New malware campaigns turn routers and network devices into DDoS nodes and crypto miners

Two newly documented malware campaigns show how quickly attackers can turn network infrastructure into profit and attack capacity. Security researchers say one strain, called CondiBot, turns Linux-based network devices into DDoS bots, while the other, Monaco, brute-forces SSH access and deploys Monero mining software across servers, routers, IoT gear, and network appliances.
Eclypsium disclosed both malware strains this month after capturing fresh samples on March 6, 2026. The company says the findings highlight a broader trend in which financially motivated actors now target the same network and edge systems that nation-state groups have pursued for years.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
That matters because many of these devices sit outside normal endpoint visibility. Routers, firewalls, VPN appliances, and embedded Linux systems often do not run standard EDR tools, which gives attackers more room to persist, mine cryptocurrency, or prepare disruptive attacks without drawing immediate attention. Google Threat Intelligence Group said enterprise-focused zero-day exploitation grew in 2025, with security and networking products among the top targets.
CondiBot expands the Mirai-style botnet playbook
Eclypsium describes CondiBot as a DDoS botnet executor built on the Mirai model. Its goal is simple: compromise Linux devices and convert them into remotely controlled bots that can launch network floods on command. The samples Eclypsium analyzed were compiled for x86-64, ARM32, ARM64, and MIPS, which makes the malware suitable for a wide range of servers, IoT hardware, routers, and Juniper equipment.
The malware also shows signs of active adaptation. Eclypsium says this CondiBot variant uses an internal identifier, QTXBOT, that has not appeared in prior public Condi reporting. The company also found 32 registered attack handlers in the sample, which suggests a broader DDoS feature set than earlier Condi variants documented in past research.
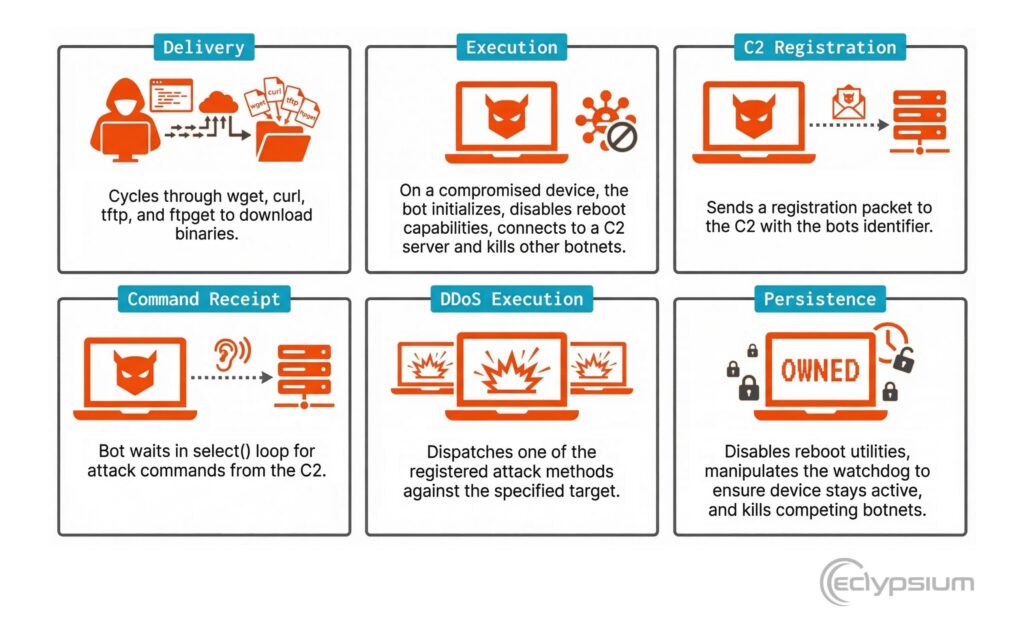
Once CondiBot lands on a device, it cycles through common transfer tools such as wget, curl, tftp, and ftpget to deliver its payload. After launch, it modifies reboot-related permissions, connects to its command server, and waits for attack instructions. Eclypsium also says it kills competing malware processes and manipulates watchdog behavior to keep the compromised device under its control.
Monaco focuses on SSH brute forcing and Monero mining
The second strain, Monaco, takes a different route. Eclypsium says it is an active multi-architecture cryptojacking operation that brute-forces weak SSH credentials on servers, routers, IoT devices, and network gear, then deploys Monero mining software after it gets in. The malware was written in Go 1.24.0 and includes its own scanning and credential collection logic.
According to Eclypsium, Monaco does more than mine. It harvests working SSH credentials from compromised systems and sends them back to command-and-control servers, which gives the operators a way to expand the campaign across additional hosts. That turns every weak password into a possible bridge to the next device.
The result is a two-part threat. On one side, compromised devices burn resources to produce cryptocurrency. On the other, the same infrastructure can help the operators move laterally or scale future compromise attempts. Eclypsium says both malware families target architectures common in embedded and network equipment, which makes them especially relevant for organizations with exposed SSH services or aging appliance fleets.
Why network devices keep drawing attackers
The broader data supports this shift. Verizon’s 2025 DBIR says exploitation of vulnerabilities in network edge devices, especially VPNs, rose by almost 8x year over year, jumping from 3% to 22% of breaches involving exploits. The report summary cited by Eclypsium also says only 54% of those vulnerabilities were fully remediated, with a median remediation time of 32 days.
Google Threat Intelligence Group’s 2025 zero-day review shows the same pressure on enterprise infrastructure. GTIG tracked 90 zero-day vulnerabilities exploited in the wild in 2025, and 43 of them targeted enterprise technologies. Security and networking products accounted for 21 of those enterprise-targeted zero-days, including many aimed at edge devices such as routers, switches, VPNs, and security appliances.
That mix creates a clear security gap. Attackers want devices that hold privileged network positions, remain internet reachable, and rarely get the same monitoring as laptops or servers. These campaigns show that criminal groups now see those boxes as revenue sources and as attack infrastructure.
Malware details at a glance
| Malware | Main purpose | Primary targets | Entry method | Key behavior |
|---|---|---|---|---|
| CondiBot | DDoS botnet | Linux servers, routers, IoT, Juniper gear | Payload delivery through common transfer utilities | Registers with C2, waits for attack commands, kills rival bots |
| Monaco | Cryptojacking and credential harvesting | Servers, routers, IoT, network devices | SSH brute force | Deploys Monero miner and sends harvested credentials to C2 |
What defenders should do now
- Enforce strong, unique SSH passwords and disable default credentials on internet-facing devices.
- Patch routers, VPNs, firewalls, and other edge devices faster, especially when vendors publish fixes for exposed services.
- Monitor unusual outbound traffic from network appliances, especially traffic that does not fit the device’s normal role.
- Review devices for unfamiliar processes, unexpected resource spikes, or signs of unauthorized SSH activity.
- Apply firmware integrity and configuration monitoring to infrastructure that cannot run standard EDR agents.
FAQ
Eclypsium describes CondiBot as a Mirai-style DDoS botnet executor that turns compromised Linux devices into attack nodes.
Monaco brute-forces weak SSH credentials, installs Monero mining software, and sends harvested access data back to its operators.
They often sit in privileged network positions, stay exposed to the internet, and usually lack the kind of monitoring common on desktops and servers. GTIG says networking and security products were among the most targeted enterprise systems in 2025 zero-day exploitation.
No. Eclypsium says these campaigns show that financially motivated actors now target network infrastructure aggressively for DDoS operations and crypto mining, not just espionage.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages