Mirai-based botnets are getting bigger, faster, and more useful to cybercriminals

Mirai-based botnets have evolved far beyond the malware family that first made headlines in 2016. Researchers and law enforcement now describe an ecosystem of variants that power record-breaking DDoS attacks, large-scale proxy abuse, and criminal services sold through chat platforms and underground markets. Cloudflare says the Aisuru-Kimwolf botnet alone now spans an estimated 1 million to 4 million infected hosts.
That scale has turned Mirai’s descendants into more than simple disruption tools. Cloudflare says Aisuru-Kimwolf has launched attacks as large as 31.4 Tbps and 14.1 billion packets per second, while the U.S. Department of Justice said botnets including Aisuru, KimWolf, JackSkid, and Mossad together infected millions of devices worldwide before a March 19, 2026 disruption effort.
The sample you shared captured the main direction correctly: Mirai’s code release helped create a sprawling variant ecosystem, Aisuru and Kimwolf emerged as standout threats, and the latest wave blends DDoS firepower with proxy monetization.
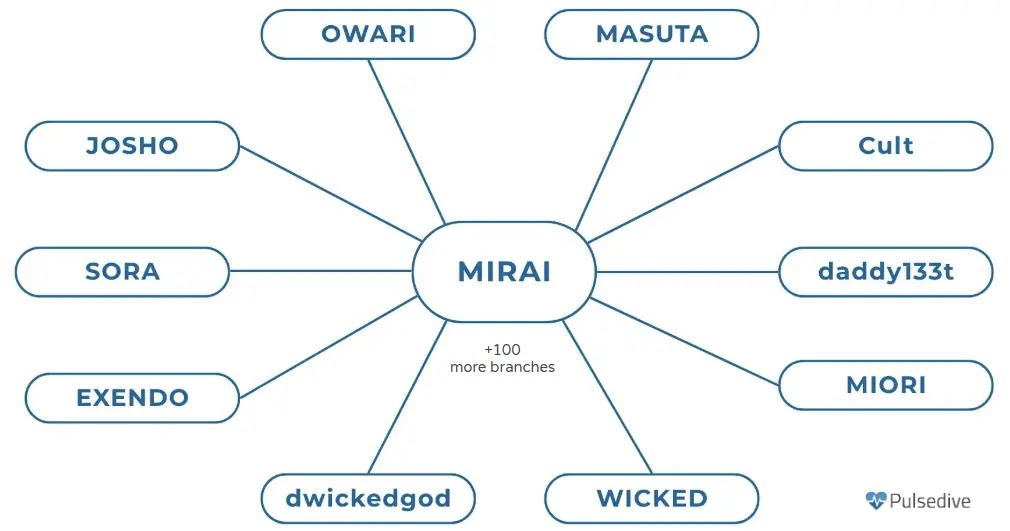
Why Mirai is still a major threat
Mirai became so influential because its source code leaked in 2016, giving other threat actors a ready-made foundation for new botnets. Cloudflare says Aisuru is one of the major descendants of that ecosystem, and Kimwolf is its Android-focused variant. Both continue the core Mirai model of compromising large numbers of exposed devices and turning them into remotely controlled attack nodes.
Many of those devices remain easy targets. Cloudflare says IoT devices and routers often stay online for long periods, use default credentials, and go unpatched, which makes them ideal botnet fodder. That same weak device hygiene helped Mirai spread years ago and still fuels modern variants today.
Aisuru and Kimwolf changed the scale of the problem
Cloudflare describes Aisuru-Kimwolf as a hyper-volumetric botnet capable of launching some of the largest DDoS attacks ever recorded. The company says the botnet has delivered 31.4 Tbps attacks, 14.1 Bpps floods, advanced DNS attacks, and HTTP attacks exceeding 200 million requests per second. It also says the botnet’s potential attack size grew by more than 700% within a single year spanning 2025 to 2026.
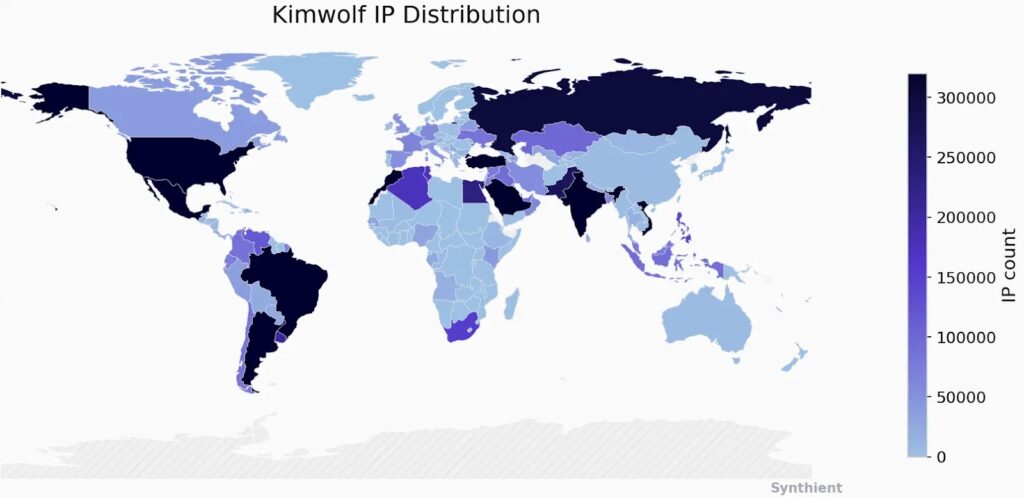
Kimwolf has become a major reason for that growth. Cloudflare says Kimwolf alone comprises about 2 million Android devices globally, especially across countries including Vietnam, Brazil, India, and Saudi Arabia. It targets Android-based endpoints such as mobile devices, streamers, and smart TV boxes.
These botnets now do more than DDoS
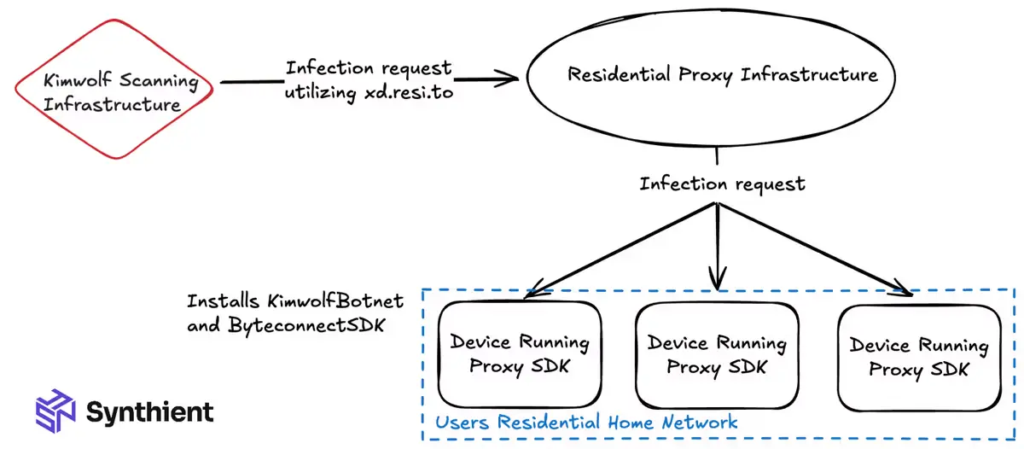
One of the biggest shifts is monetization. Cloudflare says Aisuru and Kimwolf do not only launch DDoS attacks. Their operators also sell access to infected devices as residential proxies, which lets other criminals hide malicious traffic behind ordinary home IP addresses. Cloudflare says these services have been used for anonymous scraping and other abuse, while chunks of the botnet are also sold as botnet-for-hire services through Discord and Telegram.
That means the same infected devices can support several revenue streams at once. Instead of only renting out attack traffic, operators can also profit from proxying, credential abuse, and broader criminal infrastructure services.
What law enforcement did in March 2026
On March 19, 2026, the U.S. Department of Justice announced a court-authorized operation to disrupt command-and-control infrastructure used by the Aisuru, KimWolf, JackSkid, and Mossad IoT botnets. The DOJ said the operation took place alongside actions in Canada and Germany, and that the disrupted botnets had launched record-breaking attacks against victims around the world, including some around 30 Tbps.
The DOJ also said the botnets had infected millions of devices worldwide, including routers, web cameras, DVRs, and other IoT hardware. The action targeted U.S.-registered domains, virtual servers, and other infrastructure allegedly tied to botnet operations.
Key facts at a glance
- Mirai’s leaked source code helped fuel a wide ecosystem of descendants and variants.
- Cloudflare estimates Aisuru-Kimwolf has between 1 million and 4 million infected hosts.
- Cloudflare says the botnet launched attacks as large as 31.4 Tbps and 14.1 Bpps.
- Kimwolf is the Android-focused branch of the broader Aisuru botnet.
- Operators monetize infected devices through residential proxies and botnet-for-hire services.
- The DOJ disrupted infrastructure for Aisuru, KimWolf, JackSkid, and Mossad on March 19, 2026.
Mirai then and now
| Category | Original Mirai model | Newer Aisuru-Kimwolf model |
|---|---|---|
| Main targets | IoT devices and routers | IoT, routers, Android devices, smart TV boxes |
| Core use | DDoS attacks | DDoS, proxy abuse, botnet-for-hire, scraping support |
| Growth pattern | Fast spread via weak device security | Larger, more commercialized, more adaptable |
| Notable scale | Massive for its era | Record-setting 30+ Tbps and 14.1 Bpps attacks |
The comparison above reflects Cloudflare’s explanation of how Aisuru and Kimwolf extend Mirai’s model into a broader criminal service ecosystem.
Why defenders should pay attention
These botnets do not just threaten websites and gaming services anymore. Cloudflare says attacks of this size can cause collateral disruption across providers and networks, even when the provider itself is not the intended target. The company noted that Aisuru traffic caused broader internet disruption in the United States due to sheer scale.
That makes modern Mirai variants a network-level problem, not only a victim-level one. Even organizations that never appear on an attacker’s target list can feel the impact when upstream infrastructure gets flooded or when residential proxy abuse makes malicious traffic harder to separate from real users.
What organizations should do
- Patch internet-facing routers, cameras, and IoT devices regularly.
- Replace default passwords with strong unique credentials during setup.
- Use DDoS mitigation that can react automatically to short, high-volume bursts.
- Monitor for unusual proxy behavior from consumer or residential IP ranges.
- Review exposed Android Debug Bridge services and similar weak points on Android-based devices.
FAQ
It is a botnet built from or inspired by the Mirai malware codebase, which infects connected devices and uses them for attacks such as DDoS. Modern variants now support additional abuse like proxying and botnet-for-hire services.
Cloudflare says Aisuru is a major Mirai-lineage botnet and Kimwolf is its Android-focused variant. Together they form one of the most powerful DDoS ecosystems active today.
Cloudflare estimates Aisuru-Kimwolf includes roughly 1 million to 4 million infected hosts, while Kimwolf alone accounts for around 2 million Android devices globally.
They are larger, more distributed, and more profitable than older Mirai waves. Operators can switch between DDoS attacks, proxy services, and rented criminal infrastructure, which makes disruption harder.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages