IBM links Hive0163 to AI-assisted Slopoly malware used for persistent access in ransomware attacks

IBM X-Force says a financially motivated threat cluster known as Hive0163 used a likely AI-generated malware family called Slopoly during a ransomware intrusion in early 2026. According to IBM, the malware helped the attackers keep persistent access to a compromised server for more than a week during the post-exploitation stage of the attack.
The bigger story is not that Slopoly is highly advanced. It is not. IBM describes the script as “mediocre at best” from a technical standpoint. What concerns defenders is the speed and ease with which attackers appear to have built and deployed it. IBM says malware like Slopoly shows how threat actors can use AI to create new malware frameworks in a fraction of the time older development cycles required.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
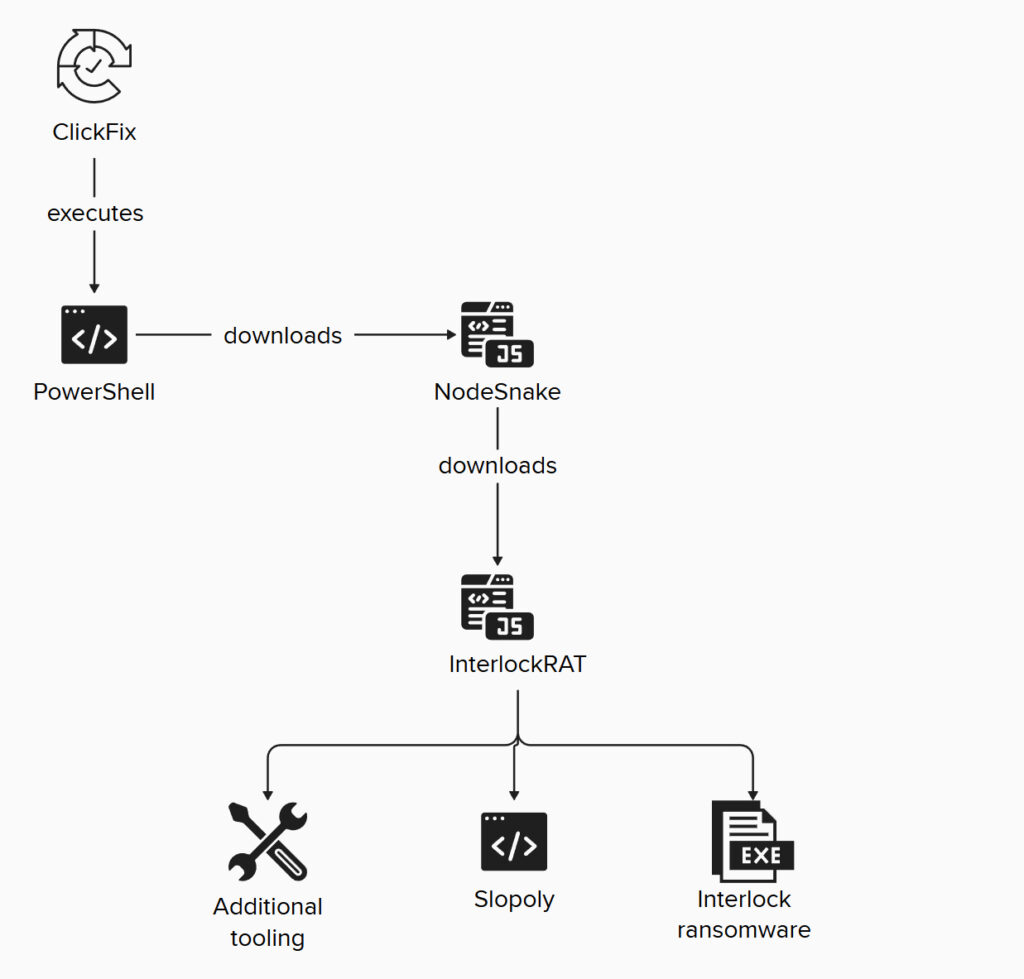
IBM attributes the activity to Hive0163, a group it ties to large-scale data theft and ransomware. The company says the cluster has used tools such as NodeSnake, Interlock RAT, JunkFiction loader, and Interlock ransomware. In the observed case, Slopoly appeared later in the attack chain, which suggests the operators used it to keep control of the environment after the initial compromise.
IBM’s analysis points to a PowerShell backdoor that was likely created with help from a large language model. The signs include extensive comments, detailed logging, strong error handling, and unusually clean variable names. The code even labels itself a “Polymorphic C2 Persistence Client,” although IBM says the malware does not actually show advanced polymorphic behavior and cannot rewrite its own code during execution.
Instead, Slopoly looks more like a practical backdoor built fast. IBM says it was likely generated through a builder that inserted fixed configuration values such as a session ID, mutex name, C2 URL, and beacon timings. The script reportedly lands in C:\ProgramData\Microsoft\Windows\Runtime\ and creates persistence through a scheduled task named “Runtime Broker.”
Once active, Slopoly collects basic system data, sends a heartbeat to its command server every 30 seconds, checks for new commands every 50 seconds, runs those commands through cmd.exe, and sends the results back to the attackers. IBM says it also keeps a local log file named persistence.log, which rolls over once it hits 1 MB.
IBM says the intrusion itself began with a ClickFix social engineering attack. In that technique, victims get tricked into pasting a malicious PowerShell command into the Windows Run box. IBM says that step installed NodeSnake, a NodeJS-based malware that then helped bring in the wider Interlock framework, including Slopoly.
That makes this case important for two reasons. First, it shows attackers do not need groundbreaking AI malware to benefit from generative tools. Second, it fits a wider IBM warning that AI is starting to speed up attacker workflows even when the underlying code remains basic. IBM’s 2026 X-Force Threat Intelligence Index says organizations should prepare for AI-accelerated attacks that increase speed, scale, and automation across common intrusion paths.
What IBM says Slopoly does
| Capability | IBM’s finding |
|---|---|
| Malware type | PowerShell backdoor and likely client component of a new C2 framework |
| Suspected developer aid | Likely generated with help from a large language model |
| Persistence | Scheduled task named “Runtime Broker” |
| Install path | C:\ProgramData\Microsoft\Windows\Runtime\ |
| Beacon interval | Every 30 seconds |
| Command polling | Every 50 seconds |
| Command execution | Via cmd.exe |
| Local logging | persistence.log with rollover at 1 MB |
Why this matters to defenders
- AI helped shorten development time even though the malware itself was not sophisticated.
- Hive0163 used Slopoly during a real ransomware intrusion, not just in testing.
- IBM says the malware maintained access to the victim server for more than a week.
- The attack started with ClickFix, which shows social engineering still opens the door for modern ransomware chains.
- IBM’s broader 2026 threat outlook warns that AI is speeding up attacker operations even when foundational security gaps still drive most successful breaches.
Key takeaway
Slopoly does not represent a leap in malware sophistication. It represents a drop in the effort required to build and field custom tooling during an attack.
That shift could matter a lot. If lower-skill operators can spin up workable backdoors faster, defenders may face more custom malware, more rapid iteration, and harder attribution even when the code itself looks ordinary. IBM says this is only the early phase of a broader arms race between attackers and defenders using AI.
FAQ
IBM X-Force describes Slopoly as a likely AI-generated PowerShell backdoor that acts as the client side of a command-and-control framework.
IBM links the malware to Hive0163, a financially motivated threat cluster associated with extortion, data theft, and ransomware activity.
Not really. IBM says the script is functional but technically mediocre, and it does not deliver the advanced polymorphic behavior its own comments claim.
IBM says the observed intrusion started with ClickFix social engineering, which tricked the victim into running a malicious PowerShell command.
IBM says the main risk is acceleration. AI can help threat actors build and deploy malware frameworks faster, even if the resulting code is not sophisticated.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages