Telnyx Python package compromised on PyPI in latest TeamPCP supply chain attack
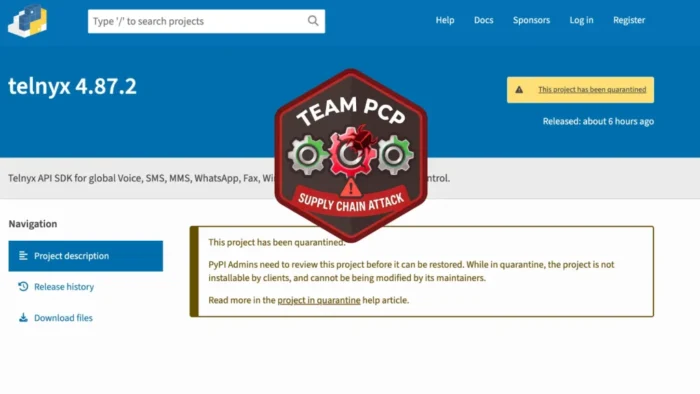
Developers who installed telnyx versions 4.87.1 or 4.87.2 should treat those environments as compromised. Telnyx says the two unauthorized releases contained malicious code and were published to PyPI at 03:51:28 UTC on March 27, 2026, before PyPI quarantined them by 10:13 UTC the same day.
The attack did not hit Telnyx’s core platform. According to the company’s security notice, the incident affected only the Python SDK releases on PyPI, not the Telnyx platform, APIs, or internal infrastructure.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
Security researchers say the compromise fits a wider supply chain campaign linked to TeamPCP, the same threat actor that has already been connected to recent incidents involving Trivy, Checkmarx, and LiteLLM. Independent reporting from Aikido and StepSecurity ties the Telnyx package attack to that same campaign.
How the malicious package worked
Researchers say the malicious code lived inside telnyx/_client.py and ran at import time. That means the payload could trigger as soon as an application or developer imported the package, rather than waiting for a separate installer script or post-install step.
The delivery method also stood out. Analysts say the package fetched payloads hidden inside .wav audio files, a technique designed to make the content look less suspicious to automated inspection tools and content filters.
On Windows, the malware reportedly wrote a file named msbuild.exe into the Startup folder for persistence. On Linux and macOS, researchers say it fetched and ran additional code, then encrypted stolen data before exfiltrating it to attacker-controlled infrastructure.
Why this matters
This was not a fake package pretending to be Telnyx. It was the official telnyx package on PyPI, which made the risk much more serious for teams that update dependencies automatically or do not pin exact versions. Telnyx’s GitHub issue says versions 4.87.1 and 4.87.2 appeared on PyPI without matching GitHub releases or tags, which points to compromised publishing credentials rather than a normal source-code release.
The package also has broad reach. The PyPI page shows Telnyx’s Python library serves as a client for the Telnyx REST API, and the sample article you shared cited 742,000 downloads over the past month, which matches the scale security outlets described around this incident.
For security teams, this attack reinforces a larger problem. Attackers no longer need to trick developers into installing obviously fake libraries when they can compromise trusted release channels and wait for normal update workflows to do the rest. That is the same pattern researchers have described across TeamPCP’s recent campaign.
Affected versions and safe version
| Package | Status |
|---|---|
| telnyx 4.87.1 | Malicious |
| telnyx 4.87.2 | Malicious |
| telnyx 4.87.0 | Last known clean version referenced by Telnyx and researchers |
Source basis for the table: Telnyx’s notice, the GitHub issue, and multiple security write-ups all identify 4.87.1 and 4.87.2 as malicious, while pointing users back to 4.87.0.
What developers and companies should do now
- Check whether any machine, container, or CI pipeline installed
telnyx==4.87.1ortelnyx==4.87.2. - Downgrade or replace those versions with 4.87.0, then pin the version explicitly.
- Rotate API keys, tokens, SSH keys, cloud credentials, and any secrets exposed to affected environments.
- Hunt for suspicious outbound traffic and persistence artifacts, especially where researchers identified the malware’s follow-on behavior.
- Review dependency update controls so production systems do not pull fresh releases automatically without validation. This last point is an inference based on the attack path and the mitigation advice from security researchers.
FAQ
Telnyx says no. The company states that its platform, APIs, and infrastructure were not compromised, and that the issue was limited to the PyPI distribution channel for the Python SDK.
The malicious releases were telnyx 4.87.1 and 4.87.2. Telnyx and the project’s GitHub issue both identify those two versions specifically.
Researchers say the code executed at import time and used payloads hidden inside .wav files. That combination makes the compromise both stealthy and dangerous in automated developer environments.
The last known clean version cited by Telnyx and multiple researchers is 4.87.0.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages