China-linked Red Menshen hides BPFDoor inside telecom networks to spy on governments

A China-linked threat actor has planted stealthy BPFDoor implants inside telecommunications networks to support long-term espionage, including spying paths that can reach government communications. Rapid7 says the campaign involves deep persistence inside critical infrastructure, not quick smash-and-grab access.
The group behind the activity is Red Menshen, which researchers also track as Earth Bluecrow, DecisiveArchitect, and Red Dev 18. Rapid7 says the actor has targeted telecom providers across the Middle East and Asia since at least 2021.
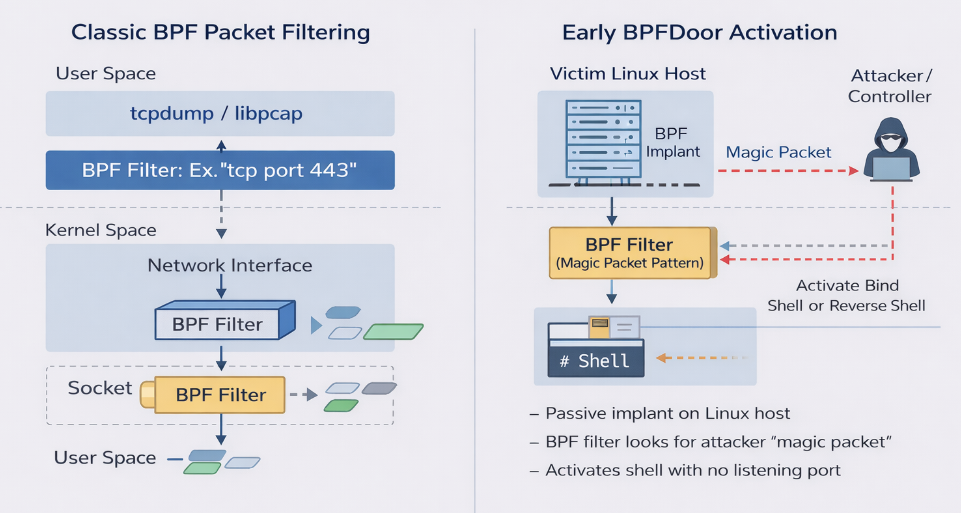
At the center of the campaign sits BPFDoor, a Linux backdoor that works very differently from ordinary malware. Instead of opening a visible port or maintaining a noisy command-and-control channel, it uses Berkeley Packet Filter functionality inside the kernel and wakes up only after receiving a specially crafted trigger packet. The sample article you shared also highlights this stealth model.
Why BPFDoor is so hard to detect
Rapid7 says BPFDoor behaves like a hidden trapdoor inside the operating system. Because it does not keep a normal listener active and does not beacon in obvious ways, traditional endpoint tools can miss it for long periods.
The researchers also found that Red Menshen does not rely on one tool alone. After initial access, the actor has used CrossC2 for post-exploitation, along with Sliver, TinyShell, keyloggers, and brute-force tools to gather credentials and move across networks.
Initial access appears to come through exposed edge systems and internet-facing infrastructure. Rapid7 lists targets such as VPN appliances, firewalls, and web-facing platforms tied to vendors including Ivanti, Cisco, Juniper Networks, Fortinet, VMware, Palo Alto Networks, and Apache Struts.
What makes this telecom campaign especially serious
Rapid7 says some BPFDoor artifacts support SCTP, or Stream Control Transmission Protocol. That matters because SCTP plays a role in telecom signaling, which means the malware may give attackers visibility into subscriber behavior, location data, and telecom-native protocols.
The company also found a newer BPFDoor variant that hides its trigger inside traffic that looks like normal HTTPS. According to Rapid7, the implant checks for the string “9999” at a fixed byte offset, which helps it stay hidden while still recognizing an activation command.
Rapid7 says the controller can also run from inside the victim environment itself. In that mode, it can disguise itself as a legitimate process, trigger implants on internal hosts, and support controlled lateral movement between compromised systems.
Red Menshen telecom espionage at a glance
| Item | Verified detail |
|---|---|
| Threat actor | Red Menshen, also tracked as Earth Bluecrow, DecisiveArchitect, and Red Dev 18 |
| Main malware | BPFDoor, a stealth Linux backdoor that inspects traffic in the kernel |
| Target sector | Telecommunications networks, with espionage implications for government communications |
| Known regions | Middle East and Asia |
| First known activity | Since at least 2021 |
| Evasion updates | HTTPS-hidden trigger logic, fixed offset parsing, ICMP-based host communication |
| Other tools seen | CrossC2, Sliver, TinyShell, keyloggers, brute-force utilities |
Bigger picture for telecom defenders
Rapid7 says this campaign reflects a broader shift in attacker tradecraft. Instead of staying in user space where defenders often look first, adversaries are pushing deeper into kernels, infrastructure layers, and specialized environments such as containerized 4G and 5G core components.
That matches earlier research around BPFDoor activity. Trend Micro reported in 2025 that controllers linked to the backdoor had already been used against telecom, finance, and retail targets across several Asian and Middle Eastern countries, showing that this malware family has operated in sensitive networks for years.
Rapid7 has also released a scanning script to help defenders hunt for BPFDoor implants. Help Net Security reported that the tool aims to help critical infrastructure operators identify implants that can sit quietly inside networks for extended periods.
What security teams should do now
- Audit internet-facing VPN, firewall, and web systems for older exposure and suspicious persistence.
- Hunt for unusual kernel-level packet filtering behavior on Linux systems in telecom environments.
- Review internal lateral movement paths, especially where one compromised host could trigger another.
- Watch for traffic patterns that may conceal activation logic inside otherwise normal HTTPS flows.
- Use the Rapid7 detection guidance and related defensive tooling to scan high-risk infrastructure.
FAQ
BPFDoor is a stealth Linux backdoor that uses Berkeley Packet Filter functionality to inspect traffic at the kernel level and activates only when it receives a specially crafted packet.
Red Menshen is a China-linked threat cluster also known as Earth Bluecrow, DecisiveArchitect, and Red Dev 18. Rapid7 links it to long-term espionage inside telecom networks.
Telecom environments can expose subscriber activity, signaling data, and pathways into government and critical infrastructure communications. Rapid7 says that makes them ideal terrain for low-noise, long-term espionage.
Rapid7 says newer samples can hide activation logic inside HTTPS traffic, support SCTP-aware monitoring, and use lightweight ICMP-based communication between infected hosts.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more




User forum
0 messages