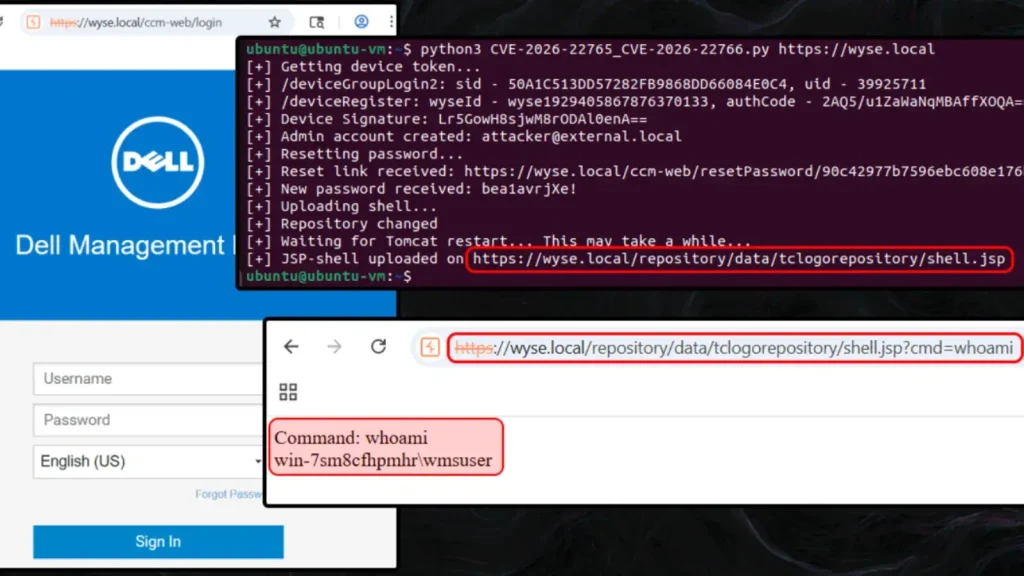
Threat actors keep hitting exposed MS-SQL servers to deploy ICE Cloud scanner

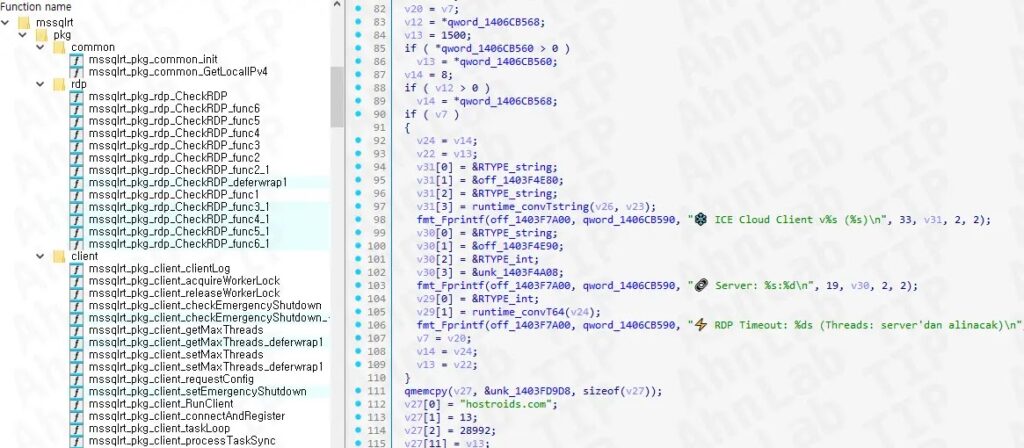
Threat actors are still targeting exposed Microsoft SQL Server systems with weak credentials, and the latest payload is a scanner called ICE Cloud Client. According to AhnLab’s ASEC team, the activity links back to Larva-26002, a cluster that previously used Trigona and Mimic ransomware and has now shifted toward scanning and brute-force operations against more MS-SQL targets.
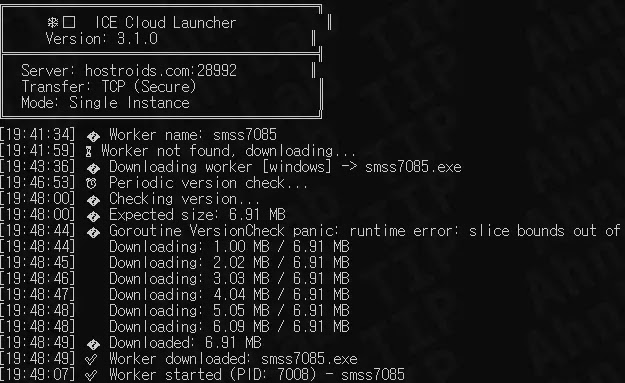
ASEC says this campaign has stayed active from at least January 2024 into March 2026, with the operator reusing parts of the same playbook while updating the tooling. In the newest cases, the group used a Go-based ICE Cloud toolset after earlier campaigns used ransomware and, later, a Rust-based scanner.
The practical risk for admins is simple. A poorly secured internet-facing SQL Server can become both a victim and a launch point for more attacks. Microsoft’s own SQL Server security guidance warns that brute force, password spray, and ransomware remain common infrastructure threats, and it recommends strong passwords, patching, access control, and defense-in-depth protections.
ASEC’s report shows the attackers still focus on systems exposed to the internet and vulnerable to brute-force or dictionary attacks. After gaining access, they profile the host, create or download malware, connect to a command-and-control server, and then use the infected machine to scan additional MS-SQL endpoints.
What ASEC says happened
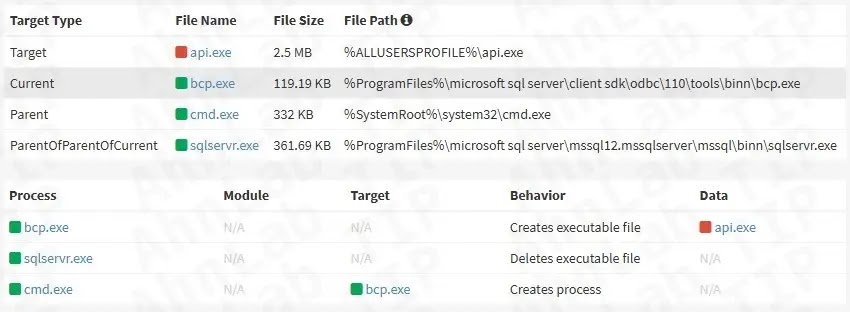
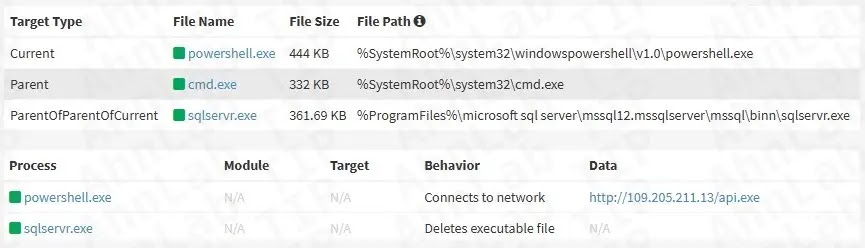
ASEC says Larva-26002 targeted improperly managed MS-SQL servers, used the legitimate bcp.exe utility to write malware from a database table to disk, and in some cases fell back to curl, Bitsadmin, or PowerShell when needed. The new chain ends with ICE Cloud Client, which acts as a scanner and brute-force tool.
The researchers also said the malware contains Turkish-language strings, a detail they tied to earlier Mimic-related activity. They further noted emoji-like elements in the binary and said those details suggest the developer may have used generative AI in parts of the coding process.
How the infection chain works
| Stage | What the attacker does | Why it matters |
|---|---|---|
| Initial access | Targets internet-exposed MS-SQL servers with weak credentials | Weak passwords open the door to brute-force entry |
| Recon | Runs commands such as hostname, whoami, ifconfig, netstat, and tasklist | Helps the attacker understand the host and active services |
| Malware delivery | Uses bcp.exe to export malware from table uGnzBdZbsi to C:\ProgramData\api.exe, often with format file FODsOZKgAU.txt | Shows repeated tradecraft that ASEC has tracked since 2024 |
| Alternate delivery | Uses curl, Bitsadmin, or PowerShell to fetch api.exe | Gives the actor a fallback when BCP fails |
| Payload stage | Launches ICE Cloud Launcher, then downloads ICE Cloud Client from C2 | Turns the server into a scanning node |
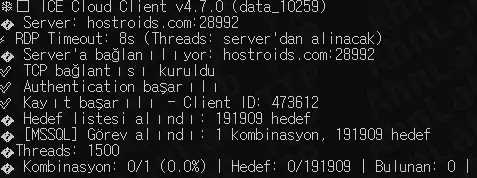
| Follow-on activity | Receives target MS-SQL addresses and credential pairs such as ecomm/ecomm | Lets the infected host probe other database servers for successful logins |
Why this campaign matters
This is no longer just a ransomware story. The campaign now looks more like infrastructure building. Instead of only encrypting systems, the attackers appear to use compromised SQL servers as scanners that test more database endpoints and send successful results back to the control server. That gives the operator a growing map of reachable and weakly protected database assets.
That shift matters because it can scale quietly. A scanner-based campaign can keep feeding future intrusions, data theft, lateral movement, or ransomware deployment later. Even when the immediate payload is not encryption, the compromise still signals serious exposure.
What administrators should check now
- Review whether any SQL Server instance is directly reachable from the public internet. Microsoft documentation stresses access control and firewall protections for SQL Server environments.
- Audit SQL authentication settings and review all high-privilege accounts, especially older or rarely used ones. Microsoft says weak passwords and careless use of the sa account increase risk.
- Hunt for suspicious files such as api.exe under C:\ProgramData\ and for odd use of bcp.exe, curl, Bitsadmin, or PowerShell on database hosts. ASEC specifically observed those methods in this campaign.
- Check outbound connections from SQL servers for unexpected traffic to unfamiliar hosts. ASEC said the malware authenticates with a C2 server, downloads the scanner, and sends back successful results.
- Rotate passwords for SQL logins and disable or rename risky accounts where possible. Microsoft recommends strong passwords and says the sa login should not be enabled unless an application truly requires it.
- Run vulnerability assessment and general hardening reviews. Microsoft recommends vulnerability assessment, auditing, patching, and layered security controls to reduce exposure.
Indicators that deserve urgent review
- Repeated failed login attempts against MS-SQL
- New or unexplained files in C:\ProgramData\
- Unusual execution of bcp.exe on a server that rarely exports data
- Bitsadmin or curl activity on a database server
- Unexpected outbound traffic from the SQL host
- Signs that a server is attempting to authenticate to large numbers of external MS-SQL addresses
Bottom line
Organizations should treat this campaign as a warning that weakly secured SQL Server systems remain an easy target. ASEC’s latest findings show that Larva-26002 has kept refining the same attack path for more than two years, while Microsoft’s own guidance still points to the same basics: reduce exposure, lock down authentication, patch systems, and watch closely for abuse of legitimate tools.
FAQ
ASEC describes ICE Cloud Client as a Go-based scanner and brute-force malware used after MS-SQL compromise. It receives targets from a control server and reports successful access back to that server.
AhnLab attributes the activity to Larva-26002, a threat actor it says previously distributed Trigona and Mimic ransomware before shifting toward scanner deployment on compromised systems.
ASEC says the group targets internet-exposed MS-SQL servers that use simple credentials and attacks them with brute-force or dictionary methods. Microsoft separately lists brute force and password spray among major SQL Server infrastructure threats.
BCP is a legitimate SQL Server command-line utility for importing and exporting data. ASEC says the attackers abused it to write malware from a table to a local file path on the compromised server.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more



User forum
0 messages