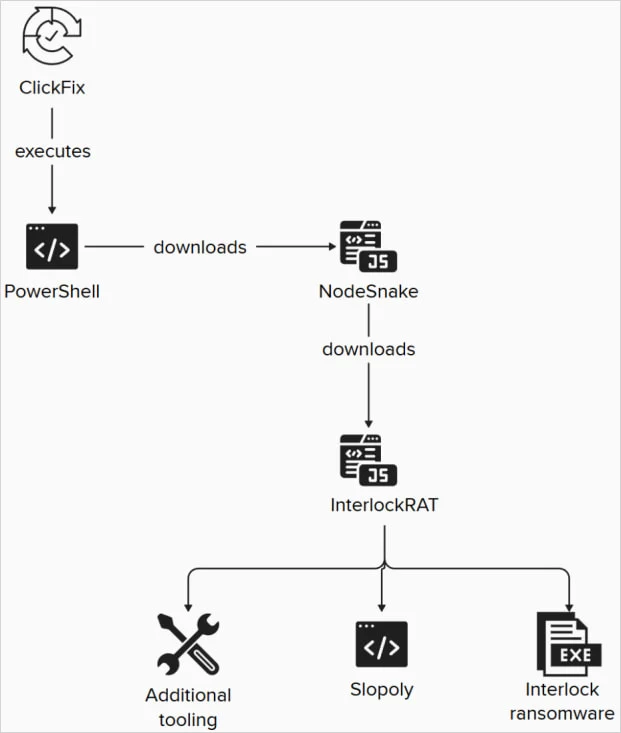
IBM attributes the intrusion to a financially motivated cluster it tracks as Hive0163, which it says has deployed Interlock ransomware in major attacks. According to IBM, the group used Slopoly late in the attack chain after an initial ClickFix social engineering lure, alongside other malware including NodeSnake, InterlockRAT, JunkFiction, and the Interlock ransomware payload itself.
What IBM says Slopoly did
| Function | Reported behavior |
|---|---|
| Persistence | Creates a scheduled task named Runtime Broker |
| C2 communications | Sends heartbeat beacons every 30 seconds |
| Command polling | Checks for commands every 50 seconds |
| Command execution | Runs received commands through cmd.exe |
| Data return | Sends command output back to the C2 |
| Logging | Maintains a rotating persistence.log file |
| Deployment path | C:\ProgramData\Microsoft\Windows\Runtime\ |
These technical details come from IBM’s analysis of the PowerShell script used in the incident. IBM says the malware was likely generated by a builder that inserted static configuration values such as session IDs, mutex names, command-and-control addresses, and beacon intervals.
Why the “AI-generated” label needs care
IBM’s report does not claim that Slopoly is advanced because of AI. In fact, the company says the script is “mediocre at best” from a technical standpoint and lacks the self-modifying behavior suggested by its own “polymorphic” label. IBM also says it could not determine which model was used, though it believes the quality suggests a less advanced one.
So the real story is not that AI suddenly created elite malware. It is that AI may have helped attackers build custom malware faster and with less effort. IBM frames this as an early sign that threat actors can now produce workable tools more quickly, even if those tools are not especially sophisticated.
Attack chain at a glance
- Initial access came through a ClickFix social engineering tactic.
- Attackers later deployed Slopoly to maintain access for more than a week.
- IBM says the same intrusion also involved NodeSnake, InterlockRAT, and the JunkFiction loader.
- The final ransomware stage used a 64-bit Windows Interlock payload.
IBM says the ransomware sample it observed could run as a scheduled task with SYSTEM privileges and used the Windows Restart Manager API to unlock files before encrypting them. The encrypted files reportedly received either the . !NT3RLOCK or .int3R1Ock extensions.
Source: IBM X-Force
Why this incident matters
This case matters because it shows a practical use of AI in cybercrime, not a theoretical one. IBM’s assessment suggests attackers may already be using generative AI to speed up malware development, create custom backdoors, and adjust tooling during live intrusions. That does not make the malware better than established families overnight, but it can shorten development time and lower the skill barrier for attackers.
It also fits a broader pattern around Interlock. IBM and IBM X-Force Exchange describe Interlock as a big-game ransomware operation tied to multi-stage intrusions, multiple backdoors, and extortion-focused campaigns. Slopoly appears to be one more tool in that ecosystem rather than a standalone breakthrough.
FAQ
No public report proves that with certainty. IBM says the script shows strong indicators of large language model-assisted development, but it could not identify the exact model.
IBM says it acted as a PowerShell backdoor that maintained persistence, contacted a command-and-control server, executed commands, and returned the results.
IBM says the intrusion started with a ClickFix social engineering lure, then expanded through additional malware and ransomware components.
IBM says no. The company describes it as technically unsophisticated and says it mainly shows how AI can speed up malware creation rather than produce advanced capabilities by itself.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages