DRILLAPP backdoor targets Ukraine by hiding inside Microsoft Edge’s debugging features

A newly documented espionage campaign has targeted Ukrainian organizations with a backdoor called DRILLAPP. Researchers say the malware abuses Microsoft Edge command-line and debugging features to blend into normal browser activity while collecting files, microphone audio, webcam images, and screen captures from infected systems.
The activity was observed during February 2026 and has been linked with low confidence to the Russia-aligned group tracked as Laundry Bear, also known as Void Blizzard and UAC-0190. LAB52, the threat intelligence team at S2 Grupo, said the campaign shares tradecraft with an earlier operation that used charity-themed lures and public text-sharing services to target Ukrainian defense-related entities. Microsoft has previously described Void Blizzard as a Russia-affiliated espionage actor that focuses heavily on NATO states and Ukraine.
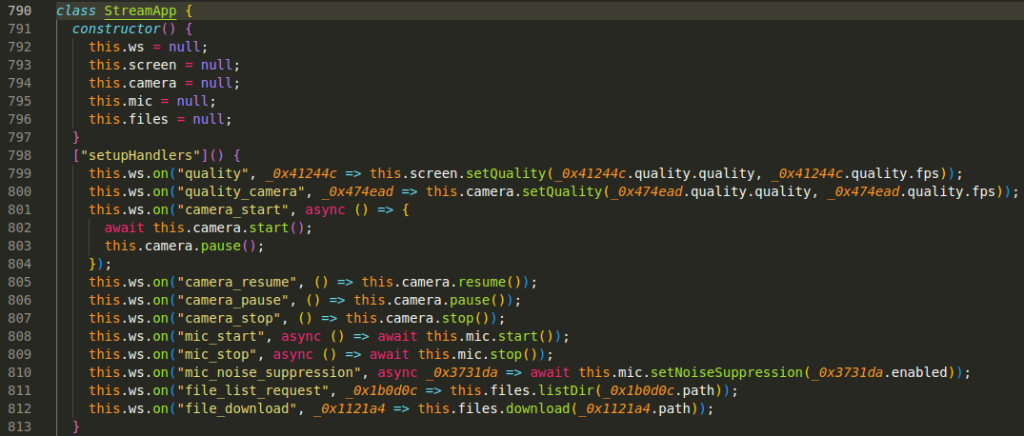
What makes this campaign stand out is the delivery method. Instead of dropping a traditional Windows backdoor and leaving it running as an obvious suspicious process, the attackers run their JavaScript payload through Edge in headless mode. LAB52 said the malware uses browser flags that weaken security boundaries and can grant access to sensitive local resources, helping the spyware act through a process many security tools and users would normally trust. Microsoft’s own documentation confirms that Edge supports the DevTools Protocol and can be launched with a remote debugging port that exposes a WebSocket debugger endpoint.
Researchers identified two campaign variants. The earlier one used LNK shortcut files that created an HTA file in the temporary folder and pulled remote code from Pastefy. To stay persistent, the malicious shortcut was copied into the Windows Startup folder. A later variant shifted away from LNK files and used Windows Control Panel modules, while keeping the broader infection logic in place and expanding the backdoor’s file-handling features.
LAB52 said the operators also relied on Chrome DevTools Protocol style functionality to work around JavaScript’s usual limits on remote file downloads. That matters because it shows the attackers were not simply using the browser as a launcher. They were using browser debugging infrastructure as part of the backdoor’s operational design. According to Microsoft, the protocol exists to inspect, debug, and profile Edge, and a browser started with a remote debugging port exposes attachable targets and a webSocketDebuggerUrl. In the wrong hands, those legitimate capabilities can become surveillance tools.
The lures also fit a familiar pattern. The campaign used judicial and charity themes, including material referencing Starlink installation and the Come Back Alive Foundation. Recorded Future News said the operation targeted Ukrainian organizations with fake documents tied to Starlink terminal verification and a well-known charity, reinforcing the view that the attackers tailored the social engineering to current wartime concerns in Ukraine.
For defenders, the larger lesson is clear. This campaign shows how legitimate browser features can be turned into a stealth layer for espionage. Microsoft has already warned that Void Blizzard uses simple techniques that still work at scale, while LAB52 believes DRILLAPP may still be in an early development stage. Even so, the tradecraft is already effective enough to deserve close attention because it hides spying behavior inside one of the most common processes on a Windows system.
DRILLAPP campaign at a glance
| Element | What researchers found |
|---|---|
| Primary targets | Ukrainian entities and organizations |
| Suspected actor | Laundry Bear / Void Blizzard / UAC-0190, with low-confidence attribution from LAB52 |
| Initial lure themes | Judicial notices, Starlink-related content, and charity-themed material including Come Back Alive references |
| Early infection chain | LNK file creates HTA, then loads remote script from Pastefy |
| Persistence | LNK copied to Windows Startup folder |
| Execution method | Microsoft Edge headless mode with unsafe flags and debugging features |
| Capabilities | File upload and download, microphone access, webcam capture, screen capture, device fingerprinting |
| Later variant | Uses Windows Control Panel modules and adds recursive file enumeration and batch uploads |
Why this attack matters
- It turns a trusted browser into the main execution environment, which can reduce suspicion during incident response.
- It abuses legitimate debugging features instead of relying only on classic malware tooling.
- It continues a wider pattern of Russian espionage activity against sectors tied to Ukraine and its partners.
- It shows that even relatively simple intrusion methods can support high-value intelligence collection.
What organizations should watch for
Security teams should review unusual Edge launches, especially headless executions, unexpected debugging ports, suspicious browser flags, HTA creation, LNK activity in Startup paths, and outbound connections to text-sharing or WebSocket infrastructure. Microsoft’s threat guidance for Void Blizzard also stresses stronger identity controls, risk-based sign-in policies, and phishing-resistant MFA because this actor has repeatedly used straightforward but effective access techniques.
FAQ
DRILLAPP is a JavaScript-based backdoor identified by LAB52. It can upload and download files, access microphones, capture webcam images, and take screen captures from infected devices.
LAB52 linked the operation with low confidence to Laundry Bear, also known as Void Blizzard and UAC-0190, based on overlaps with earlier campaigns. Microsoft separately tracks Void Blizzard as a Russia-affiliated espionage actor.
Researchers believe Edge helped the malware hide in a common, trusted process while giving it access to debugging and browser-level features that supported file access and surveillance actions. Microsoft documents confirm that Edge supports remote debugging through the DevTools Protocol.
The current campaign focuses on Ukrainian entities, but the broader actor linked to it has targeted critical sectors in multiple countries, especially NATO states and organizations tied to Ukraine.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages