B says that in Egypt, for example, attackers were observed using numbers formatted to resemble local mobile prefixes.

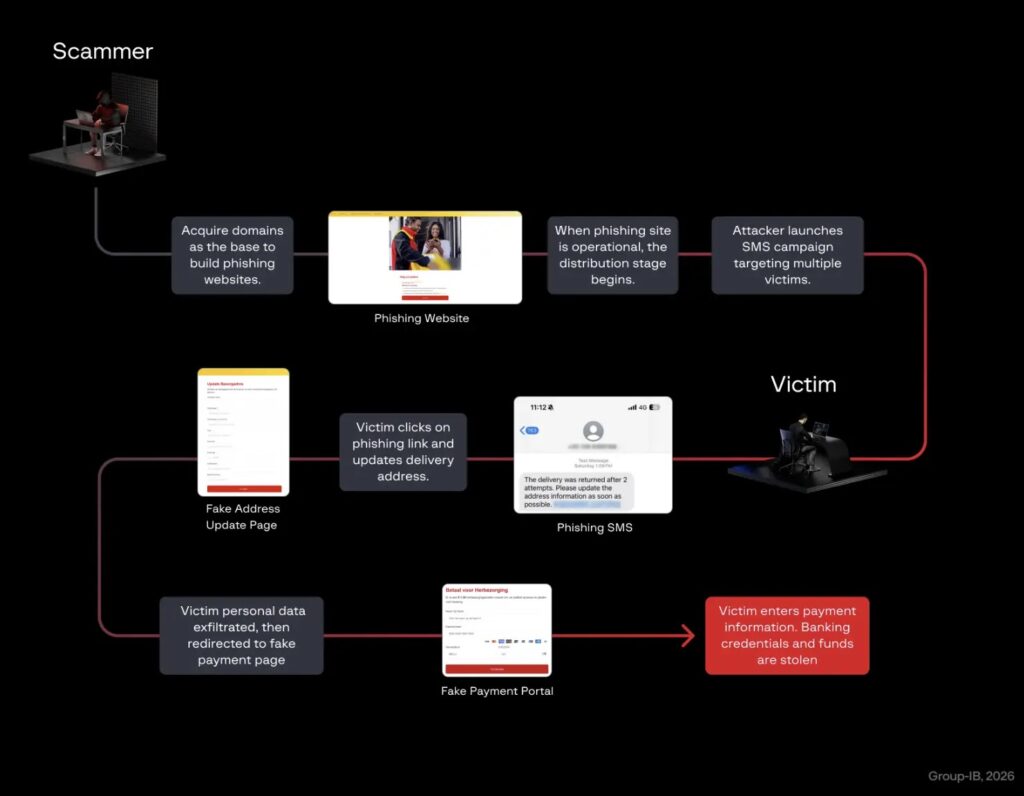
Once the victim taps the link, the phishing page often checks the user agent and shows its full content only on mobile browsers. Attackers also add endings such as index.html or similar masks to make links look more convincing and help the page load correctly on phones.
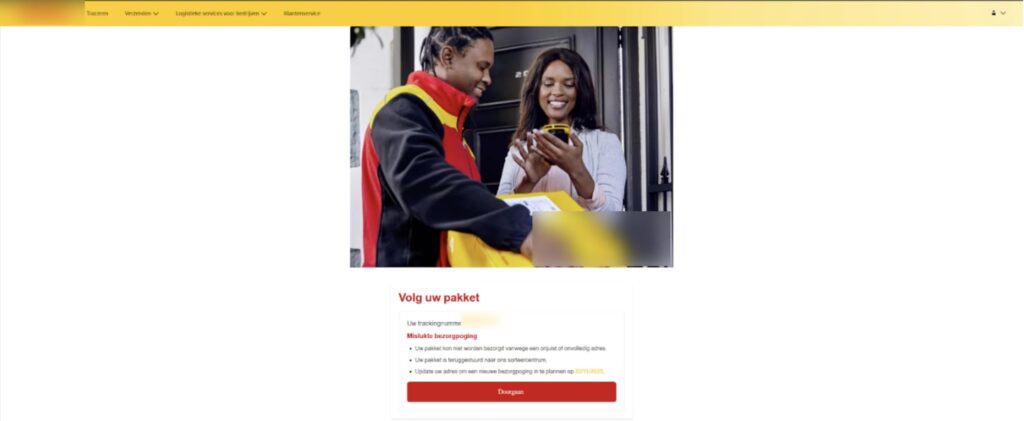
The pages usually present fake tracking details, a claimed reason for failed delivery, and a request to update address data or pay a small fee. The pressure is psychological, not technical. The goal is to make the victim act before thinking.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What makes the phishing technically dangerous
Group-IB says its HTML analysis found embedded scripts that open WebSocket connections and support live credential harvesting. In practice, that means attackers can receive entered data immediately, rather than waiting for the victim to submit a form and leave the page.
The researchers also found session tracking through unique UUID tokens, which suggests organized operations that manage victims individually and at scale. That infrastructure, combined with shared IPs, registrars, and hosting overlaps, points to coordinated phishing activity rather than isolated copycat pages.
Group-IB also says the campaign shows signs linked to Darcula, a Chinese-language phishing-as-a-service platform known for large volumes of counterfeit domains and ready-made phishing templates. The company says customers can review more detail about the activity and the Darcula Pushing Kit in its threat intelligence portal.
What Group-IB found in MEA
| Finding | Detail |
|---|---|
| Main lure | SMS delivery failure message |
| Common asks | Address update, handling fee, taxes, tariffs |
| Main targets | Postal and delivery brands, then banks, telecom, mobility, e-commerce |
| User focus | Mobile users |
| Data at risk | Personal details, banking credentials, card numbers, CVV, OTPs |
| Delivery method | Phishing links sent through SMS |
Why the scam keeps working
Shipment alerts blend into daily life. If people shop online often, they already expect delivery texts, tracking updates, and occasional address checks. Criminals exploit that normal behavior and make the fake message feel just plausible enough to trigger a fast tap.
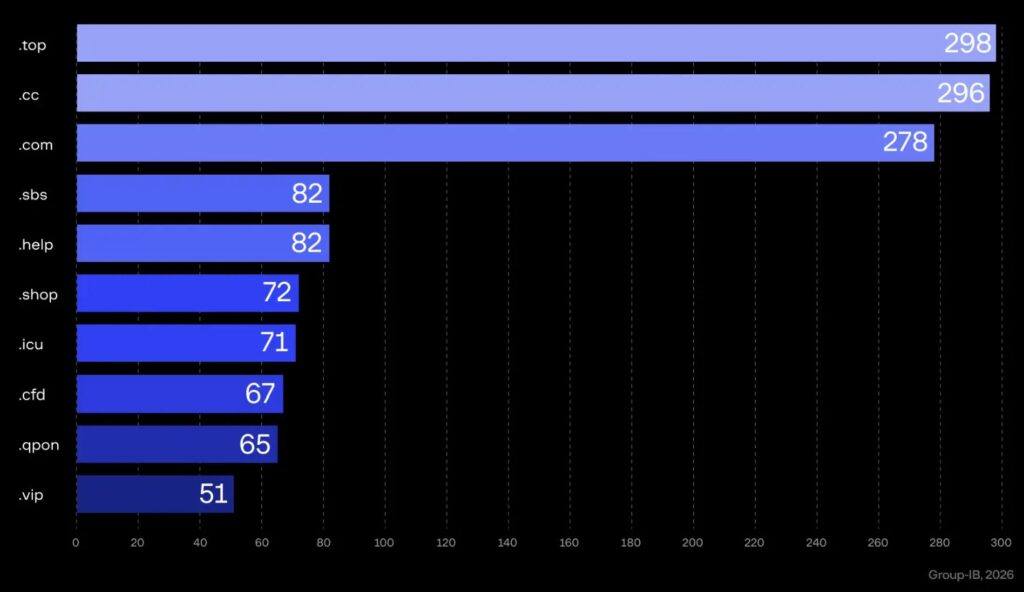
The fake domains also help. Group-IB warns that many of these campaigns use disposable or low-cost extensions such as .xyz, .sbs, .top, and .click, which lets attackers replace blocked domains quickly and keep the scam moving.
How to protect yourself
- Do not tap shipment links from unexpected SMS messages. Go to the courier’s official website and enter the tracking number manually.
- Treat any message demanding urgent payment or address correction as suspicious. Legitimate courier companies usually do not charge for simple redelivery or basic address updates.
- Watch for unfamiliar domain endings such as
.xyz,.sbs,.top, and.click. - Use mobile security tools and browser protections that can flag phishing pages and suspicious links.
- Report scam messages to your postal operator or local cyber authority.
What businesses should do
- Publish clear alerts when scammers impersonate your brand.
- Strengthen domain protections and email authentication with DMARC, DKIM, and SPF. Group-IB’s post appears to contain a typo and says “SKIM,” but the standard email protocol is DKIM.
- Work with mobile operators to filter scam SMS patterns and block impersonation attempts.
- Offer a public verification tool so users can confirm whether a message or tracking request is legitimate.
FAQ
It is a phishing scheme where victims receive a fake delivery failure text and are pushed to a bogus courier page that steals personal and financial data.
Group-IB says the activity has grown sharply since early 2024 and surged through 2025, especially as delivery and courier services have become a routine part of daily life.
They target personal information, banking credentials, card numbers, CVV codes, and one-time passwords.
Do not use the link in the message. Open the courier’s official website yourself and check the shipment manually.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages