Axios npm packages were compromised in supply chain attack, with malicious code pushed through official releases
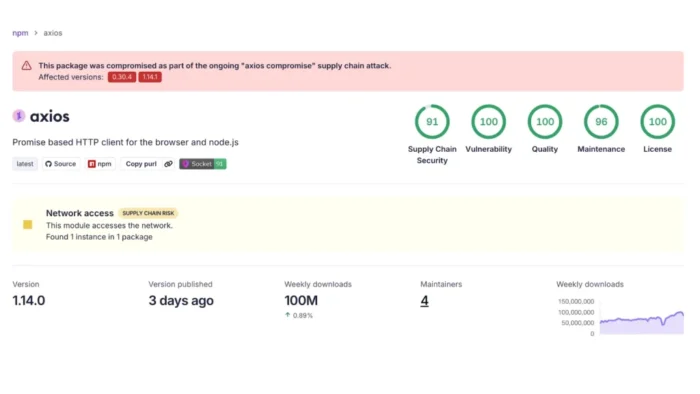
Axios users need to check their projects right away. Security researchers say two real Axios releases, 1.14.1 and 0.30.4, were maliciously published to npm after a maintainer account was likely hijacked, turning one of JavaScript’s most-used HTTP libraries into an active supply chain attack vector.
The poisoned releases pulled in [email protected], a package that researchers at Socket and StepSecurity say contained malicious code. Socket said the dependency deployed a multi-stage payload with remote access trojan behavior, while StepSecurity described it as a cross-platform RAT dropper that targeted Windows, macOS, and Linux.

Access content across the globe at the highest speed rate.
70% of our readers choose Private Internet Access
70% of our readers choose ExpressVPN

Browse the web from multiple devices with industry-standard security protocols.

Faster dedicated servers for specific actions (currently at summer discounts)
This matters because Axios sits deep inside modern web stacks. Snyk lists it as a key ecosystem package with roughly 100 million weekly downloads, and it now warns that the package “was involved in a security incident resulting in compromised versions being published.” Snyk also lists 1.14.0 as the latest non-vulnerable version.
How the Axios compromise happened
Socket said the malicious publish broke Axios’ normal release pattern. The security firm noted that [email protected] and [email protected] appeared on npm without matching GitHub release tags, while v1.14.0 remained the latest visible release in the project’s GitHub repository at the time of reporting.
Researchers say the attacker made only a small change to Axios itself by adding the malicious dependency instead of rewriting large parts of the codebase. That made the compromise harder to notice and let the malicious package execute through npm’s install flow rather than through obvious application logic changes.
Socket’s timeline shows [email protected] was published on March 30, 2026 at 23:59:12 UTC, then flagged by its malware detection at 00:05:41 UTC on March 31. It said [email protected] and [email protected] followed shortly after, poisoning both the current 1.x line and the legacy 0.x line within 39 minutes.
Why developers should treat this as serious
This was not a typosquat or fake lookalike package. Researchers say attackers published malicious versions of the real Axios package through the official npm channel, which means teams that trusted normal semver updates could have pulled the bad release during a routine install. StepSecurity said the hijacked account belonged to primary Axios maintainer jasonsaayman.
Socket also said that anyone using caret ranges like ^1.14.0 or ^0.30.0 could have received the compromised release during the next npm install. That sharply widened the possible blast radius because many JavaScript projects allow patch and minor updates automatically unless teams pin exact versions.
There were also signs of chaos around the maintainers’ access. Socket cited a public GitHub issue where a collaborator said they could not revoke access from the account behind the malicious publish because the attacker’s permissions exceeded theirs. That suggests the incident hit both package publishing and project governance at the same time.
Affected packages
| Package | Malicious version |
|---|---|
| axios | 1.14.1 |
| axios | 0.30.4 |
| plain-crypto-js | 4.2.1 |
What security teams should do now
- Search lockfiles and dependency trees for
[email protected],[email protected], and[email protected]. - Roll back Axios to a known safe version such as
1.14.0where possible. - Assume compromise if the malicious versions were installed and rotate secrets, tokens, and credentials exposed on affected machines. This recommendation follows directly from researchers describing the payload as a RAT-capable installer malware chain.
- Review CI pipelines, feature branches, open pull requests, and caches for transient exposure.
FAQ
Researchers identified [email protected] and [email protected] as the malicious releases. Both pulled in [email protected].
Snyk says 1.14.0 is the latest non-vulnerable version listed on its package page.
The public reporting points more clearly to npm publishing abuse than to a confirmed GitHub source-code compromise. Socket said the malicious releases did not appear in the normal GitHub release tags, which is one reason researchers believe the attacker published outside the standard workflow.
Yes. Any package, build, or application that resolved to the compromised Axios versions could have pulled the malicious dependency during installation. Socket also found related exposure in other packages that bundled or inherited the bad dependency chain.
Read our disclosure page to find out how can you help VPNCentral sustain the editorial team Read more






User forum
0 messages