How CISOs can scale phishing detection in the SOC without burning out analysts
Phishing has become harder to catch early because many campaigns now use legitimate cloud services, polished sign-in pages, and encrypted traffic that looks normal at first glance. For CISOs, the challenge is no longer just blocking bad emails. It is building a SOC workflow that can validate suspicious links, attachments, and login activity fast enough to stop credential theft before it spreads.
That means scaling investigation, not just alerting. If analysts need several manual steps to confirm every suspicious URL or attachment, queues grow, response slows, and attackers gain time. Security agencies and major identity vendors now push the same broader lesson: reduce reliance on weak signals, verify behavior faster, and harden identity controls so phishing does less damage even when a lure lands.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
A stronger phishing defense usually rests on three practical changes. First, teams need a safe way to interact with suspicious content and observe what really happens. Second, they need automation that can process large volumes without forcing headcount growth. Third, they need visibility into encrypted phishing flows, because HTTPS often hides the most important evidence. Those three ideas also sit at the center of ANY.RUN’s March 2026 pitch to security leaders, although product performance claims should be treated as vendor claims unless independently validated in your own environment.
Why phishing detection breaks at scale
Many SOCs still investigate phishing in a linear way. An alert arrives, an analyst checks domain reputation, opens a few tools, reviews headers, and tries to decide whether the case deserves escalation. That process can work for low volumes, but it does not scale well when teams face a constant flow of suspicious messages, QR codes, login prompts, and user-reported emails.
The real business risk starts when delays pile up. Stolen credentials can lead to SaaS access, mailbox compromise, VPN abuse, and account takeover inside trusted environments. Microsoft’s recent guidance on phishing-resistant authentication reflects that same concern, especially for privileged access and cloud administration.
The three steps CISOs should introduce
1. Let analysts interact with suspicious content safely
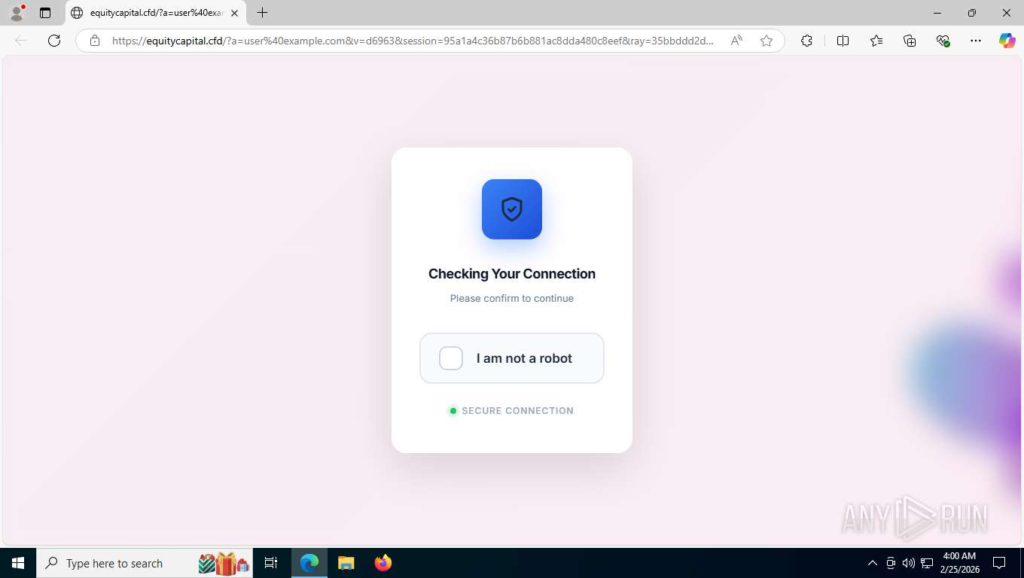
Static checks still help, but they often miss the moment when a phishing page turns malicious. Some attacks reveal the real payload only after redirects, user clicks, or test credential entry. A controlled sandbox gives analysts a safer way to follow that path and see the phishing flow as it unfolds.
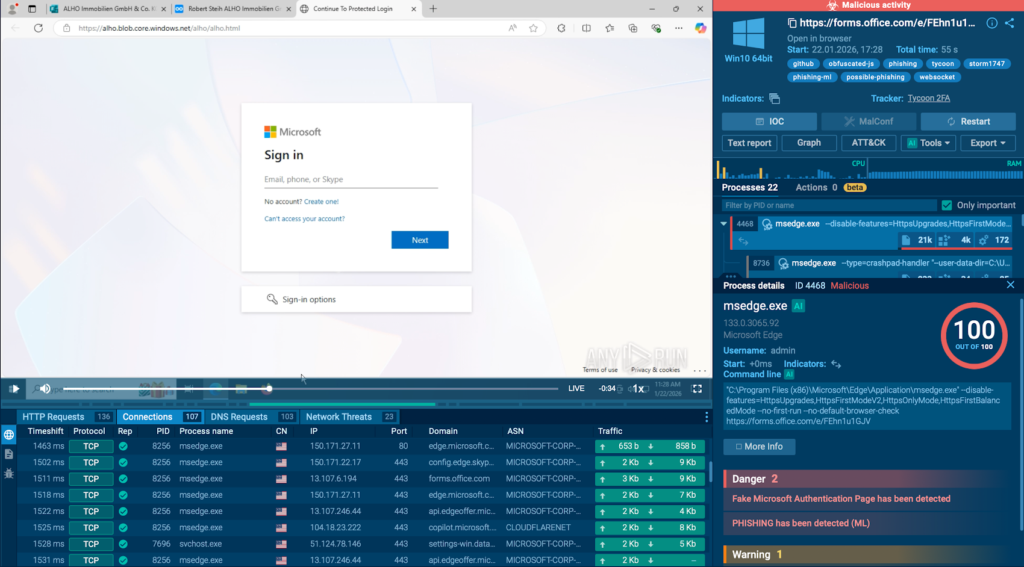
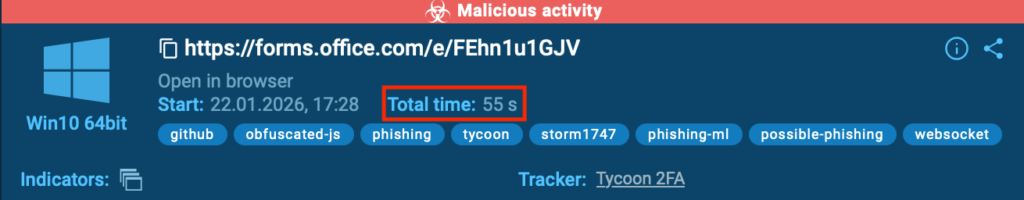
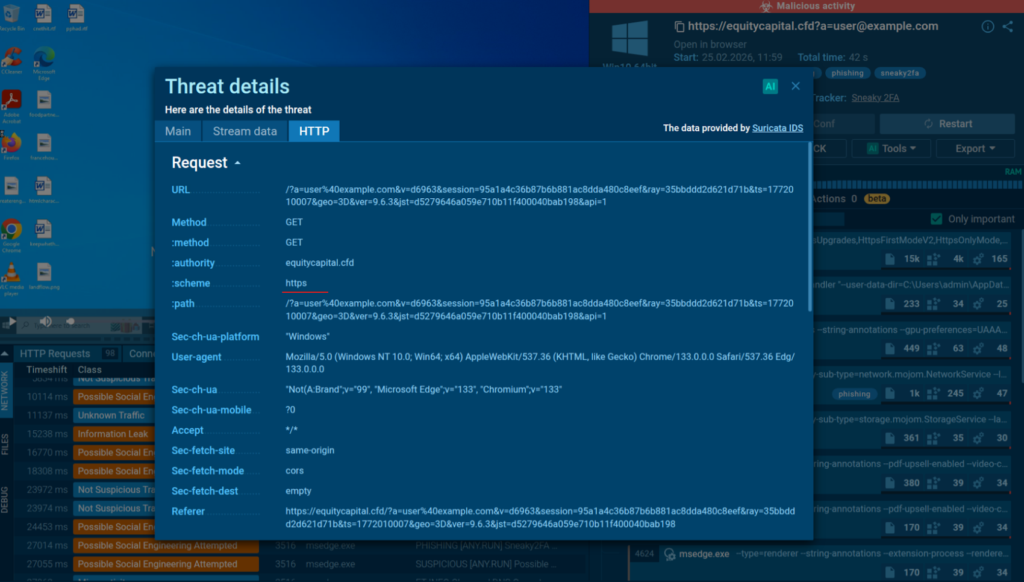
That approach improves decision quality because the SOC stops guessing from fragments. Analysts can observe redirect chains, dropped files, credential capture pages, and outbound connections in one session. ANY.RUN positions its interactive sandbox around exactly that use case, including phishing kits such as Tycoon2FA and Salty2FA.
2. Automate the first pass so volume does not overwhelm the team
Even a strong manual process collapses if every suspicious link needs human hands. Automation helps by detonating artifacts, collecting indicators, and returning an early verdict quickly. The benefit is not just speed. It also gives analysts a consistent starting point, which reduces repetitive work across Tier 1 triage.
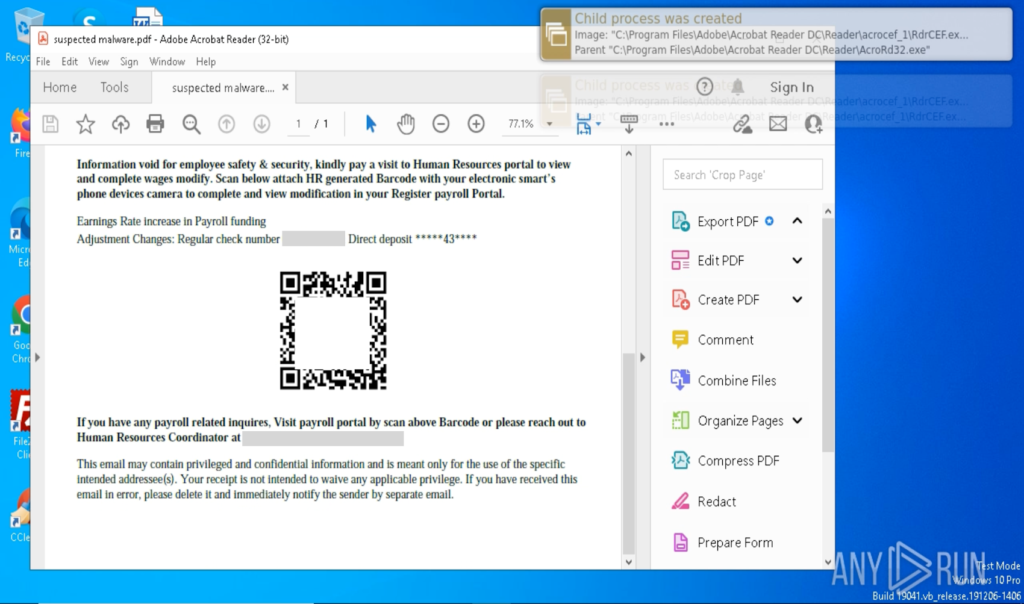
The limitation is that many phishing pages now use QR codes, CAPTCHAs, redirects, and staged login flows that break shallow automation. Vendors now respond by blending automation with simulated user interaction inside the sandbox. That can move the session deeper into the attack chain before an analyst steps in.
3. Inspect encrypted phishing traffic during analysis
A large share of phishing infrastructure now runs over HTTPS, often with valid certificates and trusted hosting providers. Without visibility into the encrypted session, monitoring tools may see only a secure connection to a seemingly normal site. That creates a false sense of trust and slows confirmation.
ANY.RUN says its sandbox can decrypt HTTPS traffic during execution by extracting keys from process memory, which helps expose redirect chains and credential harvesting logic during the first run. That is a meaningful capability if it performs as advertised, because it helps analysts confirm intent faster instead of escalating every unclear case.
Static checks vs. scalable phishing investigation
| Investigation model | What it does well | What it often misses | Best use |
|---|---|---|---|
| Static analysis | Fast metadata checks, reputation lookups, header review | Redirect chains, credential capture logic, gated phishing pages | First-pass filtering |
| Interactive sandboxing | Shows behavior in a controlled environment | May need tuning and analyst review for edge cases | High-risk URLs and attachments |
| Automated sandbox triage | Handles large alert volumes quickly | Deep evasion tricks if automation is shallow | Tier 1 throughput |
| SSL-aware analysis | Reveals behavior inside HTTPS sessions | Depends on tool capability and coverage | Confirming encrypted phishing flows |
Vendor material from ANY.RUN supports the case for interactive and encrypted-session analysis, while public guidance from Microsoft and CISA supports the broader need to reduce phishing exposure through stronger identity controls and faster validation.
What CISOs should ask their SOC leaders now
- How long does it take to validate a suspicious phishing link from alert to verdict?
- How many cases still depend on manual clicking, manual enrichment, or manual escalation?
- Can the current stack analyze phishing pages hidden behind HTTPS, redirects, or QR codes?
- Which workflows reduce phishing impact even if the lure succeeds, such as phishing-resistant MFA and stronger conditional access?
- Have product claims about faster triage or lower workload been tested internally against real cases?

Those questions matter because tooling alone does not solve phishing at scale. The operating model matters just as much. Fast validation, lower analyst drag, and stronger identity controls usually deliver more value than another feed of weak indicators.
FAQ
Most teams still rely on manual validation steps that do not keep up with alert volume. That creates delays, backlog, and missed opportunities to stop credential theft early.
Encrypted sessions can hide redirect chains, fake login forms, and credential capture behavior from traditional inspection layers. The traffic can look legitimate unless a tool can reveal what happens inside the session.
Not fully. Basic automation helps with scale, but modern phishing often adds QR codes, CAPTCHAs, and multi-step flows that require richer interaction. The best results usually come from combining automation with safe sandbox interaction.
They should also reduce the blast radius of phishing by pushing phishing-resistant MFA, stronger conditional access, and better protection for privileged roles and cloud administration.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages