Microsoft warns Storm-2561 uses fake VPN downloads in search results to steal enterprise credentials

Storm-2561 is using poisoned search results and fake VPN downloads to steal enterprise credentials, according to Microsoft. The campaign pushes users searching for trusted VPN software toward spoofed sites and malicious ZIP files that install signed trojans disguised as legitimate VPN clients. Microsoft says the goal is simple: capture saved VPN credentials and connection data from users who believe they are downloading real software.
Microsoft says it first observed the activity in mid-January 2026 and attributes it to Storm-2561, a financially motivated threat actor active since May 2025. The group has a history of abusing SEO poisoning and impersonating well-known software vendors, which makes this latest campaign part of a broader and increasingly polished playbook.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
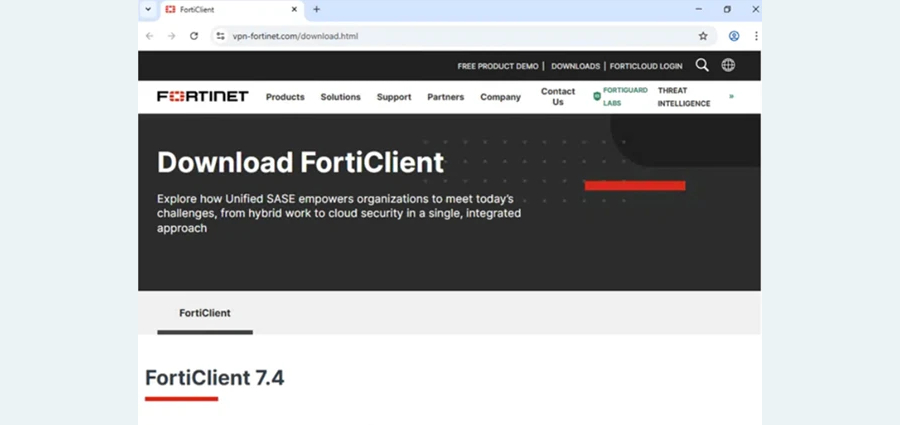
The attack starts when a victim searches for terms such as “Pulse VPN download” or “Pulse Secure client.” Instead of reaching a legitimate vendor page, the user lands on a fake website that mimics trusted enterprise VPN brands. Microsoft says it saw spoofing tied to brands such as Fortinet and Ivanti, with domains including vpn-fortinet[.]com and ivanti-vpn[.]org directing users to malicious downloads.
From there, the victim gets pushed to a GitHub repository hosting a ZIP archive. Inside that archive is an MSI installer that looks like legitimate VPN software but drops malicious DLL files during installation. Microsoft says the attacker used digitally signed components in the campaign, signed by “Taiyuan Lihua Near Information Technology Co., Ltd.,” though the certificate has since been revoked and the GitHub repositories have been taken down.
The malware then displays a convincing fake VPN sign-in prompt to capture credentials. Once the victim enters the information, the fake client shows an error and may redirect the user to the real VPN vendor site, which helps reduce suspicion. Microsoft says one of the malicious components is a variant of the Hyrax information stealer, which extracts VPN credentials and connection data for exfiltration.
Persistence is also built into the campaign. Microsoft says the malware uses the Windows RunOnce registry key so it can run again after a reboot. That gives the attackers another shot at credential theft even if the initial lure did not fully succeed the first time.
The campaign matters because it targets users at a moment of high trust. People searching for enterprise VPN software often expect to find a vendor download page near the top of search results. Attackers know that and abuse both search ranking trust and software branding to make the malicious workflow feel legitimate. Microsoft says the operation highlights how trusted platforms such as GitHub can also be abused as part of the delivery chain.
This tactic did not appear out of nowhere. Zscaler documented a similar campaign in October 2025 involving trojanized Ivanti Pulse Secure VPN installers delivered through Bing-focused SEO poisoning. In that campaign, signed MSI files dropped malicious DLLs that stole VPN connection details and sent them to attacker-controlled infrastructure. That earlier activity closely matches what Microsoft now attributes to Storm-2561.
How the Storm-2561 campaign works
| Stage | What happens |
|---|---|
| Search | Victim searches for trusted VPN software |
| Redirect | SEO-poisoned results send the user to a spoofed site |
| Download | Fake page links to a malicious GitHub-hosted ZIP file |
| Install | MSI installer drops malicious DLLs alongside fake VPN software |
| Theft | Fake sign-in window captures VPN credentials |
| Persistence | Malware sets RunOnce for execution after reboot |
Microsoft says this chain relies on user trust in both search rankings and brand familiarity.
Why this attack is dangerous
- It abuses trusted search behavior instead of suspicious spam or exploit kits.
- It uses signed malware to appear more legitimate and evade suspicion.
- It targets enterprise VPN credentials, which can open a path to deeper network access.
- It can redirect users to the legitimate vendor site after theft, which helps hide the compromise.
- It shows that attackers still get strong results from SEO poisoning when they pair it with polished branding and trusted hosting.
What organizations should do
- Enforce MFA on all VPN and enterprise accounts.
- Train users to download software only from verified vendor domains they type directly into the browser.
- Block or closely inspect unsigned and unexpected MSI installers from download workflows. This is a best-practice inference based on the attack chain Microsoft described.
- Monitor for suspicious use of RunOnce, DLL sideloading behavior, and fake VPN application paths. This is also a defensive inference from Microsoft’s technical details.
- Review detections for Hyrax or similar credential-stealing behavior on endpoints used for remote access.
FAQ
Storm-2561 is a Microsoft-tracked threat actor that has used SEO poisoning and software vendor impersonation since at least May 2025.
It tricks users into installing a fake VPN client, then displays a bogus VPN sign-in window that captures the credentials they enter.
Microsoft says the credential theft component is a variant of the Hyrax information stealer.
Yes. Microsoft says the GitHub repositories used in the campaign were taken down and the abused certificate was revoked.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages