RegPwn vulnerability lets low-privilege Windows users gain SYSTEM access

A newly disclosed Windows privilege escalation flaw known as RegPwn can let a low-privileged local user gain full SYSTEM access on affected machines. The issue is tracked as CVE-2026-24291, and Microsoft fixed it in its March 2026 Patch Tuesday updates.
The bug affects the way Windows Accessibility Infrastructure, specifically ATBroker.exe, handles registry permissions during secure desktop operations. Microsoft describes it as an incorrect permission assignment issue that allows an authorized attacker to elevate privileges locally.
Security firm MDSec says it privately used the flaw in red team engagements since January 2025 before Microsoft patched it. In its technical write-up, the company explains that the vulnerability can be abused through built-in accessibility features such as On-Screen Keyboard and Narrator, which interact with registry keys that remain writable by the logged-in user.
Why RegPwn matters
This is not a remote code execution bug, so an attacker must already have local access to the target system with a regular user account. Even so, the outcome is serious because a successful exploit can turn that limited foothold into full SYSTEM-level control.
Once SYSTEM access is obtained, an attacker can tamper with services, change protected registry settings, disable defenses, and move deeper into the environment. MDSec’s proof of concept shows one practical path by overwriting a service ImagePath entry and then triggering that service to launch a SYSTEM shell.
The research also matters because it shows how trusted Windows components can be chained together in unexpected ways. In this case, accessibility tools, secure desktop behavior, writable registry paths, and registry symbolic links combined to create a reliable privilege escalation path.
How the exploit works
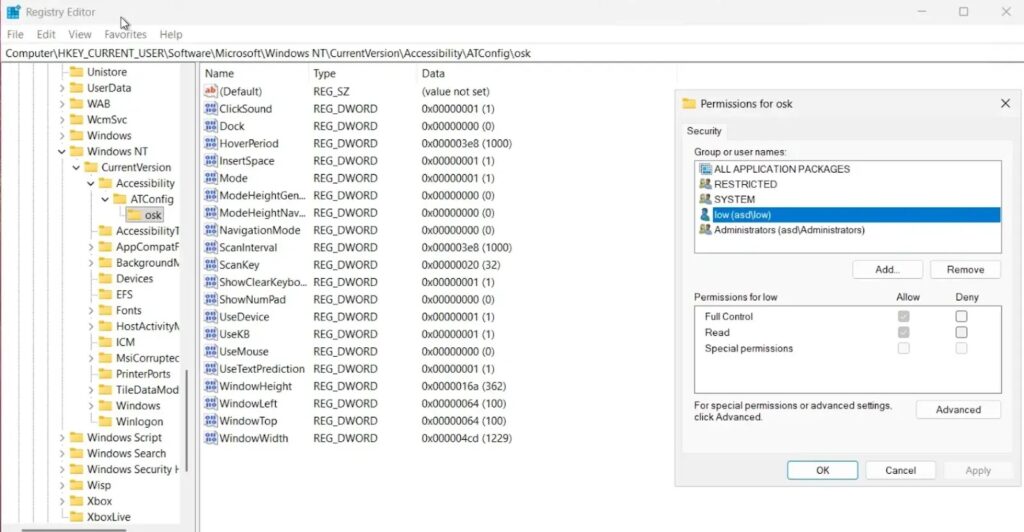
MDSec says Windows stores accessibility tool settings under a user-controlled registry path in HKCU. During login and secure desktop events, Windows copies those values into machine-level and default-user registry locations that take part in launching accessibility tools like On-Screen Keyboard.
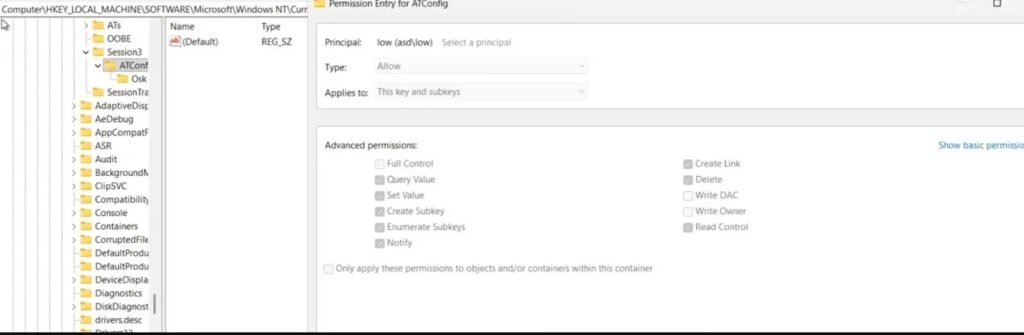
The issue appears because one of the intermediate registry locations under HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Accessibility\Session<session id>\ATConfig remains writable by the logged-in user. During a narrow timing window, the attacker can replace that key with a registry symbolic link pointing to another protected registry location.
MDSec says it used an opportunistic lock on a system XML file tied to On-Screen Keyboard to pause the process at the right moment. That pause let the attacker redirect where SYSTEM wrote registry values, turning a user-controlled accessibility configuration into an arbitrary registry write as SYSTEM.
What Microsoft says
Microsoft’s Security Update Guide entry for CVE-2026-24291 classifies the flaw as an elevation of privilege vulnerability in Windows Accessibility Infrastructure. NVD mirrors that description and lists the issue as a high-severity local privilege escalation bug with low attack complexity and low privileges required.
Microsoft’s public entry does not describe the exploit chain in the same detail as MDSec, but the vendor confirms the root category of the flaw and says the issue has been addressed through security updates released on March 10, 2026.
Affected systems
MDSec says the vulnerability affected a broad set of supported Windows releases before the patch landed.
| Platform | Reported by MDSec as affected before patch |
|---|---|
| Windows 10 | Yes |
| Windows 11 | Yes |
| Windows Server 2012 | Yes |
| Windows Server 2016 | Yes |
| Windows Server 2019 | Yes |
| Windows Server 2022 | Yes |
| Windows Server 2025 | Yes |
Source: MDSec technical write-up.
Risk summary
| Item | Details |
|---|---|
| CVE | CVE-2026-24291 |
| Vulnerability type | Elevation of privilege |
| Component | Windows Accessibility Infrastructure (ATBroker.exe) |
| Access needed | Local, authorized user |
| Potential impact | SYSTEM-level access |
| Patch status | Fixed by Microsoft in March 2026 updates |
Source: Microsoft Security Update Guide, NVD, MDSec.
What defenders should do now
Install the March 2026 Windows security updates across client and server systems. That is the main mitigation, and Microsoft has already shipped the fix.
Security teams should also review where standard users have local access on sensitive systems. This flaw still requires local execution, so limiting initial access, restricting interactive logons, and watching for unusual service or registry changes can reduce exposure even after patching. This point is an operational takeaway based on the exploit’s local nature and MDSec’s proof of concept.
Organizations that run shared servers, jump boxes, VDI environments, or developer workstations should prioritize patching because those systems often host multiple user sessions and present more opportunities for local abuse after an initial compromise. This is an inference from the documented local attack path and affected Windows versions.
Key points
- RegPwn is a Windows local privilege escalation vulnerability tracked as CVE-2026-24291.
- Microsoft patched the flaw in March 2026.
- MDSec says it exploited the issue in internal engagements since January 2025 before disclosure.
- The bug abuses writable accessibility registry paths and secure desktop behavior to achieve arbitrary registry writes as SYSTEM.
- A successful exploit can give an attacker full SYSTEM access from a low-privileged local account.
FAQ
RegPwn is the name MDSec gave to CVE-2026-24291, a Windows elevation of privilege flaw in Accessibility Infrastructure that can let a low-privileged local user gain SYSTEM access.
No. The flaw requires local access and an authorized attacker with low privileges. Microsoft and NVD both describe it as a local privilege escalation issue.
Microsoft’s public description points to Windows Accessibility Infrastructure, specifically ATBroker.exe. MDSec’s research connects the exploit to accessibility tools such as On-Screen Keyboard.
Yes. Microsoft addressed the flaw in its March 2026 Patch Tuesday updates.
Yes. Local privilege escalation flaws are still valuable because attackers often use them after phishing, malware execution, or stolen credentials to take full control of a compromised machine. This is a security assessment based on the documented impact of SYSTEM-level access.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages