New ClickFix campaigns push Windows and macOS users to infect their own devices
ClickFix has become one of the most effective social engineering tricks in active cybercrime campaigns, and new research shows it now targets both Windows and macOS users with tailored lures. Instead of exploiting a software bug directly, attackers trick victims into pasting malicious commands into the Windows Run box or macOS Terminal, which hands over execution without the need for a traditional exploit.
Recorded Future’s Insikt Group said in a March 25 report that it tracked five separate ClickFix clusters using this approach. The campaigns impersonated brands and services such as Intuit QuickBooks, Booking.com, and Birdeye, while targeting sectors that included accounting, travel, real estate, and legal services.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
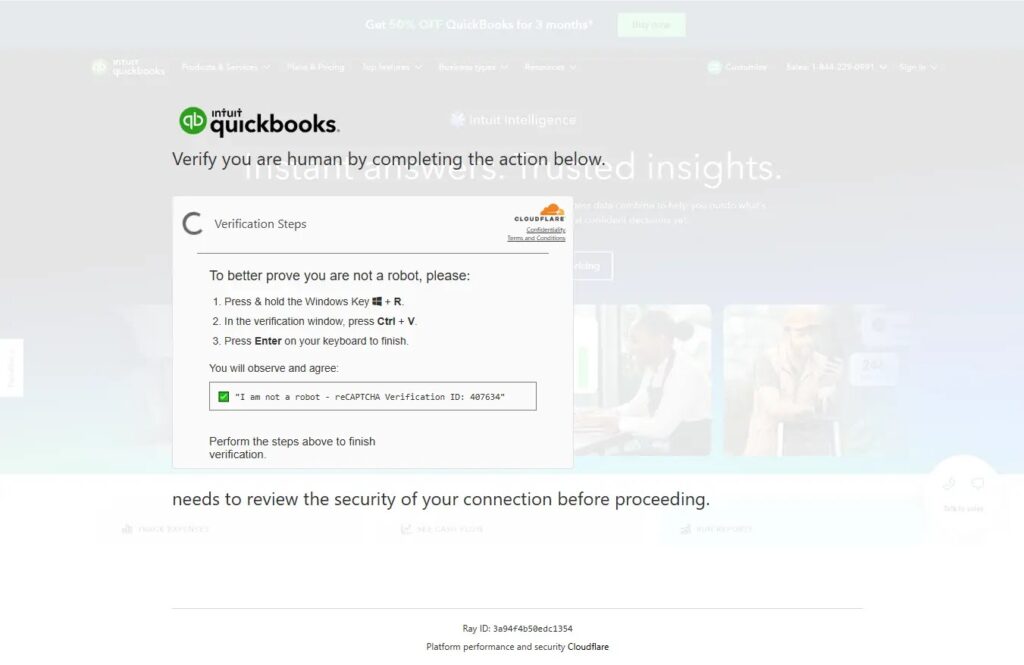
The technique keeps spreading because it shifts the attack away from the browser and onto the user. Microsoft has already warned that ClickFix works by leading people to fake verification pages, bogus error screens, or phony CAPTCHA checks, then convincing them to run a malicious command themselves. That makes the attack chain look routine even though it can end in malware installation, credential theft, or remote access.
How the new campaigns worked
Recorded Future said all five clusters followed the same basic model even when the lures looked different. A victim lands on a fake verification page, background JavaScript copies a command to the clipboard, and the page tells the user to paste it into a native system tool. On Windows, that usually means the Run dialog box or PowerShell. On macOS, the same trick pushes the user into Terminal.
According to the report, the Windows side often relied on living-off-the-land binaries and trusted system utilities to fetch the next-stage payload. In one QuickBooks-themed cluster, the command launched an obfuscated PowerShell chain that reached out to attacker-controlled infrastructure and then installed NetSupport RAT. Recorded Future said some campaigns also used stolen or aged domains to blend in and reduce suspicion.
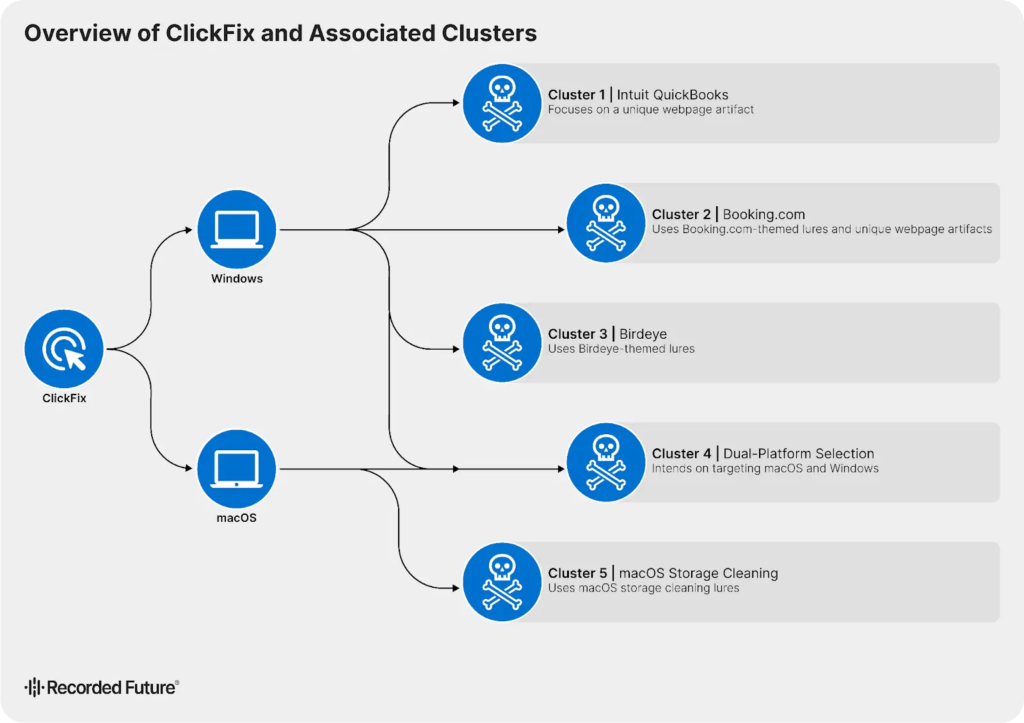
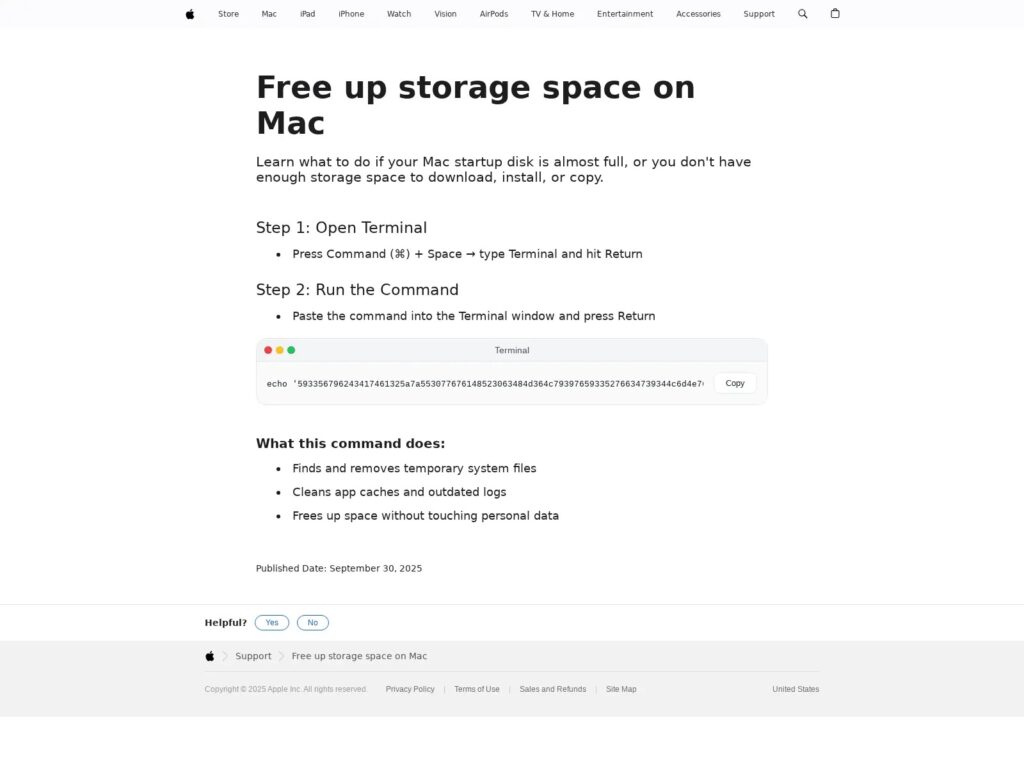
The macOS side used a similar playbook with different tooling. Recorded Future said one cluster impersonated Apple support and pushed a command that decoded layers of data before using zsh to pull and run MacSync, an information stealer. Another cluster checked the victim’s operating system first and then served platform-specific commands, which shows how these campaigns now adapt more carefully to the target environment.
Why ClickFix keeps growing
This technique works because it abuses trust rather than breaking security controls outright. Microsoft said ClickFix campaigns often begin with phishing, malicious ads, or compromised websites, then rely on a fake verification step to insert the user into the infection chain. That user action can help attackers bypass some automated defenses that would normally flag a direct exploit or dropped executable.
Recorded Future’s findings also suggest that ClickFix is no longer a niche trick. The firm said the method has matured into a reusable template that multiple threat actors can adopt quickly, with changes focused mostly on branding, infrastructure, and delivery themes rather than on the core execution flow. Insikt Group said it expects ClickFix to remain a primary initial access method through 2026.
Microsoft’s recent threat research backs that up. Over the past year, Microsoft has tied ClickFix-style delivery to Booking.com impersonation campaigns, CrashFix activity, and broader malware distribution chains that use native tools to stay below the radar.
Malware seen in these campaigns
Recorded Future said the ClickFix clusters it tracked delivered several malware families, including:
- NetSupport RAT
- Odyssey Stealer
- Lumma Stealer
- MacSync
These payloads can support remote control, credential theft, browser data theft, and cryptocurrency wallet harvesting, depending on the campaign and final malware family. Microsoft has separately warned that modern infostealers increasingly target both Windows and macOS, often using native tools, fileless execution, and trusted platforms to avoid detection.
ClickFix campaign summary
| Area | Verified details |
|---|---|
| Main technique | Fake verification or CAPTCHA pages that trick users into running commands manually |
| Target platforms | Windows and macOS |
| Tracked clusters | Five distinct clusters in Recorded Future’s March 25 report |
| Common lures | QuickBooks, Booking.com, Birdeye, fake support or verification pages |
| Delivery path | Clipboard-loaded commands pasted into Run, PowerShell, or Terminal |
| Malware observed | NetSupport RAT, Odyssey Stealer, Lumma Stealer, MacSync |
| Main advantage for attackers | User-assisted execution helps bypass many standard browser defenses |
What defenders should do
Security teams should focus on the exact user actions these campaigns exploit, not just on malware signatures.
- Train users to treat any page that asks them to paste a command into Run, PowerShell, or Terminal as malicious by default.
- Restrict or monitor PowerShell use with controls such as AppLocker, Windows Defender Application Control, or similar policy enforcement.
- Review browser, EDR, and SIEM telemetry for suspicious clipboard activity, spawned shells, and downloads initiated by native tools. This is a defensive inference based on the execution pattern described by Recorded Future and Microsoft.
- Limit Terminal access on managed macOS systems where possible and keep endpoint protections current, especially for info-stealer behavior.
- Block or investigate domains and infrastructure tied to known ClickFix clusters as threat intelligence updates arrive.
FAQ
ClickFix is a social engineering technique that tricks users into manually running a malicious command, usually through a fake verification page or CAPTCHA screen.
Yes. Recorded Future said the latest clusters targeted both platforms and used tailored commands for each operating system.
Not in the usual sense. ClickFix usually relies on deception and user action rather than exploiting a software flaw directly.
Recorded Future listed NetSupport RAT, Odyssey Stealer, Lumma Stealer, and MacSync among the payloads delivered in the clusters it analyzed.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages