Fake game cheats on GitHub and Reddit are spreading Vidar Stealer 2.0

Vidar Stealer 2.0 is spreading through hundreds of fake game cheat repositories on GitHub and promotional posts on Reddit, according to new research from Acronis Threat Research Unit. The campaign targets gamers looking for free cheats for titles like Counter-Strike 2, Fortnite, Valorant, and Call of Duty, then tricks them into installing an infostealer that can grab passwords, session data, crypto wallets, and local files.
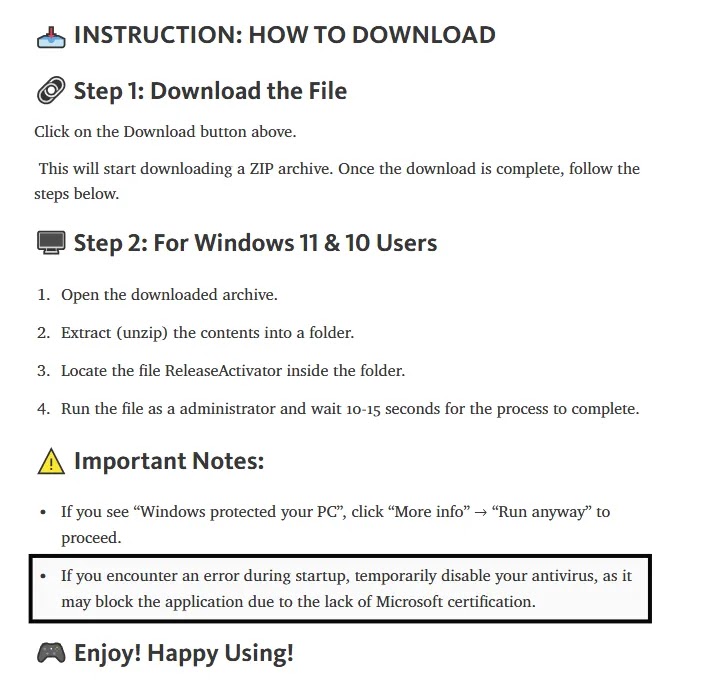
The lure works because cheat users already expect antivirus warnings, privilege prompts, and unusual setup steps. Acronis says the attackers take advantage of that mindset by presenting the malware as a normal cheat installer and telling victims to disable protections, unpack password-protected archives, and run the file with administrator rights.
This campaign also shows how threat actors keep shifting to trusted platforms. Instead of using obviously shady download portals, the operators rely on GitHub pages that look like real projects and Reddit posts that steer users toward them. That makes the infection path look more believable, especially to younger gamers or users who already trust community cheat-sharing channels.
Why Vidar 2.0 is gaining attention
Acronis says Vidar has become more prominent as the infostealer market adjusted after major law enforcement disruptions hit Lumma and Rhadamanthys. Europol announced in November 2025 that Operation Endgame targeted Rhadamanthys infrastructure, while separate law enforcement action in May 2025 disrupted Lumma Stealer operations. Acronis argues that this created room for Vidar 2.0 to fill part of that gap.
Vidar itself is not new. Acronis says it has existed since 2018 as a fork of Arkei, but the current 2.0 variant adds enough capability and flexibility to make it attractive again. The report says the malware can steal browser credentials, cookies, autofill data, Azure tokens, cryptocurrency wallets, FTP and SSH credentials, Discord and Telegram session data, and selected local files.
For attackers, gaming victims offer more than simple passwords. Compromised gaming accounts can include valuable in-game skins, stored payment methods, linked email accounts, and crypto wallets. Those assets can move quickly through grey markets, which helps explain why game-themed lures remain popular. This assessment follows directly from Acronis’s description of the stolen data and the target profile.
How the infection chain works
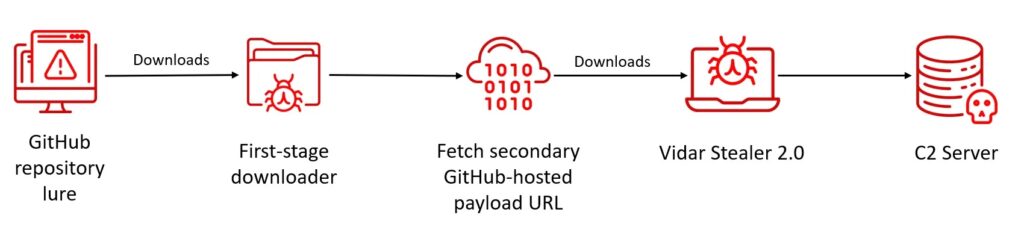
Acronis says the attack starts when a victim clicks a Reddit link or lands on a fake GitHub repository that includes installation instructions for a supposed cheat tool. The downloaded file is a PowerShell script compiled into a .NET binary with PS2EXE, which helps it look more like a normal Windows executable.
Once launched, the loader adds a Microsoft Defender exclusion for an attacker-controlled folder. It then reaches out to a hard-coded Pastebin URL to fetch the address of the next-stage payload hosted on GitHub. After that, it creates a hidden folder with a random name inside %AppData%, drops the final payload as background.exe, checks that the file starts with the MZ header of a Windows executable, and runs it.
Persistence follows immediately. Acronis says the loader creates a scheduled task named SystemBackgroundUpdate and sets it to launch at user logon with elevated privileges. The final stealer is packed with Themida and does not rely on a fixed command-and-control address in the binary. Instead, it uses Telegram bots and Steam profiles as dead-drop resolvers to hide its real infrastructure behind well-known services.
Infection chain at a glance
| Stage | What happens |
|---|---|
| Initial lure | Victim finds a fake cheat on GitHub or through Reddit |
| Setup guidance | Repository tells the victim to disable AV and run as admin |
| Loader type | PowerShell script compiled into a .NET binary with PS2EXE |
| Defense evasion | Loader adds a Defender exclusion for an attacker-controlled folder |
| Payload lookup | Loader checks a Pastebin URL for the next GitHub payload location |
| File drop | Payload is stored in a hidden random folder under %AppData% as background.exe |
| Persistence | Scheduled task SystemBackgroundUpdate runs at login with elevated rights |
| C2 hiding | Vidar 2.0 uses Telegram bots and Steam profiles as dead-drop resolvers |
Source: Acronis TRU analysis.
Why GitHub and Reddit matter here
GitHub gives malicious campaigns a layer of credibility because a repository page can look like a normal open-source project or hobby tool. Reddit helps drive traffic because posts inside gaming communities can make a cheat repository look community-approved rather than malicious. Acronis says the campaign combines both platforms into a repeatable distribution pipeline.
This does not mean GitHub or Reddit were breached. Based on the Acronis report, the attackers abused public platform trust, not a platform vulnerability. That distinction matters because users often assume malware on a known site must have come from a hack, when in many cases it comes from malicious content uploaded by bad actors.
What Vidar 2.0 steals
- Browser usernames and passwords
- Cookies and autofill data
- Azure tokens
- Cryptocurrency wallet data
- FTP and SSH credentials
- Discord and Telegram session data
- Local files chosen by the operator or the malware ruleset
What makes this campaign effective
The campaign is built around user behavior, not a software exploit. Victims install the malware themselves because they think they are getting a working cheat. The instructions even tell them to turn off protections, which removes one of the biggest barriers that would normally block the infection.
Acronis also notes that cheat users often have a strong reason not to report infections. They may not want to admit they tried to use a cheat, and they may dismiss early security alerts as false positives because cheat tools frequently trigger detections anyway. That social dynamic gives attackers extra cover.
What defenders and users should do
- Block or flag executables launched from unusual user-writable paths such as
%AppData%and%ProgramData%whenever possible. Acronis specifically recommends restricting execution from non-standard locations. - Monitor for suspicious process chains that include PowerShell, compiled script loaders, scheduled task creation, and fast data access or exfiltration activity. Acronis says EDR tools should focus on unusual process chains, credential access, and exfiltration behavior.
- Warn users that “disable antivirus first” is a major red flag, even in gaming circles where people may see it as normal. This guidance follows directly from the campaign’s installation instructions.
- Download software only from verified vendor sources or trusted official stores, not from Reddit threads or random code repositories. Acronis recommends sticking to official vendor websites or verified repositories.
- Keep operating systems and apps updated so attackers cannot stack credential theft with older unpatched weaknesses. Acronis includes patching and endpoint protection among its mitigation steps.
FAQ
It is a newer variant of the Vidar infostealer that Acronis says steals credentials, cookies, tokens, wallet data, messaging sessions, and files from infected systems.
Acronis says the main delivery path uses fake game cheat repositories on GitHub and promotional posts on Reddit that direct users to download and run malicious installers.
The campaign targets users searching for free cheats for major online games, including CS2, Fortnite, Valorant, and Call of Duty.
Acronis says the final payload avoids a simple hard-coded C2 address and instead relies on Telegram bots and Steam profiles as dead-drop resolvers, which makes tracking harder.
The available reporting does not say that. The campaign appears to abuse public trust in those platforms by hosting or promoting malicious content there.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages