Copyright-themed lures spread PureLog Stealer in stealthy credential theft campaign

A new phishing campaign is using fake copyright violation notices to infect organizations with PureLog Stealer, a data-stealing malware that runs almost entirely in memory. Trend Micro says the operation targets sectors including healthcare, government, education, and hospitality, with the strongest activity seen in Germany and Canada, plus additional victims in the United States and Australia.
The attack does not rely on a Windows flaw or a browser exploit. Instead, it uses social engineering to pressure victims into opening what looks like a legal complaint, then quietly launches a multi-stage infection chain that steals browser credentials, cryptocurrency wallet data, browser extension data, and basic system details.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This matters because the campaign combines believable lures with a delivery chain built to avoid easy detection. Trend Micro says the malware uses encrypted payloads, remote key retrieval, Python-based execution, and in-memory loading, which leaves very little behind on disk for traditional antivirus tools to flag.
What PureLog Stealer does
PureLog is an infostealer sold as a low-cost and easy-to-use tool, which makes it accessible to less-skilled threat actors. Once it lands on a machine, it can collect Chrome credentials, extension data, cryptocurrency wallet information, and general host details that can later support account takeover, fraud, or broader compromise.
Trend Micro says the campaign used language-matched lures, with German-language messages aimed at Germany and English-language versions aimed at Canada and other regions. That level of localization suggests a more deliberate operation, not a random mass spam run.
How the infection chain works
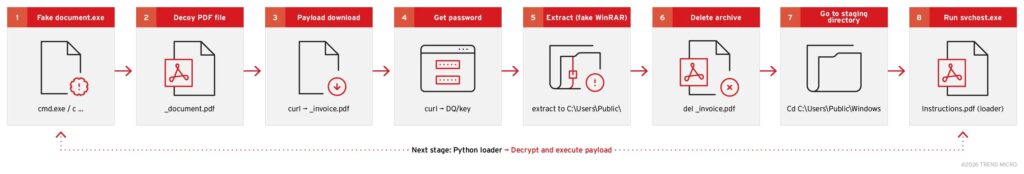
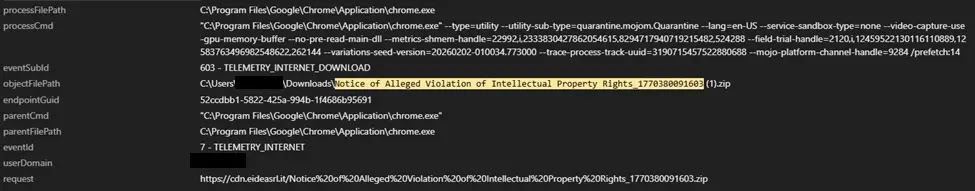
The victim first receives a phishing email that links to a malicious download instead of attaching the malware directly. The downloaded file uses a name that resembles a legal complaint, which increases the chance that the target will open it without questioning it.
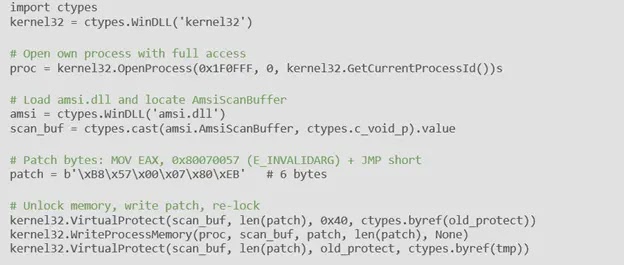
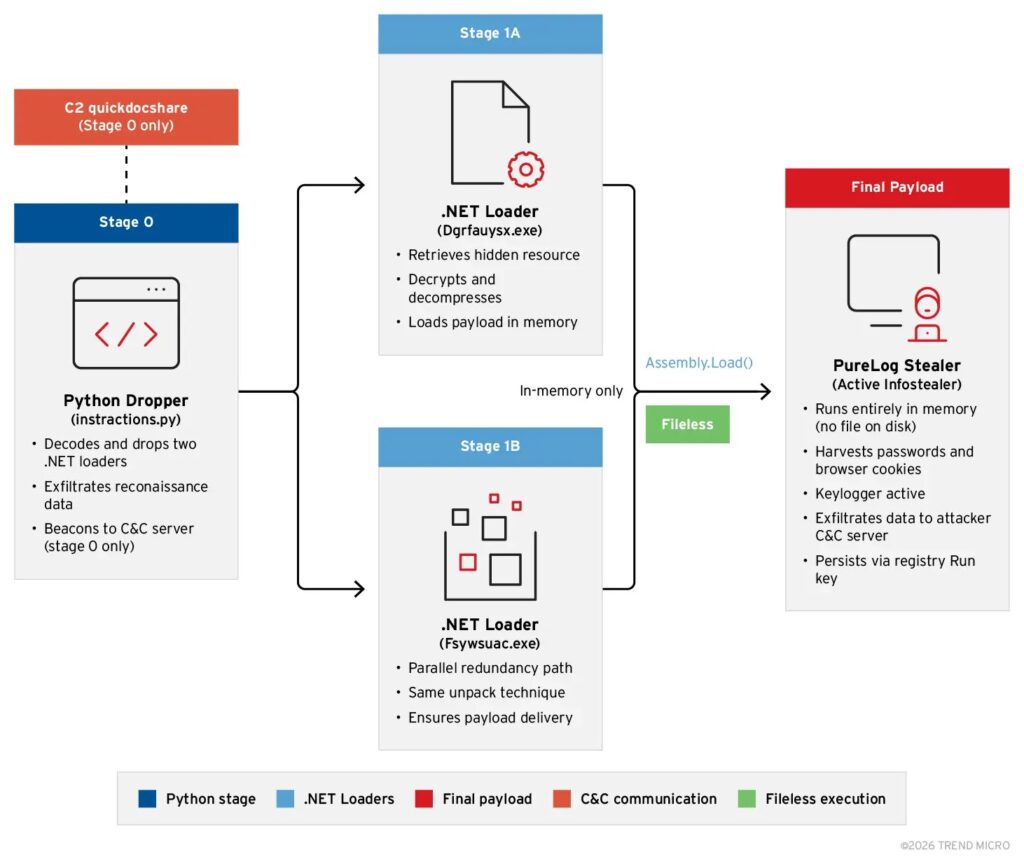
Once the file runs, a decoy PDF opens so the victim sees something harmless. Behind the scenes, the malware contacts attacker infrastructure, pulls down an encrypted archive disguised as invoice.pdf, fetches the decryption password from a separate server, and then uses a renamed WinRAR binary to unpack the real payload. Trend Micro says the final stages involve a renamed Python interpreter, an obfuscated Python script, AMSI bypass code, registry persistence, and two .NET loaders that decrypt and launch PureLog directly in memory.
Attack chain at a glance
- Phishing email delivers a download link
- Victim opens a fake copyright complaint executable
- A decoy PDF appears on screen
- Malware downloads an encrypted archive disguised as
invoice.pdf - A separate server returns the decryption password at runtime
- A renamed WinRAR executable extracts the hidden payload
- A renamed Python interpreter runs an obfuscated script
- The script patches AMSI in memory and sets persistence
- Two .NET loaders decrypt and launch PureLog Stealer in memory
Why defenders may miss it
This campaign stands out because it avoids the usual signs defenders look for. Trend Micro says the malware executes filelessly, retrieves keys on demand, and uses in-memory loading, which sharply reduces the amount of suspicious disk activity security tools can inspect later.
The script also collects a screenshot, the machine name, the logged-in username, and the installed antivirus product before sending that data to the command-and-control server over HTTPS. That gives the attacker a quick picture of the environment before PureLog begins stealing data.
| Stage | What happens | Why it matters |
|---|---|---|
| Initial lure | Fake copyright complaint arrives by email | Increases the chance of manual execution |
| Decoy phase | Benign PDF opens | Reduces suspicion |
| Retrieval phase | Encrypted archive and remote password are fetched separately | Makes offline analysis harder |
| Execution phase | Python and .NET loaders run in memory | Leaves fewer forensic traces |
| Theft phase | Credentials, wallet data, browser data, and host info are collected | Supports fraud and account compromise |
Source: Trend Micro research.
Who is at risk
Trend Micro says the campaign has hit healthcare, government, education, and hospitality organizations. These sectors often deal with legal notices, compliance requests, and customer or public-facing communications, which makes a copyright complaint lure easier to believe.
The strongest activity appeared in Germany and Canada, but Trend Micro also observed victims in the United States and Australia. That means the campaign is not limited to one geography, even if the initial lures were regionally tailored.
What security teams should do now
Organizations should warn staff that copyright complaints, trademark notices, and similar legal messages can be used as malware lures, especially when they include a download link instead of a normal document attachment. User awareness matters here because the attack starts with manual execution, not with an exploit.
Trend Micro also recommends monitoring unusual registry Run key entries, watching for Python or WinRAR activity from odd locations, and blocking outbound connections to known malicious domains involved in the campaign. Behavioral detection and network telemetry matter more than signature-only defenses in this case.
Defensive steps
- Treat unexpected copyright or legal complaint emails as suspicious
- Block or inspect downloads delivered through email links
- Monitor
HKCU\Runfor unusual persistence entries - Watch for Python or WinRAR processes from non-standard paths
- Use behavior-based detections, not only signature-based AV
- Review outbound HTTPS connections to suspicious infrastructure
FAQ
PureLog Stealer is an infostealer that can collect browser credentials, extension data, cryptocurrency wallet information, and host details from infected systems.
It uses phishing emails with download links and disguises the malware as a copyright violation notice or legal complaint.
Trend Micro says no. The campaign depends on social engineering and user execution rather than a software exploit.
The campaign was most active in Germany and Canada, with additional victims in the United States and Australia. Targeted sectors include healthcare, government, education, and hospitality.
Because it uses encrypted payloads, remote key retrieval, AMSI patching, and in-memory execution, which reduces the usual forensic and disk-based signs of compromise.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages