Dell Wyse Management Suite flaws can be chained into full server compromise
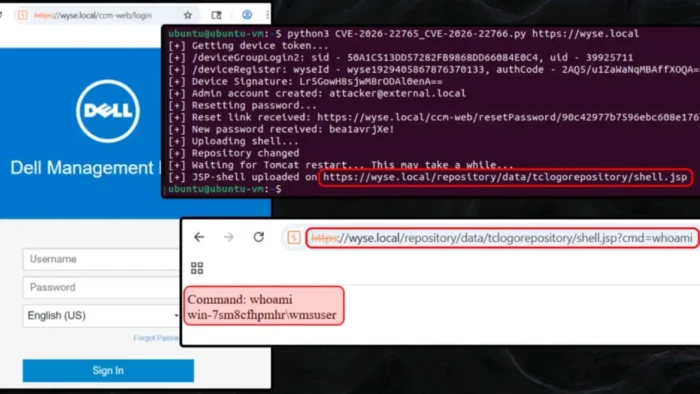
A newly detailed attack chain shows how multiple logic flaws in Dell Wyse Management Suite On-Premises can be combined into full server compromise. Researchers say an attacker can start with very limited access, escalate privileges, and then reach remote code execution on the management server. Dell has already fixed the issues in Wyse Management Suite 5.5.
The two main bugs at the center of the chain are CVE-2026-22765 and CVE-2026-22766. Dell describes the first as a missing authorization flaw that can let a low-privileged remote attacker gain elevated rights, while the second is an unrestricted upload flaw that can let a high-privileged remote attacker achieve remote execution. Dell rates CVE-2026-22765 at 8.8 and CVE-2026-22766 at 7.2, and says both affect WMS versions before 5.5.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
What makes the research notable is the way the issues can be chained. Positive Technologies said the full path can end in unauthenticated remote code execution, not just privilege escalation, because the flaws connect across device registration, user import, admin role assignment, password reset logic, and file upload behavior.
Dell says both the free Standard edition and the paid Pro edition are affected in on-premises deployments if they run a version older than 5.5. The fix shipped on February 23, 2026, and Dell’s advisory was first published on February 24, 2026, with a later update on March 20 that did not change the technical content.
How the attack starts
According to Positive Technologies, the attack can begin during device registration. In the default configuration of the on-premises product, a rogue device can allegedly be registered with an empty group token. That still returns a device identifier and authentication code, which gives the attacker a foothold to interact with the WMS API even though the device lands in a quarantine group.
From there, the researchers say the attacker can reach Active Directory import routes that should not have been exposed in this way. By calling importADUserGroups and addRoleToADGroup, the attacker can create a new AD-backed role group and then assign the Admin role to it. A final call to importADUsers can then create a new administrator account tied to that role group.
Why the login barrier does not stop the chain
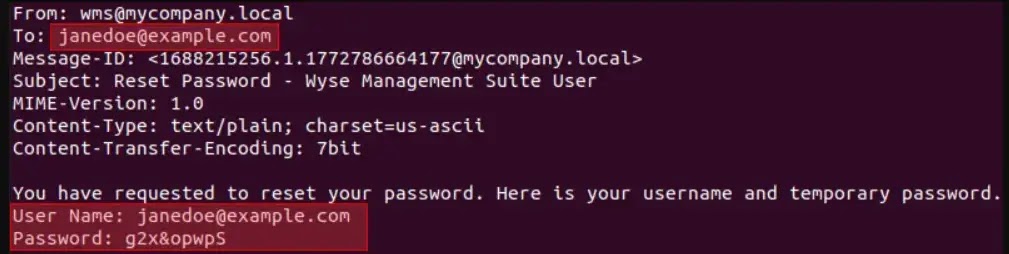
Creating a new administrator account is not enough by itself because the imported account gets an auto-generated password that is not shown to the attacker. Positive Technologies says it found two ways around that barrier.
The first route uses the password reset flow. The researchers say WMS blocks password resets for imported AD users, but that check can fail if the attacker imports the admin with an empty AD UPN. In that case, the platform may treat the account as eligible for password reset, allowing the new password to be sent to an external email address controlled by the attacker. Positive Technologies says this method depends on SMTP being configured and outbound email to external recipients being allowed.
The second route works only in WMS Pro environments with LDAP login configured. In that setup, the researchers say an attacker can import the new administrator using the objectGUID and sAMAccountName of a compromised low-privileged domain user, then log in to the administrator account with those domain credentials.
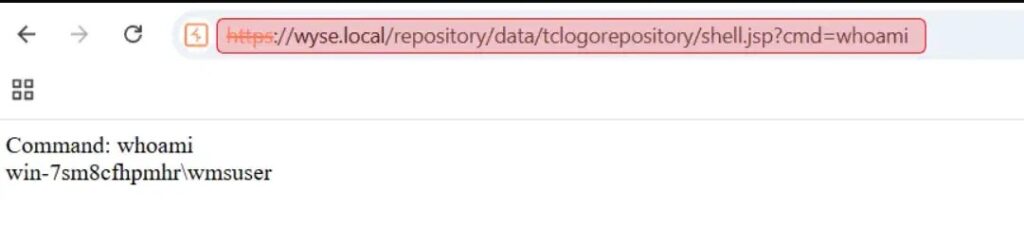
How remote code execution is achieved
Once administrative access is in place, the final stage moves to file upload and path control. Positive Technologies says WMS includes filters meant to block classic path traversal tricks, but an administrator can change the default local repository path through a hidden endpoint. The researchers say they pointed that path to Tomcat’s ROOT web application directory, where JSP execution is enabled.
That alone is not enough because WMS caches the repository path in memory. Positive Technologies says the attacker can clear that cache by restarting Tomcat through an available admin action. After that restart, a JSP payload uploaded through an image upload route gets written to the web root, which then leads to command execution on the server.
What the full exploit chain looks like
| Stage | What researchers say happens | Result |
|---|---|---|
| Initial foothold | Register a rogue device with an empty group token in default on-premises configuration | Attacker gets a device identifier and auth code |
| Privilege escalation | Abuse importADUserGroups, addRoleToADGroup, and importADUsers | New admin account gets created |
| Authentication bypass | Use password reset logic or LDAP-based login path | Attacker signs in as admin |
| Repository abuse | Change local file repository path to Tomcat ROOT | Upload destination moves into web root |
| Cache reset | Restart Tomcat to clear cached path | New path becomes active |
| Code execution | Upload JSP payload through an image upload route | Remote code execution on WMS server |
Why this matters
This case shows how smaller logic flaws can become far more serious when combined. Dell’s advisory lists the issues individually, but the researcher’s write-up shows how a real attacker could move from a weak starting position to full server takeover by chaining the bugs together. That makes patching more urgent for organizations that run WMS On-Premises to manage thin clients and related infrastructure.
It also matters because the bugs affect the management layer, not just a single endpoint. A successful compromise of WMS could give an attacker control over the system used to manage Dell thin client environments, which can widen the impact far beyond one server. This risk follows directly from Dell’s description that the flaws can be exploited to compromise the affected system and from the researcher’s demonstration of command execution on the WMS host.
What admins should do now
- Update Dell Wyse Management Suite On-Premises to version 5.5 or later. Dell lists 5.5 as the remediated version for the affected flaws.
- Review whether your deployment exposes WMS interfaces more broadly than needed. The reported chain relies on API access that should be tightly restricted.
- Check SMTP and password reset settings, especially if external outbound mail is allowed from the server. Positive Technologies says that condition helps one version of the chain succeed.
- Audit LDAP configuration in WMS Pro deployments and review the use of imported AD accounts. The Pro-only path described by researchers depends on LDAP login and a compromised domain user.
- Review local repository settings and any unexpected Tomcat restarts. Those actions played a direct role in the remote code execution stage described in the research.
FAQ
Dell says CVE-2026-22765 is a missing authorization vulnerability in Dell Wyse Management Suite versions before 5.5. A low-privileged remote attacker could exploit it to gain elevated privileges.
Dell says CVE-2026-22766 is an unrestricted upload of file with dangerous type vulnerability in WMS versions before 5.5. A high-privileged remote attacker could exploit it to achieve remote execution.
The advisory and researcher write-up focus on Dell Wyse Management Suite On-Premises. The affected product listing in Dell’s advisory covers versions prior to 5.5 for the on-premises product.
The research says the on-premises Standard and Pro editions are affected, though one of the login paths requires Pro with LDAP configured.
Patch to WMS 5.5 or later right away, then review admin account creation, LDAP settings, SMTP-enabled password reset behavior, file repository paths, and any suspicious Tomcat restarts. Dell’s advisory clearly lists 5.5 as the fixed release.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages