New CondiBot variant and ‘Monaco’ cryptominer expand threats to network devices

Two newly documented malware strains show how quickly financially motivated attackers have moved deeper into network infrastructure. Eclypsium says a new CondiBot variant and a separate cryptomining operation called Monaco were both captured on March 6, 2026, targeting Linux-based devices that include routers, IoT systems, servers, and network appliances.
The larger point is not just the malware itself. It is what the malware says about the threat landscape. Network devices used to sit mostly in the crosshairs of advanced espionage actors, but Eclypsium says the same weak spots now attract botnet operators and cryptojacking crews as well.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That trend matches broader industry data. Eclypsium cites the 2025 Verizon Data Breach Investigations Report as showing an almost eightfold increase in exploitation of edge and network devices, while Google’s threat intelligence work found that nearly a quarter of zero-days exploited in 2025 targeted network and security technologies.
What Eclypsium found
Eclypsium says the first malware sample is a previously undocumented CondiBot variant, a Mirai-derived DDoS botnet designed to turn Linux systems into attack nodes. The second is Monaco, a Go-based SSH scanner and Monero cryptominer that brute-forces weak SSH credentials, compromises exposed systems, and uses them for cryptocurrency mining.
Neither sample had been previously reported on major threat intelligence platforms when Eclypsium found them. The company says that included platforms such as VirusTotal, ThreatFox, Hybrid Analysis, and ELF Digest.
Why the new CondiBot variant stands out
Eclypsium says this CondiBot sample is a generic Linux botnet agent rather than something limited to one vendor. It supports ARM, ARM5, ARM6, ARM7, MIPS, x86, and x86_64, which gives it a broad reach across vulnerable Linux-based devices.
The malware uses a layered delivery routine that cycles through wget, curl, tftp, and ftpget so it can still pull down payloads even if some tools are missing on the target system. Once active, it connects to its command server, disables reboot utilities by setting permissions to 000, manipulates the hardware watchdog, and kills competing botnets running on the same machine.
Eclypsium also found a string inside the binary labeled QTXBOT, which had not appeared in earlier Condi reporting. The researchers say this may indicate a forked variant or an internal project name used by the developers. They also noted that the sample registers 32 attack handlers, more than earlier reported Condi versions, which suggests the addition of new flood techniques or protocol variants.
What Monaco does after it gets in
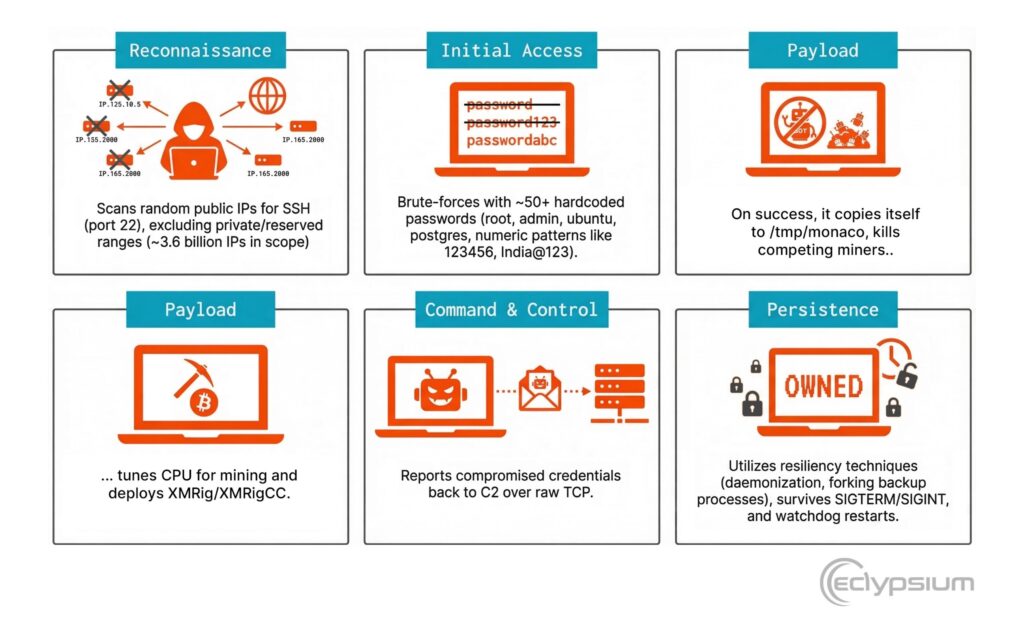
Monaco takes a different path. Eclypsium says it is written in Go 1.24.0 and acts as both an SSH scanner and a Monero cryptominer. It brute-forces exposed SSH servers across the internet, steals valid credentials, and sends them back to its command-and-control server.
The malware supports multiple architectures, including x86-64, ARM32, ARM64, and MIPS big and little endian, which lets it target servers, routers, IoT gear, and even some Juniper equipment. Eclypsium says Monaco deploys XMRig or XMRigCC to mine Monero through MoneroOcean after it compromises a host.
Eclypsium traced Monaco’s C2 infrastructure to Alibaba Cloud Singapore at 8.222.206.6. The researchers said the operator left behind open directory listings, debug builds, and default tokens, which point to relatively weak operational security.
Key details at a glance
| Threat | Main role | Target types | Notable traits |
|---|---|---|---|
| CondiBot variant | DDoS botnet | Linux network devices, routers, IoT, servers | Mirai-derived, multi-architecture, 32 attack handlers, QTXBOT string |
| Monaco | SSH scanner and cryptominer | Servers, IoT devices, routers, network equipment | Go 1.24.0, brute-force SSH, steals credentials, deploys Monero miner |
Why network devices keep attracting attackers
Attackers like these devices because they sit at critical points in the network and often run embedded systems that do not support standard endpoint security tools. If an attacker gains control of a router, firewall, or switch, that foothold can support persistence, traffic interception, lateral movement, or large-scale abuse for botnets and mining.
Eclypsium argues that many organizations still treat network gear as opaque infrastructure rather than as endpoints that need the same level of monitoring and security review as servers and laptops. That visibility gap is one reason these campaigns keep working.
What organizations should do
- Audit internet-facing network devices for unknown processes, suspicious outbound connections, and signs of cryptomining activity.
- Replace weak or default SSH credentials immediately and restrict SSH access to trusted IP ranges.
- Keep firmware and software up to date on routers, firewalls, VPN gateways, and IoT hardware.
- Isolate or retire end-of-life devices that no longer receive vendor patches.
- Treat network appliances as critical assets that require active monitoring, not as blind spots outside normal endpoint security programs. This last point follows directly from Eclypsium’s broader analysis.
FAQ
Eclypsium says it is a previously undocumented Mirai-derived DDoS botnet sample that targets a wide range of Linux devices and supports several processor architectures.
Monaco is a Go-based SSH brute-forcer and Monero cryptominer that compromises exposed systems, steals credentials, and uses infected hosts for mining.
No. Eclypsium says the CondiBot variant is a generic Linux botnet agent that can affect vulnerable Linux devices across vendors.
Because they sit in high-value parts of the environment and often lack deep security visibility, which makes them attractive to both advanced actors and financially motivated attackers.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages