Silver Fox shifts from RATs to Python stealers in tax audit phishing campaign across South Asia
A tax-themed phishing campaign tied to Silver Fox has moved away from its earlier reliance on remote access trojans and now uses a custom Python-based stealer in newer attacks. Sekoia says the group, also tracked as Void Arachne, evolved its tooling across three waves between 2025 and 2026 while continuing to impersonate tax authorities to trick victims into downloading malware.
The latest wave appears to focus on credential theft and data collection rather than the deeper foothold commonly associated with ValleyRAT, also known as Winos. According to Sekoia, the newer malware masquerades as a WhatsApp backup tool, communicates with infrastructure styled to look like a WhatsApp web service, and drops clear host artifacts on infected systems.
This matters because the campaign shows how Silver Fox keeps its lure strategy stable while swapping payloads to reduce detection and fit different goals. Sekoia says the group broadened targeting across Taiwan, Japan, Malaysia, India, Indonesia, Singapore, Thailand, and the Philippines, suggesting a wider and more opportunistic operation across South Asia.
How the campaign changed over time
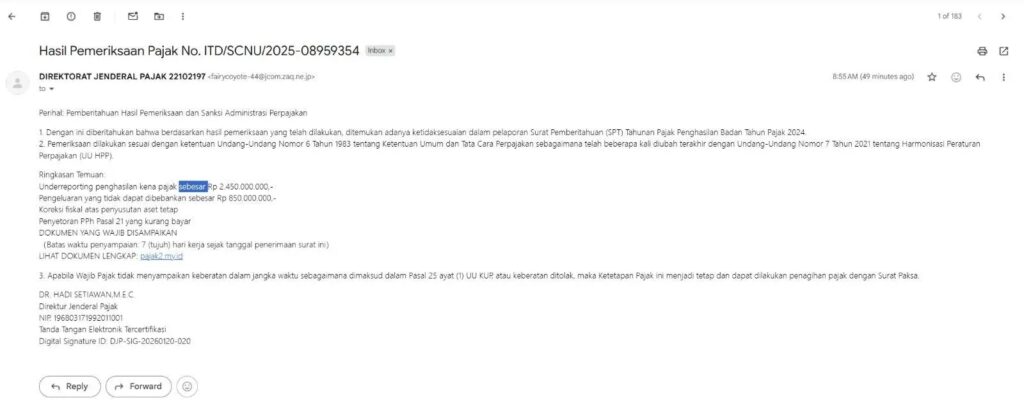
The first wave began in January 2025 and used phishing emails that impersonated Taiwan’s tax authority. Sekoia says the emails carried a malicious PDF that led victims to a ZIP archive containing files used to side-load ValleyRAT. Fortinet separately reported tax-themed lures in Taiwan that delivered Winos 4.0, which supports the broader timeline and the use of official-looking tax notices as bait.
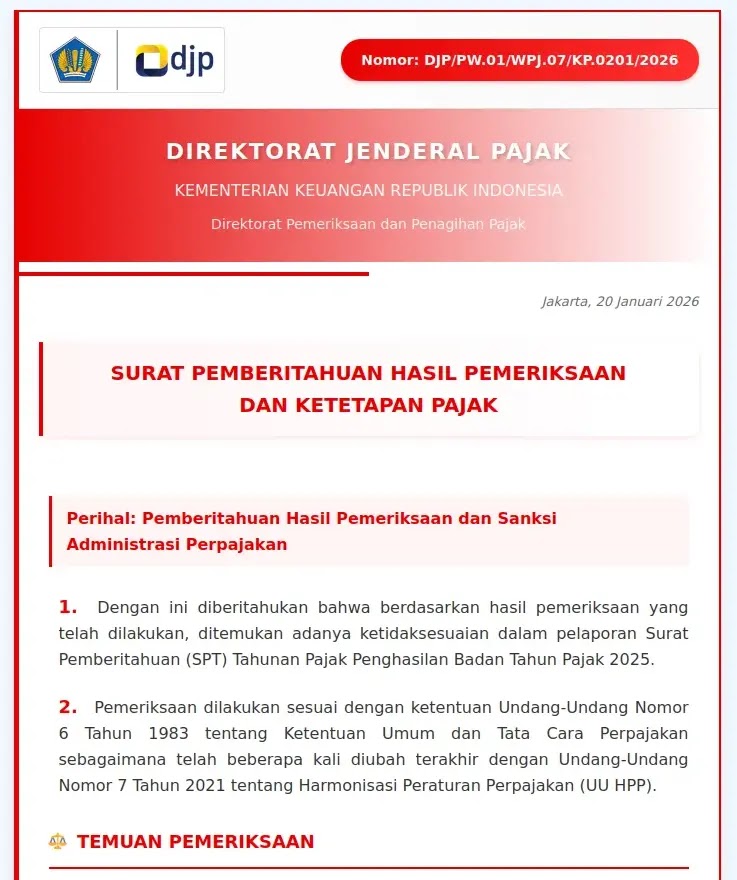
The second wave appeared in mid-December 2025 and expanded to more countries. Instead of attaching a PDF, the attackers sent victims to fake tax websites tailored to local targets. Sekoia says the downloaded archive contained a legitimate but misconfigured Chinese remote monitoring and management tool signed by SyncFutureTec Company Limited, with the command-and-control address embedded in the filename in the format [IPv4]ClientSetup.exe.
By February 2026, the group had replaced that RMM-based approach with a compiled Python stealer. Sekoia says this version targeted Malaysia with a Malay-language phishing site and used the custom User-Agent WhatsAppBackup/1.0 while sending stolen data to xqwmwru[.]top.
What the Python stealer does
Sekoia says the infection starts when a victim clicks a link in a phishing email and lands on a fake tax portal. That site serves a ZIP or RAR archive containing a PE32+ executable, which runs the stealer disguised as a WhatsApp backup application.
Once active, the malware collects credentials, browser data, files, and other sensitive information from the infected machine. Sekoia says the stealer compresses the stolen data and sends it to dedicated upload endpoints, including upload_large.php and upload_status.php, on the attacker-controlled domain.
The malware also leaves recognizable traces behind. Sekoia identified C:\WhatsAppBackup\WhatsAppData.zip and %TEMP%\whatsapp_backup.lock as notable indicators on compromised systems. Those artifacts give defenders a practical way to spot infections during host-based investigations.
Why this shift matters
Silver Fox has long been associated with ValleyRAT and related tooling, but Sekoia says the newer waves look more aligned with broad, profit-driven cybercrime than a narrow espionage operation. The move to an abused RMM tool and then to a straightforward Python stealer suggests the group values speed, flexibility, and lower visibility when running large phishing campaigns.
At the same time, Sekoia says the wider picture remains mixed. The researchers describe Silver Fox as an intrusion set with dual motives, running opportunistic campaigns for financial gain while also showing signs of more advanced, APT-style operations in other cases.
Campaign timeline
| Period | Delivery method | Payload | Main targeting noted |
|---|---|---|---|
| January 2025 | Phishing email with malicious PDF | ValleyRAT / Winos via DLL side-loading | Taiwan, later broader regional overlap |
| Mid-December 2025 | Link to fake tax website | Misconfigured signed Chinese RMM tool | Malaysia, Philippines, Thailand, Indonesia, Singapore, India |
| February 2026 | Link to fake Malay-language tax website | Compiled Python stealer posing as WhatsApp backup | Malaysia, with likely broader regional risk |
Source basis: Sekoia threat research, with Fortinet support for the Taiwan tax-lure stage.
What defenders should watch for
- tax-themed phishing emails that impersonate national revenue or audit authorities
- downloads from fake government tax portals
- executables with embedded IP-style filenames such as
[IPv4]ClientSetup.exe - outbound traffic to
xqwmwru[.]topor related infrastructure - creation of
C:\WhatsAppBackup\WhatsAppData.zip - creation of
%TEMP%\whatsapp_backup.lock - unusual archive downloads followed by a single PE32+ executable launch
What organizations should do now
Security teams should brief finance and accounting staff because tax and audit lures work best on people who regularly handle official filings and compliance messages. Sekoia specifically recommends skepticism toward unsolicited tax emails that contain attachments or download links.
Defenders should also block known malicious domains and review endpoint telemetry for the WhatsAppBackup artifacts tied to the latest wave. On the network side, inspecting connections to new or uncommon domains and hunting for the published infrastructure from the report can help catch related activity before data leaves the environment.
FAQ
Silver Fox, also called Void Arachne, is a China-based intrusion set that Sekoia says has been active since at least 2022 and has blended financially motivated campaigns with more advanced operations.
The group moved from using ValleyRAT and then an abused RMM tool to a custom Python stealer disguised as a WhatsApp backup utility.
Sekoia says the campaign hit Taiwan, Japan, Malaysia, India, Indonesia, Singapore, Thailand, and the Philippines across different waves.
Sekoia highlights C:\WhatsAppBackup\WhatsAppData.zip, %TEMP%\whatsapp_backup.lock, and traffic tied to xqwmwru[.]top as notable indicators from the newest stealer wave.
Yes. Sekoia links the tax-themed waves together and describes them as part of Silver Fox’s evolving toolkit, while Fortinet separately documented Taiwan tax lures delivering Winos 4.0, which is another name for ValleyRAT.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages