New VoidStealer variant bypasses Chrome ABE without injection or admin rights

A new version of the VoidStealer infostealer has become the first malware seen in the wild to bypass Google Chrome’s Application-Bound Encryption without code injection or privilege escalation. Gen Digital says the technique appeared in VoidStealer 2.0 and uses a debugger-based method with hardware breakpoints to capture Chrome’s v20_master_key from memory, giving attackers a stealthier way to steal credentials and cookies.
That matters because Google introduced Application-Bound Encryption, or ABE, in Chrome 127 on Windows to make it harder for infostealers running under the same user account to access sensitive browser data. Google said the feature ties protected data to the app’s identity through privileged services, raising the bar for cookie and credential theft.
Gen Digital says VoidStealer’s new method avoids two common warning signs that defenders often watch for: browser code injection and elevated privileges. Instead, the malware attaches to Chrome or Microsoft Edge as a debugger, waits for the right execution point, and then reads the decrypted key from memory when it briefly appears in plaintext. That lowers its detection footprint compared with many earlier ABE bypass approaches.
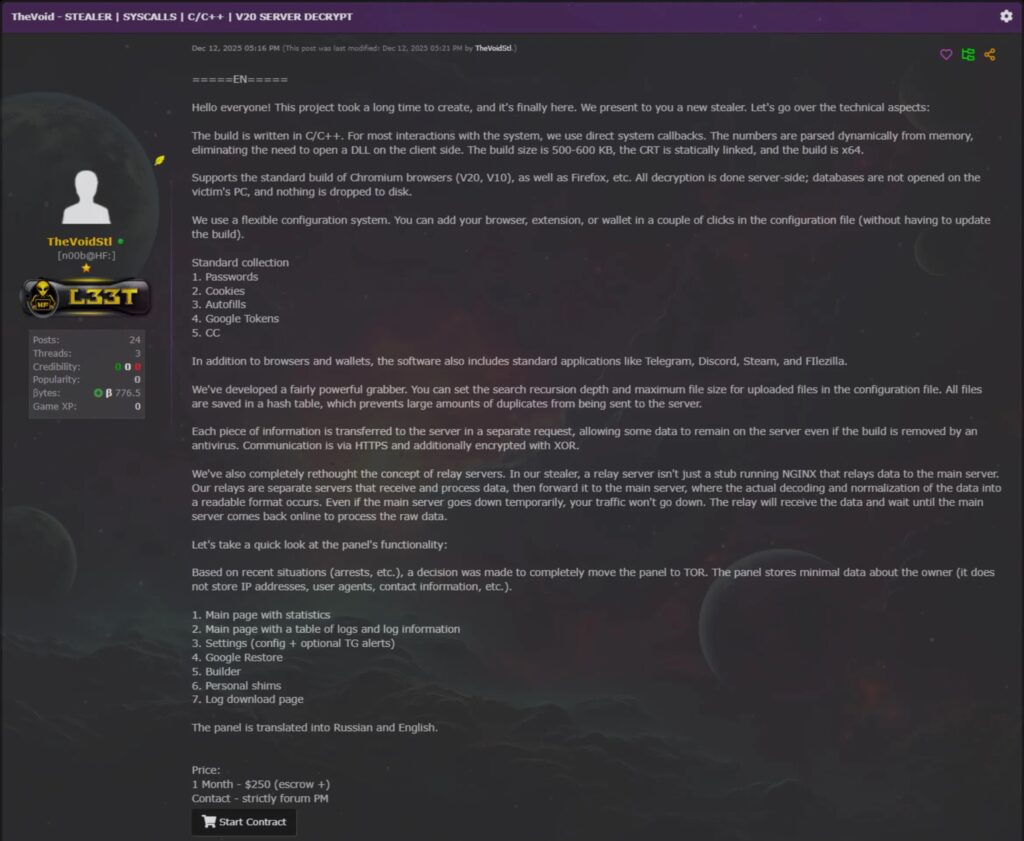
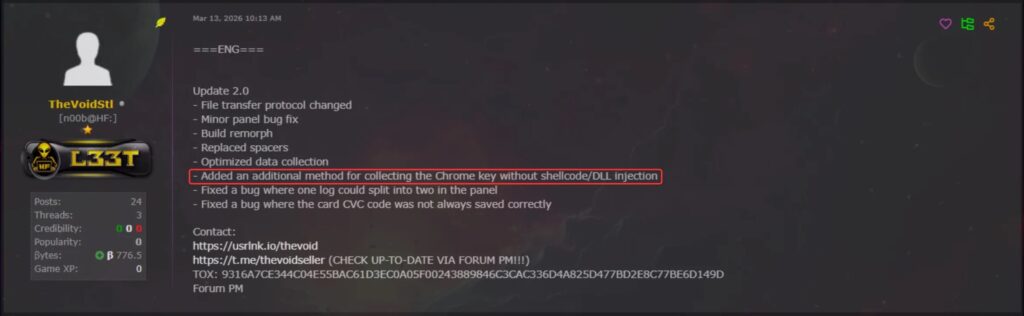
The researchers describe VoidStealer as a malware-as-a-service infostealer that surfaced on underground forums in late 2025 and evolved quickly from version 1.0 to version 2.1 in a little over three months. They say version 2.0 introduced the new debugger-based ABE bypass, adapted from the public ElevationKatz project, making it the first infostealer observed using this technique in real-world attacks.
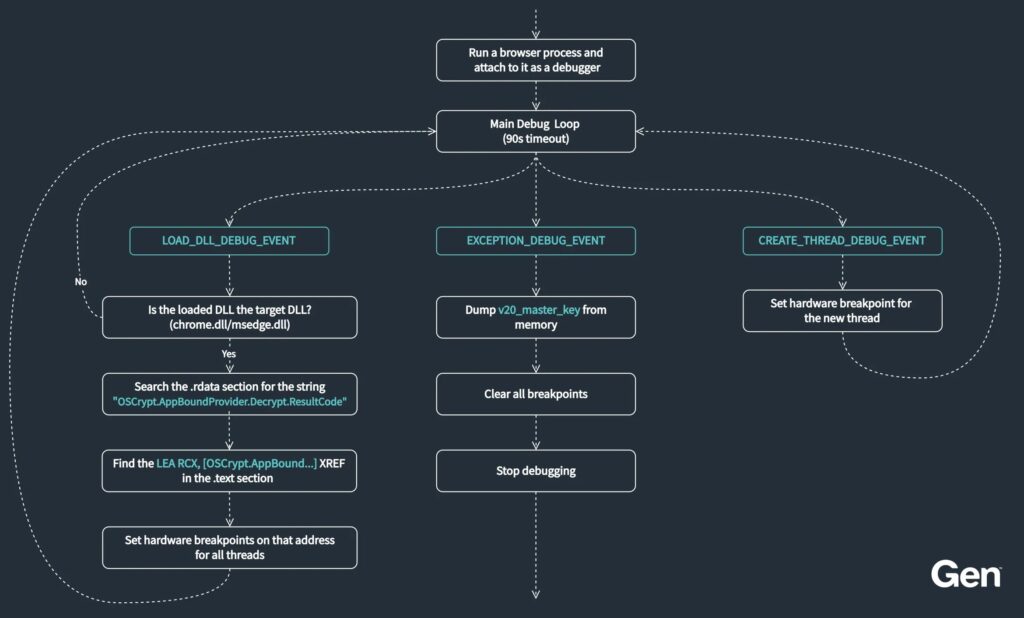
How the new bypass works
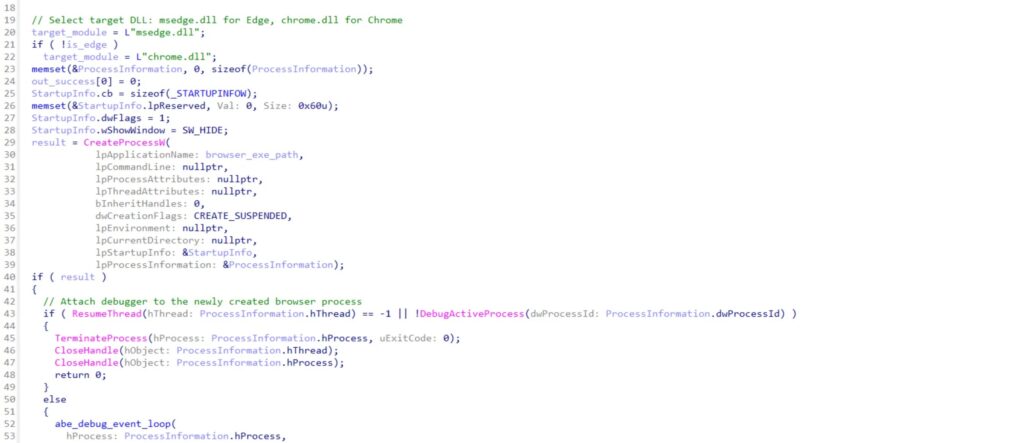
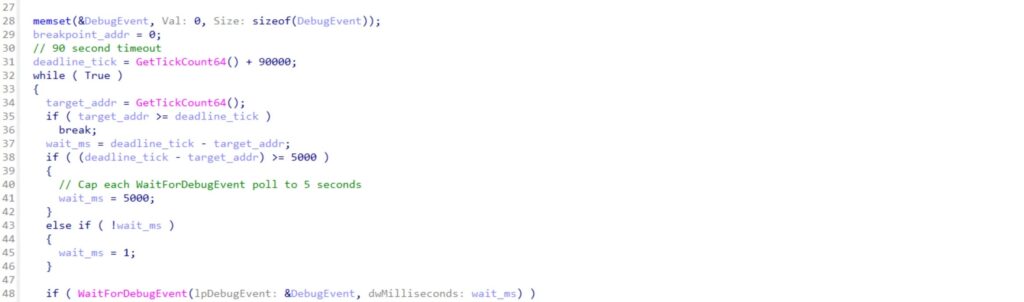
According to Gen Digital, VoidStealer launches Chrome or Edge in a suspended state, resumes it, and then attaches as a debugger with DebugActiveProcess. It monitors debug events until the browser loads the right DLL, then scans memory to find the code path associated with Chrome’s decryption flow. From there, it places hardware breakpoints using thread context registers rather than altering browser memory directly.
When the breakpoint hits, the malware reads a register that points to the plaintext v20_master_key, then pulls the key with ReadProcessMemory. Gen Digital says that lets the stealer recover protected browser data without the noisier behavior seen in injection-based methods.
This is a meaningful shift in browser theft tradecraft. Public bypass work has existed before, including projects that used injection or process hollowing to get around Chromium protections, but Gen Digital says VoidStealer is the first infostealer caught in the wild using a debugger-led approach with no injection and no admin rights.
Why Chrome ABE is no longer enough on its own
Google never positioned ABE as an absolute fix. When it launched the feature in July 2024, the company said it would make attacks harder by binding protected data to the browser’s identity and by generating system event logs when verified access attempts fail. That still helps defenders, but it does not eliminate the broader problem once attackers find ways to execute inside or alongside trusted browser flows.
VoidStealer shows exactly that. The malware does not smash through ABE with brute force. It waits until the browser itself reaches the right decryption point, then steals what it needs from memory. That makes this a bypass of the protection model in practice, even though Chrome’s underlying security design still raises the difficulty for many older infostealers.
Who and what the malware targets
Gen Digital says VoidStealer currently targets both Google Chrome and Microsoft Edge. The researchers also note that the stealer evolved fast and that the public availability of debugger-based ABE bypass ideas increases the chance that other malware families will copy the same method.
That copycat risk matters because browser data remains one of the most valuable targets in modern cybercrime. Cookies, saved passwords, payment data, and authenticated sessions can all help criminals hijack accounts, bypass logins, and move deeper into enterprise or personal systems. Google introduced ABE specifically to slow that class of threat, which shows how central browser theft has become in the infostealer ecosystem.
VoidStealer at a glance
| Item | Details |
|---|---|
| Malware | VoidStealer |
| Version highlighted | 2.0 |
| Reported by | Gen Digital |
| Main breakthrough | First infostealer seen bypassing Chrome ABE in the wild without injection or privilege escalation |
| Technique | Debugger-based memory extraction with hardware breakpoints |
| Targeted browsers | Google Chrome, Microsoft Edge |
| Key stolen item | v20_master_key |
| Main risk | Theft of cookies, passwords, and other protected browser data |
Detection opportunities for defenders
Gen Digital says defenders should treat autonomous debugger attachment to a browser as a major warning sign. The company recommends looking for unexpected DebugActiveProcess calls aimed at Chrome or Edge, unusual browser launches with hidden or headless-style flags, and third-party processes reading browser memory.
Those signals matter because legitimate software rarely debugs a user’s browser in a fully automated way. Security teams that focus only on classic injection patterns may miss this newer approach. This is an inference based on Gen Digital’s description of the malware’s lower detection footprint and debugger-led behavior.
What users and admins should do now
The immediate fix is not as simple as a single browser update, because this is about runtime theft rather than a basic browser vulnerability. Still, organizations can reduce risk by hardening endpoint detection around browser debugging behavior, limiting unknown software execution, keeping browsers current, and watching for infostealer activity that targets saved credentials and session data. Google’s broader advice around safer browsing and enterprise monitoring still applies, but VoidStealer shows that strong endpoint visibility matters just as much as browser-side protections.
FAQ
VoidStealer is a malware-as-a-service infostealer that Gen Digital says appeared on underground forums in late 2025 and evolved quickly into a more advanced browser data thief.
It bypassed Chrome’s Application-Bound Encryption with a debugger-based method that did not require code injection or elevated privileges.
It is a Windows protection Google introduced in Chrome 127 to tie sensitive browser data to the browser’s identity, making theft harder for malware running as the same user.
No. Gen Digital says the same technique also targets Microsoft Edge.
Gen Digital highlights unexpected browser debugging, hidden browser launches, and suspicious memory reads against browser processes as strong detection opportunities.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages