Critical ScreenConnect flaw can let attackers misuse server authentication material
ConnectWise has disclosed a critical ScreenConnect vulnerability that could let attackers gain unauthorized access if they obtain server-level cryptographic material used for authentication. The flaw, tracked as CVE-2026-3564, affects ScreenConnect versions earlier than 26.1 and carries a CVSS 3.1 score of 9.0.
The issue centers on how older ScreenConnect releases handled machine key material tied to each instance. ConnectWise says earlier versions stored unique machine keys in server configuration files, which under certain conditions could allow unauthorized actors to extract and misuse that material for session authentication.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That makes this a serious problem for on-premises deployments. If the cryptographic material becomes accessible, a threat actor may be able to generate or modify protected values that the application treats as trusted, which can lead to unauthorized actions inside the ScreenConnect instance, including elevated access and access to active sessions.
Why this ScreenConnect bug matters
This vulnerability does not read like a simple remote code execution bug, but it still creates a dangerous path for compromise. ConnectWise classifies it under CWE-347, which covers improper verification of cryptographic signatures, and says the flaw can affect confidentiality, integrity, and availability if abused.
The vendor has also marked the issue as Priority 1 High. In its bulletin, ConnectWise says vulnerabilities in this class should be treated as emergency changes or patched as soon as possible, usually within days.
ConnectWise separately noted that security researchers have observed attempts to abuse disclosed ASP.NET machine key material more broadly. The company says ScreenConnect uses instance-specific cryptographic material, but if that material is exposed, an attacker may be able to forge or modify trusted values and perform unauthorized actions within the instance.
What ConnectWise changed in version 26.1
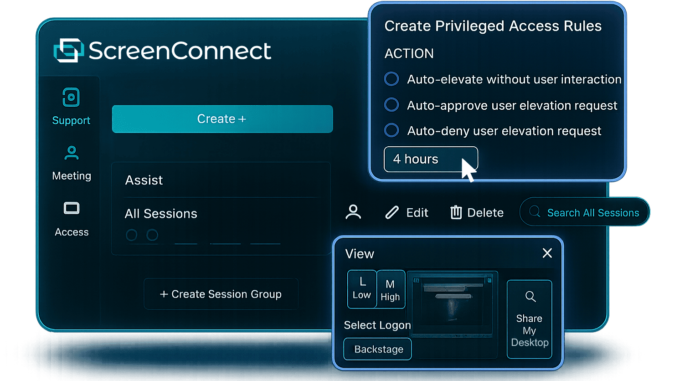
ConnectWise says ScreenConnect 26.1 adds stronger protections for machine key handling, including encrypted storage and management. The company also says the update improves protection for instance cryptographic material, enables on-demand regeneration of instance cryptographic material through an administrative action, and strengthens application integrity.
That update reduces the risk tied to disclosed authentication material and shortens the window in which exposed keys could be abused. ConnectWise frames the release as part of a broader security hardening effort for ScreenConnect authentication trust.
Who needs to act now
Cloud-hosted ScreenConnect customers do not need to take action. ConnectWise says no action is required for cloud deployments because the mitigation has already been applied on the backend.
On-premises ScreenConnect users need to upgrade to version 26.1. ConnectWise says partners should download and apply the update through the official ScreenConnect download page, and customers with lapsed maintenance will need to renew before installing the latest supported release.
ScreenConnect CVE-2026-3564 at a glance
| Item | Details |
|---|---|
| Vulnerability | CVE-2026-3564 |
| Product | ConnectWise ScreenConnect |
| Affected versions | Versions prior to 26.1 |
| Fixed version | 26.1 |
| CVSS score | 9.0 |
| CWE | CWE-347 |
| Cloud customers | No action required |
| On-prem customers | Upgrade to 26.1 |
What admins should do next
- Upgrade on-premises ScreenConnect servers to version 26.1 immediately.
- Review who can access ScreenConnect server configuration data and cryptographic material.
- Audit ScreenConnect logs for unusual authentication behavior or suspicious session activity.
- Regenerate instance cryptographic material where appropriate after updating.
- Treat exposed machine key material as a potential compromise event.
FAQ
It is a critical ScreenConnect vulnerability involving server-level cryptographic material used for authentication. If that material becomes accessible, an attacker may be able to gain unauthorized access and perform actions inside the instance.
ConnectWise says all ScreenConnect versions before 26.1 are affected.
No. ConnectWise says cloud-hosted deployments require no action.
Upgrade to ScreenConnect 26.1 as soon as possible and review logs for suspicious authentication activity.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages