Google warns ransomware actors are shifting tactics as profits fall and data theft rises

Ransomware groups are under growing financial pressure, but Google says that is not making the threat smaller. Instead, attackers are changing how they operate, leaning harder on data theft, targeting smaller organizations more often, and finding new ways to profit even as ransom payments fall. Google Cloud’s latest ransomware analysis says 77% of the ransomware intrusions it analyzed in 2025 involved suspected data theft, up from 57% in 2024.
The financial strain is real. CoveWare said ransom payment rates fell to about 20% in Q4 2025, which it described as a new historic low. Sophos separately reported that the median ransom demand dropped by 34% year over year, from $2 million in 2024 to $1,324,439 in 2025.
That mix of lower payments and stronger recovery options is changing the economics of cyber extortion. CoveWare said more organizations are restoring operations without relying on a threat actor’s decryptor, while Sophos found that 97% of organizations that had data encrypted were able to recover it and 53% fully recovered within a week, up from 35% in 2024.
What Google found in 2025 ransomware investigations
Google Cloud said its latest findings come from ransomware incidents that Mandiant Consulting responded to across 2025. The company said one-third of incidents involved confirmed or suspected exploitation of vulnerabilities for initial access, most often in common VPNs and firewalls. It also found that 43% of ransomware intrusions targeted virtualization infrastructure, up from 29% in 2024.
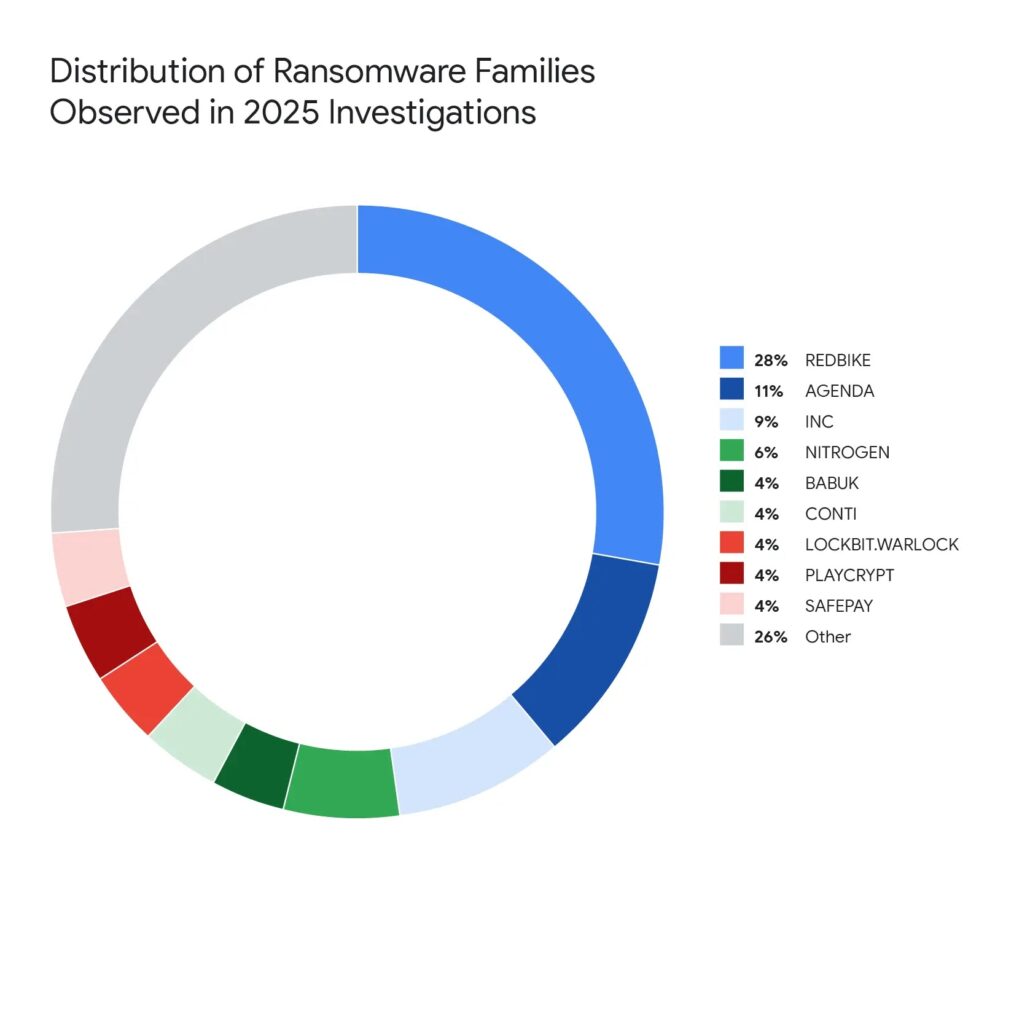
Google said REDBIKE was the most frequently deployed ransomware family in the incidents it analyzed, accounting for 30% of cases. That is a notable peak in Google’s own tracking and shows how quickly one family can gain ground after disruption hits older ransomware-as-a-service operations.
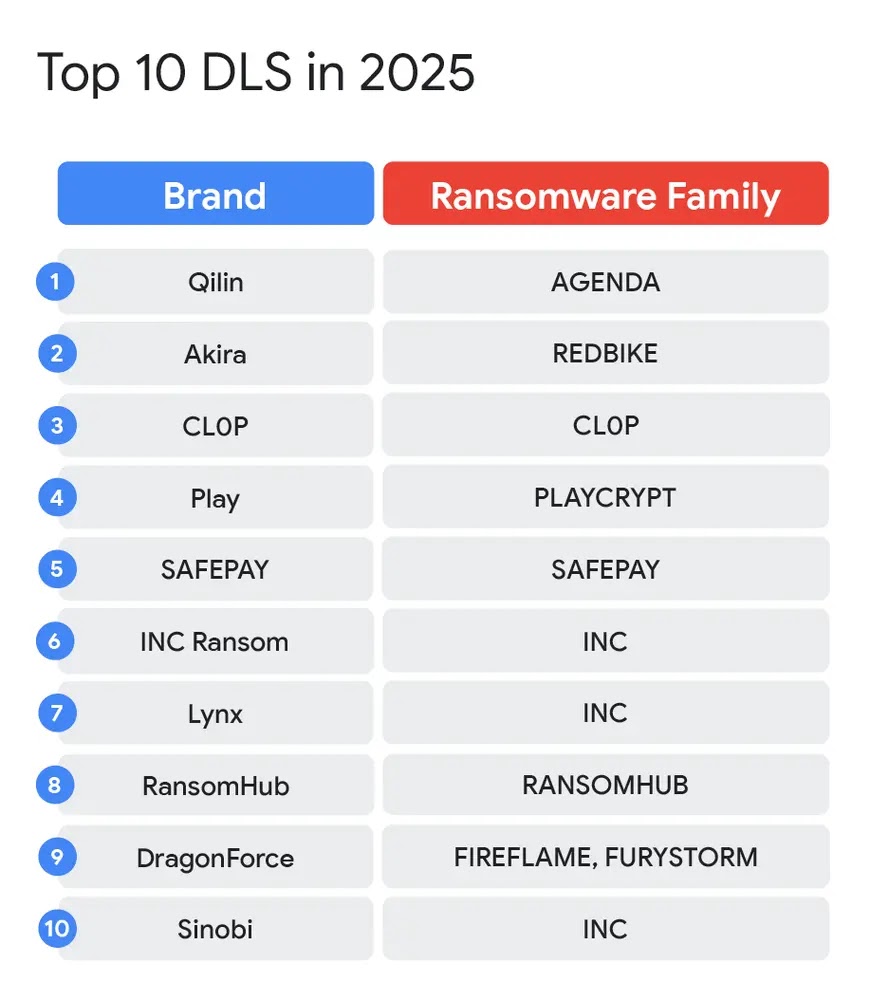
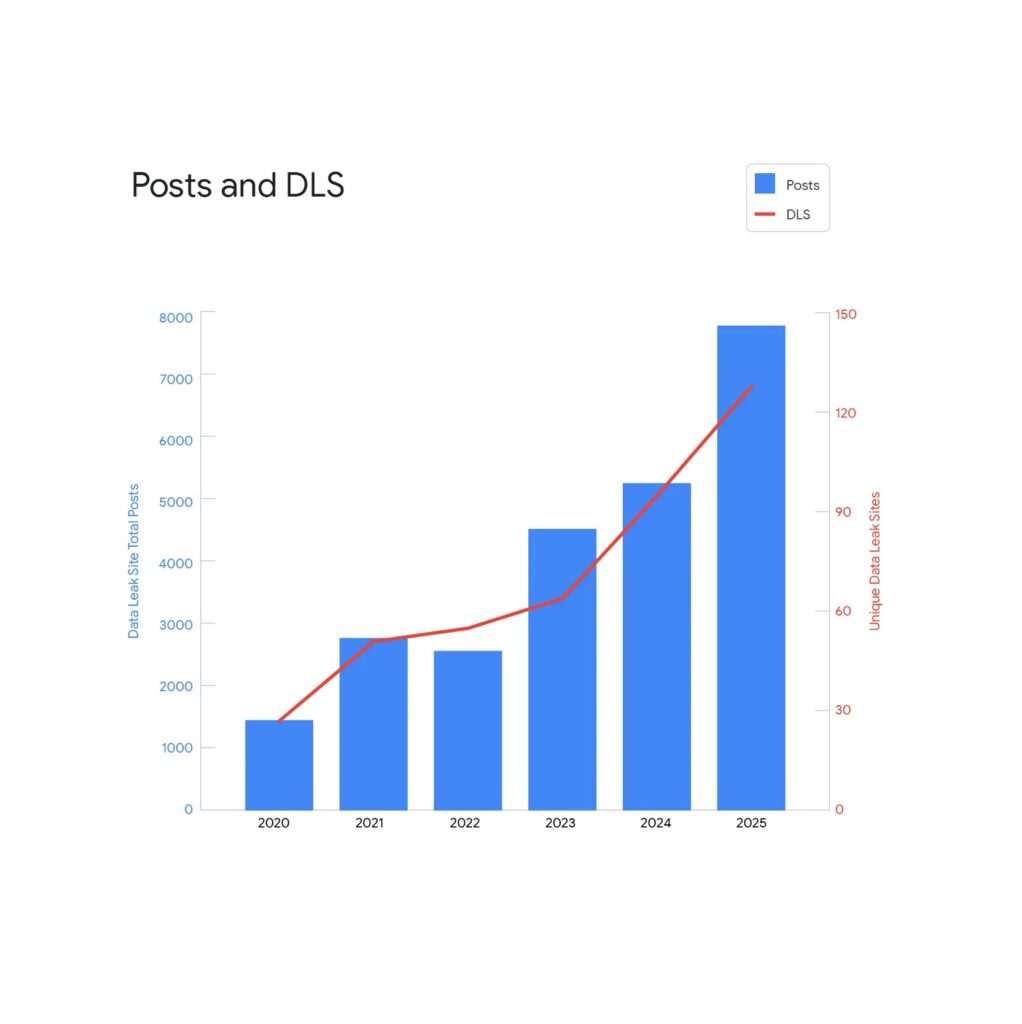
The company also said the wider ransomware ecosystem kept changing in 2025. LockBit, ALPHV, Basta, and RansomHub were weakened or disrupted by law enforcement action and internal conflict, but Google said established brands such as Qilin and Akira filled the gap, helping push the number of victims posted to data leak sites to a record high in 2025.
Why data theft is becoming more important
Google’s report shows a clear shift in extortion pressure. Encryption still matters, but stolen data now plays a much bigger role in how attackers force victims to negotiate. CyberScoop, citing Google Threat Intelligence Group, reported that financially motivated incidents involving only data theft extortion grew from about 2% of incidents in 2020 to more than 15% in 2025.
That matters because backups do not solve a data leak. A company may restore systems without paying, but it still faces public exposure of legal files, HR records, financial documents, and other sensitive business data. Google said data theft appeared in 77% of ransomware intrusions it observed in 2025, which helps explain why data leak sites kept growing even as ransom payment rates dropped.
CoveWare reached a similar conclusion from a different angle. The company said many enterprises now begin data-exfiltration-only incidents from a default assumption of non-payment and increasingly believe paying does not reduce long-term risk.
Common exfiltration and intrusion patterns
Google said ransomware actors kept using familiar tools to move stolen data out of victim environments. In the incidents it analyzed, Rclone appeared in about 28% of data theft cases. WinRAR appeared in about 23% of all 2025 incidents, and Google also observed tools and services such as FileZilla, WinSCP, MEGA, OneDrive, and Azure being used for exfiltration.
Initial access also remained practical rather than exotic. Google said exploitation of vulnerabilities accounted for roughly one-third of incidents, especially involving common VPNs and firewalls. Sophos also found exploited vulnerabilities were the most common reported root cause of ransomware incidents in 2025, at 32%, ahead of compromised credentials at 23%.
What the numbers say
| Metric | 2024 | 2025 | Source |
|---|---|---|---|
| Data theft in ransomware intrusions | 57% | 77% | Google Cloud / GTIG |
| Median ransom demand | $2,000,000 | $1,324,439 | Sophos |
| Median ransom payment | $2,000,000 | $1,000,000 | Sophos |
| Q4 ransom payment rate | not shown here | ~20% | CoveWare |
| Victims fully recovered within a week | 35% | 53% | Sophos |
| Intrusions using vulnerability exploitation | — | 33% | Google Cloud / GTIG |
Why smaller organizations may face more pressure
Google’s findings suggest some attackers are moving away from the biggest enterprises and toward organizations with fewer defensive resources. While mature large companies often have stronger backups, better incident response, and more segmented environments, smaller businesses may still offer easier paths to access, weaker visibility, and higher disruption from a single attack. That helps attackers stay profitable even when the overall extortion market contracts.
This also lines up with the broader collapse in easy ransomware profits. If fewer victims pay and recovery keeps improving, attackers need different pressure points. Data theft, access resale, phishing from compromised infrastructure, and attacks against smaller targets all fit that pattern. CyberScoop reported that Google sees more actors, especially in English-speaking cybercrime spaces, focusing directly on data theft extortion.
What organizations should do now
Security teams should treat data theft prevention as part of ransomware defense, not as a separate problem. Google’s findings make clear that stopping encryption alone is no longer enough when most intrusions also involve suspected data theft.
A practical response should include:
- Hardening internet-facing VPNs, firewalls, and remote access systems, since exploitation remained a top entry path.
- Monitoring for unusual outbound transfers and blocking unapproved tools such as Rclone where possible.
- Protecting virtualization infrastructure more aggressively, since Google saw it targeted in 43% of ransomware intrusions.
- Maintaining tested backups and recovery plans, which appear to be reducing attacker leverage.
- Logging cloud storage access and sensitive data movement, since extortion increasingly depends on stolen information rather than locked systems.
Bottom line
Google’s warning is not that ransomware is disappearing. It is that the business model is changing. Lower payment rates and better recovery are hurting profits, but attackers are adapting by stealing more data, leaning on leak-site pressure, and shifting toward tactics that keep extortion viable even when victims refuse to pay.
For defenders, that means resilience still matters, but so does visibility into exfiltration, cloud access, and the tools attackers use before encryption ever begins. The organizations that prepare only for locked files may miss the larger risk now driving many of these intrusions.
FAQ
No. Google’s findings show attackers are adapting rather than retreating, with more emphasis on data theft and extortion pressure beyond encryption.
Google said suspected data theft appeared in 77% of the ransomware intrusions it analyzed in 2025, up from 57% in 2024.
Yes. CoveWare said ransom payment rates fell to about 20% in Q4 2025, a new historic low.
Yes. Sophos said the median ransom demand dropped from $2 million in 2024 to $1,324,439 in 2025.
Google said Rclone, WinRAR, FileZilla, WinSCP, and cloud services such as MEGA, OneDrive, and Azure were used in exfiltration activity.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages